## Dual-Axis Combination Chart: Stealthiness vs. Detection Likelihood and ASR
### Overview
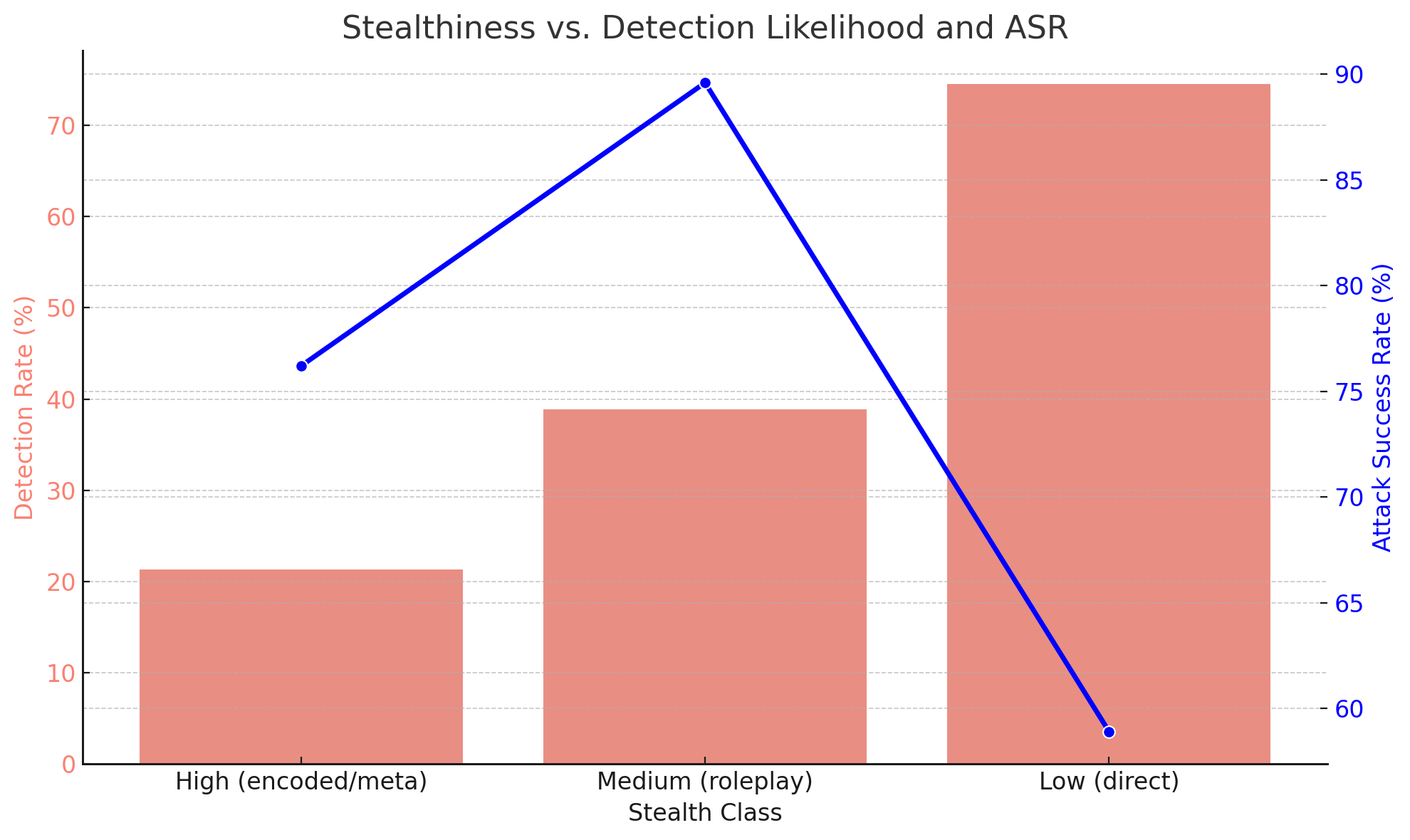
This is a dual-axis combination chart that visualizes the relationship between the stealthiness of an attack method (categorized into three classes) and two key metrics: the Detection Rate (as a percentage) and the Attack Success Rate (ASR, as a percentage). The chart demonstrates a clear trade-off between how stealthy an attack is and its likelihood of being detected versus its likelihood of succeeding.
