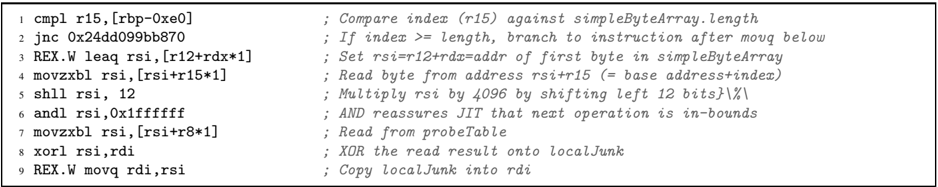
## Code Snippet: Array Bounds Checking and Data Processing
### Overview
This code snippet implements array bounds checking and data processing operations using RISC-V assembly instructions. It includes conditional branching, memory access, arithmetic operations, and bitwise logic to ensure safe array access and data manipulation.
### Components/Axes
- **Registers**:
- `r15`: Index register for array bounds checking
- `rsi`: Base address for array operations
- `rdi`: Destination register for results
- `rdx`: Index multiplier (1)
- **Instructions**:
- `cmp.l`, `j.n.c`, `REX.W`, `movzx.b`, `shl`, `andl`, `xorl`, `REX.W movq`
- **Memory Operations**:
- `simpleByteArray` (source array)
- `probeTable` (destination for XOR results)
### Detailed Analysis
1. **Line 1**: `cmp.l r15, [rbp-0xe0]`
Compares the index (`r15`) against the length of `simpleByteArray` stored at `[rbp-0xe0]`.
2. **Line 2**: `j.n.c 0x24dd099bb870`
Branches to instruction `0x24dd099bb870` if `r15 >= length` (out-of-bounds).
3. **Line 3**: `REX.W leaq rsi, [r12+rdx*1]`
Calculates the address of the first byte in `simpleByteArray` using `r12` (base) and `rdx` (index).
4. **Line 4**: `movzx.b rsi, [rsi+r15*1]`
Reads a byte from `simpleByteArray` at offset `r15` (index) and zero-extends it to 32 bits.
5. **Line 5**: `shl rsi, 12`
Multiplies the read byte by 4096 (2¹²) via left shift.
6. **Line 6**: `andl rsi, 0x1fffffff`
Ensures the result fits within a 32-bit signed integer (JIT bounds check).
7. **Line 7**: `movzx.b rsi, [rsi+r8*1]`
Reads a byte from `probeTable` at offset `r8` (index).
8. **Line 8**: `xorl rsi, rdi`
Performs bitwise XOR between the read byte and `rdi` (localJunk).
9. **Line 9**: `REX.W movq rdi, rsi`
Copies the XOR result back to `rdi` (localJunk).
### Key Observations
- **Bounds Checking**: The `cmp.l` and `j.n.c` instructions prevent out-of-bounds access to `simpleByteArray`.
- **Memory Access**: `movzx.b` and `andl` ensure safe byte-level reads and bounds-checked arithmetic.
- **Bitwise Operations**: `shl` and `xorl` manipulate data for cryptographic or checksum purposes.
- **Register Reuse**: `rsi` and `rdi` are repurposed for intermediate results, typical in RISC-V optimization.
### Interpretation
This code demonstrates a security-conscious implementation of array processing. The bounds check (`cmp.l`/`j.n.c`) prevents buffer overflow vulnerabilities, while the XOR operation (`xorl`) suggests cryptographic or data integrity checks. The use of `probeTable` implies a lookup table for dynamic data processing. The assembly optimizes performance by minimizing memory accesses and leveraging register reuse, critical for low-level systems programming.