## Diagram: Secure Multi-Party Computation for Feature Similarity
### Overview
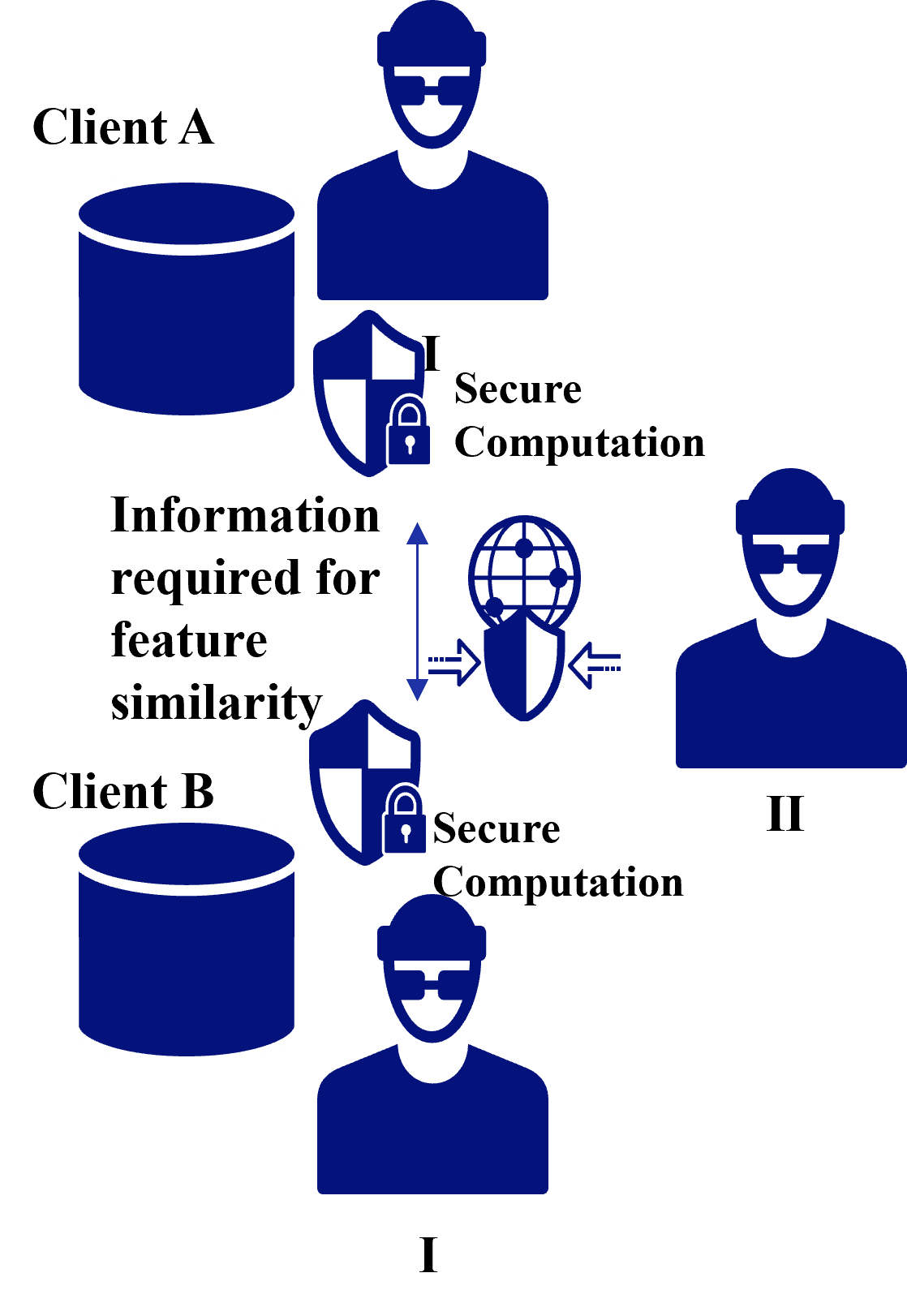
The image is a conceptual diagram illustrating a secure computation protocol between two distinct clients (Client A and Client B) to determine feature similarity without directly sharing their underlying data. The process involves local secure computation at each client and a mediated, secure exchange of information through a central entity.