### Components/Axes
* **Chart Title:** "Stealthiness vs. Detection Likelihood and ASR"
* **X-Axis (Horizontal):**
* **Label:** "Stealth Class"
* **Categories (from left to right):**
1. "High (encoded/meta)"
2. "Medium (roleplay)"
3. "Low (direct)"
* **Primary Y-Axis (Left, Vertical):**
* **Label:** "Detection Rate (%)"
* **Scale:** Linear, from 0 to 70, with major gridlines at intervals of 10.
* **Data Representation:** Salmon-colored bars.
* **Secondary Y-Axis (Right, Vertical):**
* **Label:** "Attack Success Rate (%)"
* **Scale:** Linear, from 60 to 90, with major gridlines at intervals of 5.
* **Data Representation:** A solid blue line with circular data points.
* **Legend:** Not explicitly present. The data series are distinguished by color and chart type (bars vs. line), with their corresponding axes labeled directly.
### Detailed Analysis
**Data Series 1: Detection Rate (Salmon Bars)**
* **Trend Verification:** The height of the bars increases sharply from left to right, indicating that detection likelihood rises as stealth decreases.
* **Data Points (Approximate):**
* **High (encoded/meta) Stealth:** ~21%
* **Medium (roleplay) Stealth:** ~39%
* **Low (direct) Stealth:** ~75%
**Data Series 2: Attack Success Rate (Blue Line)**
* **Trend Verification:** The line slopes upward from the first to the second data point, then slopes steeply downward to the third point, forming an inverted "V" shape. This indicates ASR peaks at medium stealth.
* **Data Points (Approximate):**
* **High (encoded/meta) Stealth:** ~76%
* **Medium (roleplay) Stealth:** ~90%
* **Low (direct) Stealth:** ~59%
### Key Observations
1. **Inverse Relationship (Detection vs. Stealth):** There is a strong inverse relationship between stealth and detection. The "Low (direct)" attack class is detected at a rate (~75%) more than 3.5 times higher than the "High (encoded/meta)" class (~21%).
2. **Optimal Stealth for Success:** The "Medium (roleplay)" stealth class achieves the highest Attack Success Rate (~90%), despite having a moderate detection rate (~39%). This suggests a "sweet spot" where the attack is complex enough to evade some detection but not so complex that it hinders its own execution.
3. **High Stealth Trade-off:** While "High (encoded/meta)" stealth is the hardest to detect (~21%), its Attack Success Rate (~76%) is significantly lower than the medium class. This implies that highly encoded or meta-level attacks may be less reliable or effective, even if they are stealthier.
4. **Low Stealth Penalty:** "Low (direct)" attacks are the easiest to detect (~75%) and also have the lowest success rate (~59%), making them the least effective strategy overall.
### Interpretation
This chart illustrates a fundamental security trade-off in adversarial attacks (likely against AI systems, given terms like "roleplay" and "encoded/meta"). The data suggests that **moderate stealth ("roleplay") is the most effective strategy**, balancing evasion of detection with operational effectiveness.
* **High Stealth (Encoded/Meta):** These attacks prioritize evasion, possibly using complex encoding or operating at a meta-level. The cost is reduced reliability or potency, leading to a lower success rate despite high stealth.
* **Medium Stealth (Roleplay):** This class likely involves attacks framed within a narrative or persona. It represents an optimal balance: it is obfuscated enough to avoid immediate detection by many systems but remains direct enough to execute its payload reliably, resulting in peak success.
* **Low Stealth (Direct):** These are overt, unobfuscated attacks. They are easily flagged by security systems (high detection rate) and, once detected, are obviously malicious, leading to a low success rate.
The overarching implication for defense is that detection systems are most challenged by moderately stealthy, context-aware attacks (like roleplay) rather than purely direct or overly complex encoded ones. For attackers, the data argues against pursuing maximum stealth at all costs, as it can undermine the attack's primary goal. The most dangerous threats are those that are just stealthy enough.