## Assembly Code Snippet: Bounds-Checked Memory Read with Probe Table
### Overview
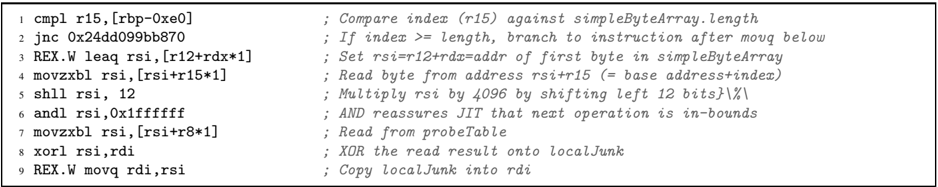
The image displays nine lines of x86-64 assembly code with explanatory comments. The code performs a bounds-checked read from a byte array (`simpleByteArray`), uses the index to perform a lookup in a `probeTable`, and combines the result with a local variable. The comments suggest this is a fragment from a Just-In-Time (JIT) compiler or a low-level system routine, possibly related to security or performance monitoring.
### Components/Axes
The content is structured as a two-column table:
* **Left Column:** Assembly instructions in Intel syntax (destination operand first).
* **Right Column:** Explanatory comments, prefixed by semicolons (`;`).
* **Spatial Layout:** The code is left-aligned. The comments are right-aligned, starting at a consistent horizontal position, creating a clear visual separation between code and documentation.
### Detailed Analysis
The following is a precise transcription of all text in the image, line by line.
**Line 1**
* **Code:** `cmpl r15,[rbp-0xe0]`
* **Comment:** `; Compare index (r15) against simpleByteArray.length`
* **Analysis:** Compares the 32-bit value in register `r15` (acting as an index) with a length value stored on the stack at `[rbp-0xe0]`. The comment identifies this length as belonging to `simpleByteArray`.
**Line 2**
* **Code:** `jnc 0x2dd099bbb70`
* **Comment:** `; If index >= length, branch to instruction after movq below`
* **Analysis:** Conditional jump if Not Carry (CF=0). Following the comparison, this branches if the index (`r15`) is greater than or equal to the length, skipping the subsequent memory read. The target address is a specific memory location.
**Line 3**
* **Code:** `LEA rsi,[r12+rdx*1]`
* **Comment:** `; Set rsi=r12+rdx=addr of first byte in simpleByteArray`
* **Analysis:** Loads the Effective Address into `rsi`. The comment clarifies that `r12+rdx` computes the base address of `simpleByteArray`.
**Line 4**
* **Code:** `movzxb1 rsi, [rsi+r15*1]`
* **Comment:** `; Read byte from address rsi+r15 (= base address+index)`
* **Analysis:** Moves a byte (zero-extended to 64 bits) from the calculated address `[rsi + r15]` into `rsi`. This is the core read from `simpleByteArray[index]`.
**Line 5**
* **Code:** `shll rsi, 12`
* **Comment:** `; Multiply rst by 4096 by shifting left 12 bits}\%\`
* **Analysis:** Shifts the value in `rsi` left by 12 bits, effectively multiplying it by 4096 (2^12). The comment contains a minor typo ("rst" instead of "rsi") and some stray characters (`}\%\`).
**Line 6**
* **Code:** `andl rsi,0x1fffffff`
* **Comment:** `; AND reassures JIT that next operation is in-bounds`
* **Analysis:** Performs a bitwise AND with the mask `0x1fffffff`. The comment indicates this is a safety check to ensure the subsequent address calculation stays within a 512MB (2^29) region, likely for a JIT compiler's memory space.
**Line 7**
* **Code:** `movzxb1 rsi, [rsi+r8*1]`
* **Comment:** `; Read from probeTable`
* **Analysis:** Reads another byte (zero-extended) from the address `[rsi + r8]`. The comment identifies `rsi` (now a scaled index) as an offset into a `probeTable`, with `r8` likely being the base address of that table.
**Line 8**
* **Code:** `xorl rsi,rdi`
* **Comment:** `; XOR the read result onto localJunk`
* **Analysis:** Performs a bitwise XOR between the value in `rsi` (the byte from `probeTable`) and the value in `rdi`. The comment names `rdi` as `localJunk`, suggesting it holds a local, possibly obfuscated, variable.
**Line 9**
* **Code:** `REX.W movq rdi,rsi`
* **Comment:** `; Copy localJunk into rdi`
* **Analysis:** Uses a REX.W prefix to perform a 64-bit move, copying the final result from `rsi` back into `rdi`. The comment confirms `rdi` now holds the updated `localJunk` value.
### Key Observations
1. **Defensive Programming:** The code includes explicit bounds checking (`cmpl`/`jnc`) and an address masking operation (`andl`), indicating it is designed to handle untrusted or variable input safely.
2. **Two-Level Lookup:** It implements a two-step memory access pattern: first reading an index/value from `simpleByteArray`, then using that to perform a second read from a `probeTable`.
3. **Obfuscation/Integration:** The final XOR operation (`xorl rsi,rdi`) merges the result from the `probeTable` with a pre-existing local variable (`localJunk`), which could be for obfuscation, checksumming, or state integration.
4. **JIT Context:** Comments explicitly mention "JIT," strongly suggesting this code is generated or used by a Just-In-Time compiler, possibly for a managed language runtime or a dynamic binary translator.
### Interpretation
This assembly snippet is a low-level implementation of a **safe, indexed probe**. The logical flow is:
1. **Validate:** Ensure an index is within the bounds of a source array (`simpleByteArray`).
2. **Fetch Index:** Read a byte from that array, which serves as a secondary index or selector.
3. **Scale & Constrain:** Scale this secondary index (multiply by 4096) and constrain it to a specific memory region (`0x1fffffff` mask) to form a valid offset.
4. **Probe:** Use this offset to read a byte from a `probeTable` (base in `r8`).
5. **Integrate:** Combine (XOR) the probed value with a local state variable (`localJunk` in `rdi`).
**Purpose & Context:** This pattern is characteristic of **performance profiling, security canaries, or type feedback** in a JIT compiler. The `probeTable` could be storing execution counts, type information, or guard values. The initial read from `simpleByteArray` might be selecting a specific "probe" based on a bytecode index or object type. The final XOR integrates this probe data into the JIT's ongoing analysis or control flow. The careful bounds checking and address masking are critical for maintaining memory safety in a dynamically generated code environment.