### Components/Axes
The diagram is composed of several key visual components, all rendered in a dark blue color on a light gray background.
**1. Client Entities:**
* **Client A (Top-Left):** Represented by a person icon (labeled "I") and a cylindrical database icon.
* **Client B (Bottom-Left):** Represented by a person icon (labeled "I") and a cylindrical database icon.
* **Central Entity (Right):** Represented by a person icon (labeled "II") and a composite icon of a globe overlaid with a shield.
**2. Process Labels & Icons:**
* **"Secure Computation" (Appears twice):** This text is placed next to a shield icon containing a padlock. One instance is positioned between Client A's database and the central entity. The second instance is positioned between Client B's database and the central entity.
* **"Information required for feature similarity" (Center-Left):** This block of text describes the data being exchanged. It is connected by a vertical, double-headed arrow to the central globe/shield icon.
* **Shield with Padlock Icon:** Appears twice, associated with the "Secure Computation" label for each client.
* **Globe with Shield Icon (Center-Right):** Represents the central, secure communication or computation channel. It has two horizontal, dashed arrows pointing inward from the left and right, indicating bidirectional data flow into this secure channel.
**3. Labels:**
* **"I" (Roman Numeral):** Appears below the person icon for Client A and below the person icon for Client B.
* **"II" (Roman Numeral):** Appears below the person icon for the central entity on the right.
### Detailed Analysis
The diagram depicts a specific workflow:
1. **Local Processing:** Both Client A and Client B perform "Secure Computation" on their own local data (represented by their respective databases). This is indicated by the shield/padlock icon next to each client's data store.
2. **Information Exchange:** The core requirement for the process is identified as "Information required for feature similarity." This information is not the raw data itself but a derived, secure representation.
3. **Secure Mediation:** This required information is exchanged through a central, secure channel represented by the globe/shield icon. The dashed arrows pointing into this icon from both sides signify that both clients contribute information to this secure environment.
4. **Role Distinction:** The labels "I" and "II" suggest a distinction in roles. Clients A and B are both role "I" (data holders/participants), while the entity on the right is role "II" (likely a coordinator, aggregator, or trusted execution environment).
### Key Observations
* **Symmetry:** The setup for Client A and Client B is visually symmetrical, indicating they perform analogous roles in the protocol.
* **Security Emphasis:** The repeated use of shield and padlock icons, along with the explicit label "Secure Computation," highlights that privacy and data security are the primary concerns of this architecture.
* **Abstraction:** The diagram is high-level and abstract. It does not specify the cryptographic techniques (e.g., homomorphic encryption, secure multi-party computation, federated learning) used to achieve "Secure Computation."
* **Data Flow:** The flow is not directly between Client A and Client B. Instead, both clients interact with a central secure entity (II), which likely facilitates the computation without having access to the raw data.
### Interpretation
This diagram illustrates a privacy-preserving framework for collaborative data analysis. The core problem it solves is how two parties (Client A and B) can jointly compute a similarity metric on their respective feature sets without revealing the sensitive raw data to each other or to a central server.
The "Information required for feature similarity" is the critical, privacy-protected output of each client's local secure computation. This could be encrypted data, model gradients, or other cryptographic shares. The central entity (II) acts as a secure aggregator or computation node that combines these protected inputs to calculate the final similarity result.
The architecture suggests a scenario common in fields like healthcare (comparing patient data across hospitals), finance (fraud detection across banks), or competitive business analytics, where collaboration is valuable but data sharing is restricted by regulation, privacy, or competition. The diagram emphasizes a solution where trust is minimized through cryptographic security ("Secure Computation") and a structured, mediated communication flow.