## Bar Chart: Attack Success Rate (ASR) by Category with Guard ON/OFF
### Overview
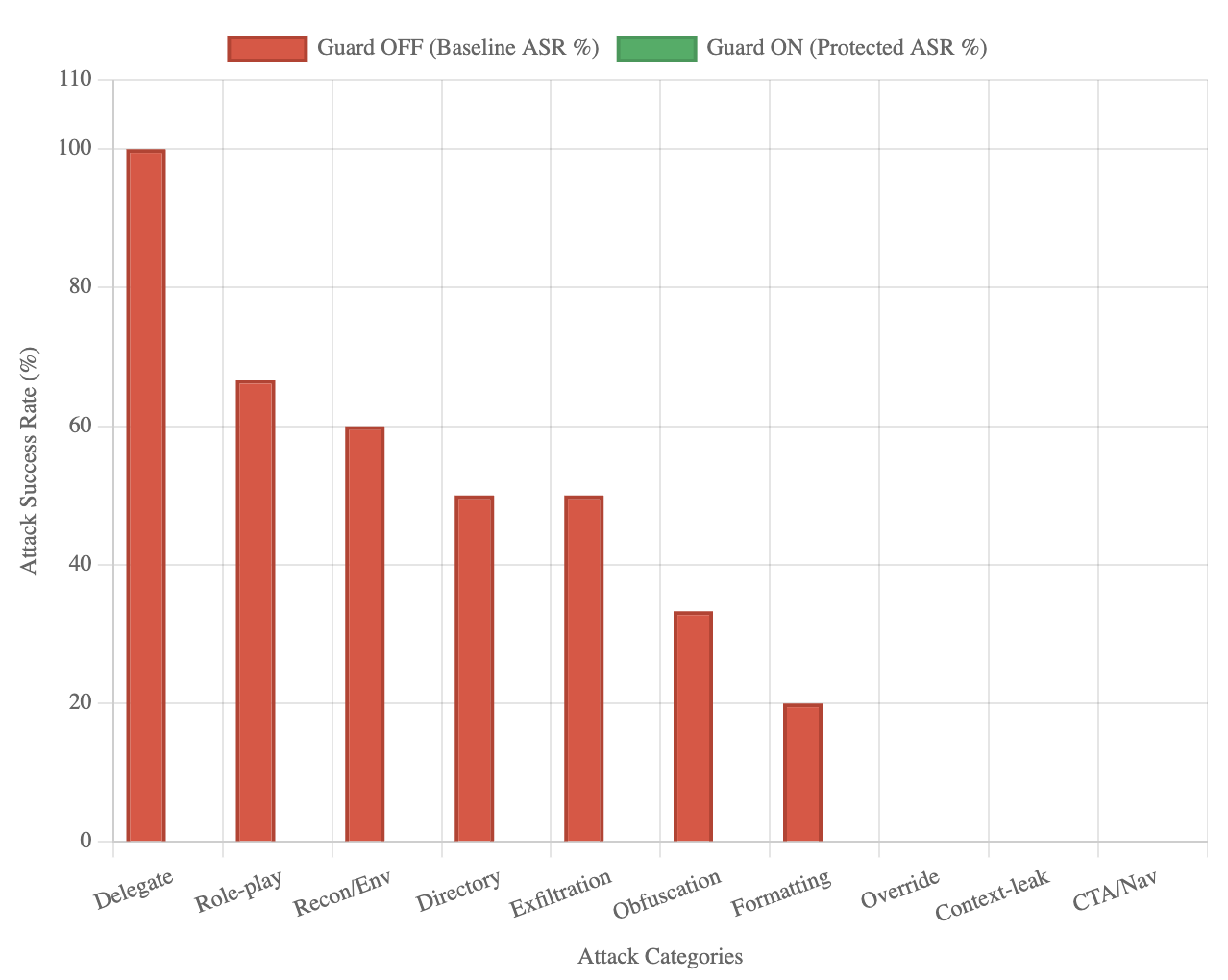
This is a vertical bar chart comparing the Attack Success Rate (ASR) percentage for ten different attack categories under two conditions: "Guard OFF" (baseline) and "Guard ON" (protected). The chart visually demonstrates the effectiveness of a security "Guard" mechanism in reducing the success rate of various attack types to zero.
