\n
## Diagram: Side-Channel Attacks Taxonomy
### Overview
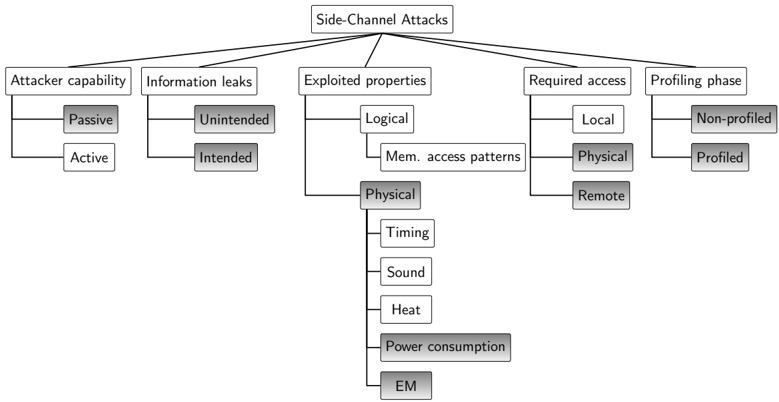
The image is a hierarchical diagram illustrating a taxonomy of Side-Channel Attacks. The diagram branches out from the central topic "Side-Channel Attacks" into five main categories: "Attacker capability", "Information leaks", "Exploited properties", "Required access", and "Profiling phase". Each of these categories further branches into sub-categories, providing a detailed classification of different types of side-channel attacks.
### Components/Axes
The diagram is structured as a tree, with the root node at the top center and branches extending downwards. There are no axes in the traditional sense, but the diagram uses hierarchical relationships to organize information. The main categories are positioned horizontally, and their sub-categories are arranged vertically below them.
### Detailed Analysis or Content Details
Here's a breakdown of each branch:
1. **Attacker capability:**
* Passive
* Active
2. **Information leaks:**
* Unintended
* Intended
3. **Exploited properties:**
* Logical
* Mem. access patterns (Memory access patterns)
* Physical
* Timing
* Sound
* Heat
* Power consumption
* EM (Electromagnetic)
4. **Required access:**
* Local
* Physical
* Remote
5. **Profiling phase:**
* Non-profiled
* Profiled
### Key Observations
The diagram demonstrates a comprehensive categorization of side-channel attacks. The "Exploited properties" branch is the most detailed, with several sub-categories under "Physical" attacks. The diagram highlights the different aspects of side-channel attacks, from the attacker's capabilities to the properties exploited and the access level required.
### Interpretation
This diagram serves as a foundational understanding of the landscape of side-channel attacks. It suggests that these attacks can be classified based on various factors, allowing for a more targeted analysis and defense strategy. The distinction between "Passive" and "Active" attacker capabilities indicates the level of interaction the attacker has with the system. The categorization of "Information leaks" into "Unintended" and "Intended" highlights whether the information leakage is a flaw or a deliberate feature. The detailed breakdown of "Exploited properties" shows the diverse range of physical phenomena that can be exploited to extract sensitive information. The "Required access" categories indicate the level of control the attacker needs to launch the attack. Finally, the "Profiling phase" categorization suggests whether the attacker has prior knowledge of the system's behavior.
The diagram is a useful tool for security professionals and researchers to understand the different types of side-channel attacks and develop appropriate countermeasures. It provides a clear and concise overview of the field, making it easier to navigate the complex landscape of side-channel security.