## Diagram: Compression-Based Side-Channel Attack Flow
### Overview
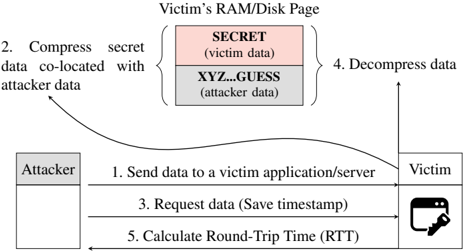
The image is a technical diagram illustrating a multi-step side-channel attack that exploits data compression to infer a victim's secret information. The attack leverages the fact that compressing data containing known patterns (attacker data) alongside unknown secret data results in a smaller output size if the secret contains matching patterns. By measuring the round-trip time (RTT) of data requests, the attacker can deduce information about the secret.
### Components/Axes
The diagram is composed of two primary actors and a shared memory space, connected by a numbered sequence of actions.
**Actors:**
* **Attacker:** Represented by a box on the left side of the diagram.
* **Victim:** Represented by a box on the right side of the diagram, which includes a lock icon, suggesting a secured application or server.
**Shared Memory Space (Top Center):**
* **Label:** `Victim's RAM/Disk Page`
* This space is divided into two co-located data blocks:
1. **Top Block (Pink):** `SECRET (victim data)`
2. **Bottom Block (Gray):** `XYZ_GUESS (attacker data)`
**Attack Flow (Numbered Steps):**
The process is depicted with arrows indicating the direction of actions and data flow between the Attacker and Victim.
### Detailed Analysis
The attack proceeds through five distinct, numbered steps:
1. **Step 1 (Attacker → Victim):** `Send data to a victim application/server`
* The attacker initiates the process by sending data (presumably the `XYZ_GUESS` data) to the victim's system.
2. **Step 2 (Internal to Victim's System):** `Compress secret data co-located with attacker data`
* An arrow points from the "Victim's RAM/Disk Page" to the compression step. This indicates that the victim's system compresses the memory page containing both the `SECRET` and the attacker's `XYZ_GUESS` data together.
3. **Step 3 (Attacker → Victim):** `Request data (Save timestamp)`
* The attacker requests the compressed data back from the victim. Crucially, the attacker saves a timestamp at the moment this request is sent.
4. **Step 4 (Internal to Victim's System):** `Decompress data`
* An arrow points from the compression step back to the "Victim's RAM/Disk Page," indicating the victim decompresses the data to serve the request.
5. **Step 5 (Victim → Attacker):** `Calculate Round-Trip Time (RTT)`
* The attacker receives the response and calculates the RTT by comparing the current time with the saved timestamp from Step 3.
### Key Observations
* **Spatial Grounding:** The legend/data (`SECRET` and `XYZ_GUESS`) is centrally located at the top. The attack flow is a linear sequence from left (Attacker) to right (Victim) and back, with internal processing steps shown above the main flow line.
* **Core Mechanism:** The critical component is **Step 2**. The efficiency of compressing the combined `SECRET` and `XYZ_GUESS` data depends on the similarity between them. If the attacker's guess (`XYZ`) matches part of the secret, the combined data will have more redundancy, leading to better compression (a smaller file size).
* **Data Exfiltration Method:** The secret is not exfiltrated directly. Instead, information is leaked through a **timing side-channel**. A smaller compressed file size (due to a good guess) results in a faster transfer and a **shorter RTT** measured in Step 5. The attacker repeats this process with different guesses (`XYZ`), using RTT variations to infer the secret's content.
### Interpretation
This diagram details a **compression-based side-channel attack**, a sophisticated method of information leakage. It demonstrates how an attacker can exploit a system's optimization process (compression) to gain covert knowledge.
* **What the data suggests:** The attack is feasible when an attacker can place their own data (`XYZ_GUESS`) into the same memory or storage page as a victim's secret data (`SECRET`) before a compression operation occurs. This is a common scenario in shared cloud environments, certain file systems, or web servers compressing cached data.
* **Relationship between elements:** The attack creates a feedback loop. The attacker's input (`XYZ_GUESS`) influences a system process (compression), the outcome of which (compressed size) is reflected in a measurable system property (RTT). The RTT measurement acts as an oracle, telling the attacker how "good" their guess was.
* **Notable implications:** This attack vector is particularly concerning because it bypasses many traditional security boundaries. Encryption alone does not prevent it, as the attack targets the compression step that often occurs *before* encryption. Mitigation requires careful system design, such as ensuring attacker-controlled data cannot be co-located with secrets before compression, using constant-time algorithms, or disabling compression on sensitive data streams. The diagram serves as a clear blueprint for understanding this class of vulnerability.