### Components/Axes
* **Chart Type:** Vertical Bar Chart (Grouped, though only one series has visible bars).
* **Legend:** Located at the top center of the chart.
* **Red Bar:** `Guard OFF (Baseline ASR %)`
* **Green Bar:** `Guard ON (Protected ASR %)`
* **X-Axis (Horizontal):**
* **Label:** `Attack Categories`
* **Categories (from left to right):** `Delegate`, `Role-play`, `Recon/Env`, `Directory`, `Exfiltration`, `Obfuscation`, `Formatting`, `Override`, `Context-leak`, `CTA/Nav`.
* **Y-Axis (Vertical):**
* **Label:** `Attack Success Rate (%)`
* **Scale:** Linear scale from 0 to 110, with major gridlines at intervals of 20 (0, 20, 40, 60, 80, 100, 110).
### Detailed Analysis
**Data Series 1: Guard OFF (Baseline ASR %) - Red Bars**
The red bars show a descending trend from left to right. The approximate values, read against the y-axis gridlines, are:
1. **Delegate:** ~100% (Bar reaches the 100 gridline).
2. **Role-play:** ~67% (Bar is between 60 and 80, closer to 60).
3. **Recon/Env:** ~60% (Bar aligns with the 60 gridline).
4. **Directory:** ~50% (Bar is midway between 40 and 60).
5. **Exfiltration:** ~50% (Bar is identical in height to Directory).
6. **Obfuscation:** ~33% (Bar is between 20 and 40, closer to 40).
7. **Formatting:** ~20% (Bar aligns with the 20 gridline).
8. **Override:** 0% (No visible red bar).
9. **Context-leak:** 0% (No visible red bar).
10. **CTA/Nav:** 0% (No visible red bar).
**Data Series 2: Guard ON (Protected ASR %) - Green Bars**
For all ten attack categories, the green bar has a height of 0%. No green bars are visible above the x-axis baseline.
### Key Observations
1. **Complete Mitigation:** The "Guard ON" condition results in a 0% Attack Success Rate for every single category tested, indicating perfect protection in this dataset.
2. **Baseline Vulnerability Hierarchy:** Without the guard (`Guard OFF`), the system is most vulnerable to the `Delegate` attack (100% success). `Role-play` and `Recon/Env` are also highly successful (~67% and ~60%). The `Override`, `Context-leak`, and `CTA/Nav` categories show no baseline success (0%), suggesting they may be ineffective or not applicable in the baseline test scenario.
3. **Trend:** The baseline success rates follow a generally descending order from left to right as presented on the x-axis, with a plateau at 50% for `Directory` and `Exfiltration`.
### Interpretation
This chart presents a clear and compelling case for the efficacy of the implemented "Guard" mechanism. The data suggests that the guard is not merely reducing risk but is completely neutralizing the tested attack vectors, bringing their success rate from significant levels (up to 100%) down to zero.
The ordering of categories on the x-axis appears to be by descending baseline vulnerability, which helps prioritize understanding which attacks are most dangerous without protection. The fact that three categories (`Override`, `Context-leak`, `CTA/Nav`) have a 0% baseline success rate is notable. This could mean these attack types were not successfully executed in the baseline test, were mis-categorized, or represent theoretical threats that did not materialize in the specific testing environment. Their inclusion with 0% values provides a complete picture of the tested attack landscape.
From a security analysis perspective, the primary takeaway is the guard's flawless performance. The secondary insight is the profile of baseline weaknesses, which could inform further hardening efforts even with the guard active, following a defense-in-depth principle. The chart effectively communicates that enabling the guard changes the security posture from one with multiple high-risk vulnerabilities to one with no measurable success for these specific attacks.