\n
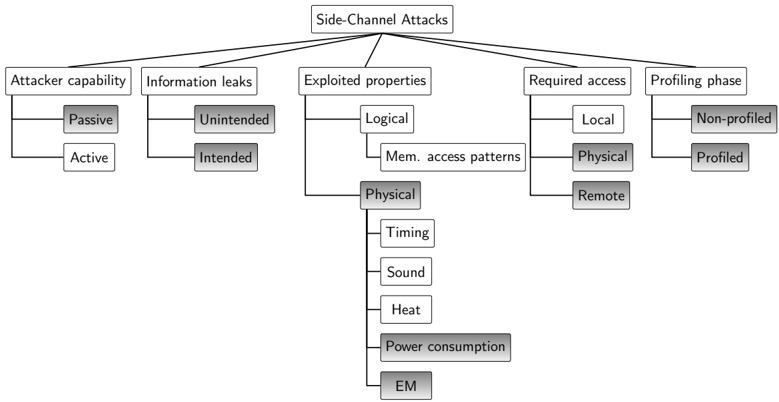
## Diagram: Taxonomy of Side-Channel Attacks
### Overview
The image displays a hierarchical tree diagram (taxonomy) that classifies the various aspects and categories of "Side-Channel Attacks." The diagram is structured with a single root node at the top, branching out into five primary categories, which further subdivide into more specific types or methods. The layout is a top-down tree, with connecting lines indicating parent-child relationships. Several leaf nodes are shaded in gray, potentially indicating a common, significant, or specific subset within their category.
### Components/Axes
**Root Node:**
* **Label:** "Side-Channel Attacks" (Top-center of the diagram)
**Primary Branches (Level 1, from left to right):**
1. **Attacker capability**
2. **Information leaks**
3. **Exploited properties**
4. **Required access**
5. **Profiling phase**
**Sub-categories (Level 2 and beyond):**
* **Under "Attacker capability":**
* Passive (shaded gray)
* Active
* **Under "Information leaks":**
* Unintended (shaded gray)
* Intended
* **Under "Exploited properties":**
* Logical
* Mem. access patterns
* Physical (shaded gray)
* Timing
* Sound
* Heat
* Power consumption (shaded gray)
* EM (shaded gray)
* **Under "Required access":**
* Local
* Physical (shaded gray)
* Remote
* **Under "Profiling phase":**
* Non-profiled
* Profiled (shaded gray)
### Detailed Analysis
The diagram provides a structured breakdown of side-channel attack characteristics:
1. **Attacker Capability:** Differentiates between attacks based on the attacker's interaction level. "Passive" attacks only observe side-channel emissions, while "Active" attacks may involve injecting signals or faults.
2. **Information Leaks:** Classifies the nature of the information leakage. "Unintended" leaks are incidental byproducts of computation, whereas "Intended" leaks might refer to scenarios where a system is designed to leak information in a controlled manner (e.g., for debugging), which can be exploited.
3. **Exploited Properties:** This is the most detailed branch, categorizing the physical or logical phenomena an attack leverages.
* **Logical:** Exploits patterns in software/hardware behavior, specifically "Mem. access patterns" (e.g., cache timing attacks).
* **Physical:** Exploits measurable physical emanations. The sub-categories list specific channels: "Timing" (execution time variations), "Sound" (acoustic emissions), "Heat" (thermal output), "Power consumption" (variations in electrical power draw), and "EM" (electromagnetic emissions).
4. **Required Access:** Specifies the level of proximity or access needed to perform the attack. "Local" implies access to the same operating system or virtual machine, "Physical" requires being near the hardware, and "Remote" can be conducted over a network.
5. **Profiling Phase:** Indicates whether the attack requires a preliminary phase to build a model or profile of the target system's behavior. "Non-profiled" attacks work without this step, while "Profiled" attacks depend on it.
**Spatial Grounding & Shading:** The legend is implicit through the tree structure and shading. The gray shading is applied to specific leaf nodes across different branches: "Passive," "Unintended," "Physical" (under Exploited properties), "Power consumption," "EM," "Physical" (under Required access), and "Profiled." This visual cue likely highlights a common or canonical subset of side-channel attack characteristics.
### Key Observations
* **Comprehensive Taxonomy:** The diagram covers the attack lifecycle from attacker capabilities and required access to the specific physical phenomena exploited and the methodology (profiling).
* **Emphasis on Physical Channels:** The "Exploited properties -> Physical" branch is the most granular, listing five distinct measurable channels (Timing, Sound, Heat, Power consumption, EM), indicating the breadth of physical side-channels.
* **Shading Pattern:** The shaded items do not form a single coherent path but represent a selection across categories. For example, a common attack profile might be: a **Passive** attacker, exploiting an **Unintended** leak, using a **Physical** property (like **Power consumption** or **EM**), requiring **Physical** access, and employing a **Profiled** methodology.
### Interpretation
This diagram serves as a conceptual framework for understanding, categorizing, and potentially defending against side-channel attacks. It moves beyond a simple list of attacks (like "Power Analysis" or "Cache Timing") to deconstruct them into their fundamental components.
* **Relationships:** The tree structure shows that a single side-channel attack can be described by a combination of attributes from each primary branch (e.g., a "Passive, Unintended, Timing-based, Remote, Non-profiled" attack).
* **Defensive Implications:** By breaking down attacks into these categories, defenders can develop more targeted countermeasures. For instance, mitigations for "Logical" property attacks (like constant-time programming) differ fundamentally from those for "Physical" property attacks (like electromagnetic shielding or power noise injection).
* **Notable Insight:** The inclusion of "Intended" information leaks is particularly insightful. It suggests that side-channel vulnerabilities can arise not only from accidental physical emanations but also from deliberate system behaviors that are misused, broadening the scope of what constitutes a side-channel.
* **Underlying Principle:** The entire taxonomy underscores the core principle of side-channel attacks: they exploit the *correlation* between a system's secret-dependent internal state and its observable, macroscopic behavior (whether logical or physical), without breaking the primary cryptographic or security mechanism itself.