## Diagram: Side-Channel Attacks Classification
### Overview
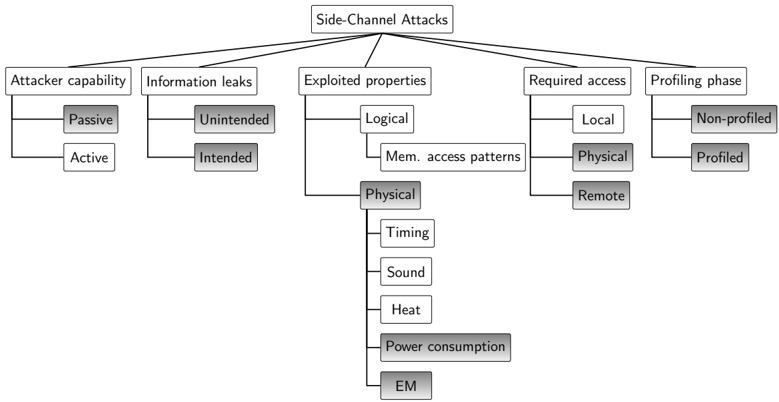
The diagram illustrates a hierarchical taxonomy of side-channel attacks, categorizing them based on attacker capabilities, exploited properties, required access, and profiling phases. It emphasizes physical and logical attack vectors, with subdivisions into passive/active, unintended/intended, and non-profiled/profiled methodologies.
### Components/Axes
1. **Main Categories**:
- Attacker capability
- Information leaks
- Exploited properties
- Required access
- Profiling phase
2. **Subcategories**:
- **Attacker capability**: Passive, Active
- **Information leaks**: Unintended, Intended
- **Exploited properties**: Logical, Physical (Timing, Sound, Heat, Power consumption, EM)
- **Required access**: Local, Remote
- **Profiling phase**: Non-profiled, Profiled
3. **Spatial Structure**:
- Root node: "Side-Channel Attacks" (center-top)
- Branches radiate downward, with subcategories nested under parent nodes.
- Physical properties (e.g., Timing, Power consumption) are grouped under "Exploited properties."
- Profiling phase splits into Non-profiled (left) and Profiled (right).
### Detailed Analysis
- **Attacker capability**:
- Passive: Observes without interaction (e.g., eavesdropping).
- Active: Engages with the system (e.g., injecting probes).
- **Information leaks**:
- Unintended: Accidental data exposure (e.g., cache timing attacks).
- Intended: Deliberate data leakage (e.g., fault injection).
- **Exploited properties**:
- Logical: Exploits computational logic (e.g., power analysis of cryptographic operations).
- Physical: Uses measurable physical phenomena:
- Timing: Delays in operations (e.g., cache access times).
- Sound: Acoustic emissions from hardware.
- Heat: Thermal imaging of device activity.
- Power consumption: Voltage fluctuations during computation.
- EM: Electromagnetic radiation analysis.
- **Required access**:
- Local: Physical proximity to the target (e.g., USB port access).
- Remote: Network-based access (e.g., Wi-Fi side-channel attacks).
- **Profiling phase**:
- Non-profiled: Generic attacks without prior knowledge of the target.
- Profiled: Tailored attacks using specific target data (e.g., user-specific encryption keys).
### Key Observations
1. **Hierarchical Relationships**:
- Physical properties are a major subset of exploited properties, indicating their prominence in side-channel attacks.
- Profiling phase bifurcates the attack strategy into generic vs. targeted approaches.
- Required access (Local/Remote) determines the attacker's proximity to the target.
2. **Notable Patterns**:
- Physical attacks dominate the taxonomy, with five distinct subcategories (Timing, Sound, Heat, Power, EM).
- Passive and Active attacker capabilities are mutually exclusive but both critical to understanding attack feasibility.
3. **Anomalies**:
- "Intended information leaks" may overlap with "Exploited properties," suggesting deliberate design flaws as attack vectors.
- "Non-profiled" attacks lack specificity, contrasting with "Profiled" attacks that require prior intelligence.
### Interpretation
This diagram underscores the multifaceted nature of side-channel attacks, emphasizing their reliance on physical and logical properties rather than direct system vulnerabilities. The classification highlights:
- **Attacker Strategy**: Passive methods (e.g., eavesdropping) vs. Active methods (e.g., injecting faults) depend on the attacker's resources and access.
- **Target Characteristics**: Local attacks require physical proximity, while Remote attacks exploit network vulnerabilities.
- **Attack Specificity**: Profiled attacks (e.g., using user-specific data) are more targeted but require prior intelligence, whereas Non-profiled attacks are broader but less effective.
The taxonomy reflects the evolution of side-channel attacks from theoretical exploits (e.g., timing analysis) to practical, real-world threats (e.g., EM-based cryptanalysis). The emphasis on Physical properties suggests that hardware-level vulnerabilities remain a critical focus for mitigation strategies.