## Diagram: Side-Channel Attacks Classification
### Overview
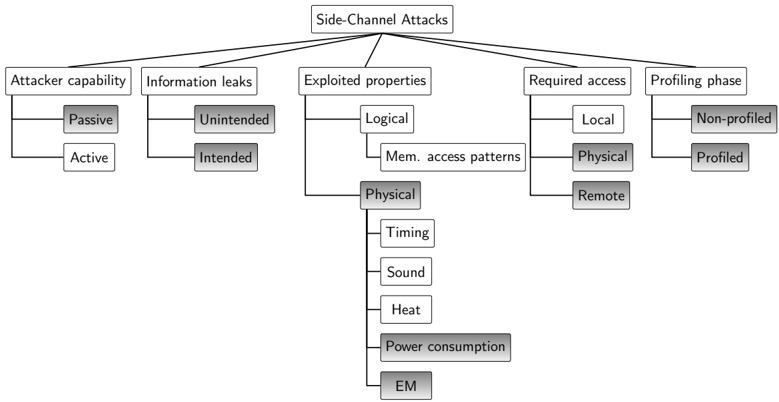
The image is a tree diagram illustrating the classification of side-channel attacks. The diagram branches out from the central topic, "Side-Channel Attacks," into five main categories: "Attacker capability," "Information leaks," "Exploited properties," "Required access," and "Profiling phase." Each of these categories further branches into subcategories, providing a hierarchical breakdown of the different aspects of side-channel attacks.
### Components/Axes
* **Main Topic:** Side-Channel Attacks (located at the top center)
* **First-Level Categories:**
* Attacker capability (top-left)
* Information leaks (left-center)
* Exploited properties (center)
* Required access (right-center)
* Profiling phase (top-right)
* **Second-Level and Third-Level Subcategories:** These are listed below under "Detailed Analysis."
### Detailed Analysis
The diagram breaks down each main category as follows:
* **Attacker capability:**
* Passive (gray box)
* Active (white box)
* **Information leaks:**
* Unintended (gray box)
* Intended (white box)
* **Exploited properties:**
* Logical (white box)
* Mem. access patterns (white box)
* Physical (gray box)
* Timing (white box)
* Sound (white box)
* Heat (white box)
* Power consumption (gray box)
* EM (gray box)
* **Required access:**
* Local (white box)
* Physical (gray box)
* Remote (gray box)
* **Profiling phase:**
* Non-profiled (gray box)
* Profiled (white box)
### Key Observations
* The diagram uses a hierarchical structure to categorize side-channel attacks.
* Some subcategories are further divided (e.g., "Exploited properties" -> "Physical" -> "Timing," "Sound," "Heat," "Power consumption," "EM").
* The use of gray and white boxes may indicate different types or levels of classification, but this is not explicitly defined in the diagram.
### Interpretation
The diagram provides a structured overview of the various dimensions of side-channel attacks. It highlights the different capabilities an attacker might possess, the types of information that can be leaked, the properties of the system that can be exploited, the level of access required, and whether the attack involves a profiling phase. The hierarchical structure allows for a detailed understanding of the relationships between these different aspects of side-channel attacks. The diagram suggests that side-channel attacks can be classified based on multiple factors, providing a comprehensive framework for analysis and mitigation. The use of gray and white boxes may indicate a binary classification within each category, but without a legend, the exact meaning is unclear.