## Diagram: Adversarial Attack Flow
### Overview
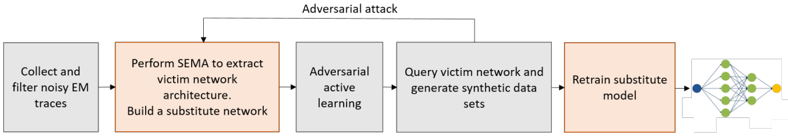
The image is a flowchart illustrating the steps of an adversarial attack on a victim network. The flow starts with collecting and filtering noisy EM traces and ends with retraining a substitute model.
### Components/Axes
The diagram consists of five rectangular boxes representing different stages of the attack. Arrows indicate the flow of information between these stages. An "Adversarial attack" arrow loops back from a later stage to an earlier one.
* **Boxes:** Each box contains a description of the action performed at that stage.
* **Arrows:** Arrows indicate the direction of the process flow.
* **Colors:** Boxes are either gray or orange, possibly indicating different types of actions.
* **Adversarial Attack Loop:** An arrow labeled "Adversarial attack" connects the "Query victim network and generate synthetic data sets" box back to the "Adversarial active learning" box.
### Detailed Analysis or ### Content Details
1. **Collect and filter noisy EM traces:** (Gray box, top-left) This is the initial step, involving the collection and filtering of electromagnetic (EM) traces.
2. **Perform SEMA to extract victim network architecture. Build a substitute network:** (Orange box, left-center) This step involves using Simple Electromagnetic Analysis (SEMA) to extract the architecture of the victim network and building a substitute network.
3. **Adversarial active learning:** (Gray box, center) This stage involves adversarial active learning.
4. **Query victim network and generate synthetic data sets:** (Gray box, right-center) The victim network is queried, and synthetic data sets are generated.
5. **Retrain substitute model:** (Orange box, right) The substitute model is retrained.
6. **Neural Network Representation:** (Right-most side) A simple neural network is depicted with a blue input node, green hidden nodes, and a yellow output node.
### Key Observations
* The process starts with data collection and analysis, moves to network architecture extraction and substitute network building, then involves adversarial active learning and querying, and finally retraining the substitute model.
* The "Adversarial attack" loop suggests an iterative process where the attacker refines their approach based on the victim network's responses.
* The use of different colors (gray and orange) for the boxes might indicate different categories of actions, such as data processing vs. model manipulation.
### Interpretation
The diagram illustrates a typical adversarial attack strategy. The attacker first gathers information about the victim network, then builds a substitute model to mimic its behavior. The adversarial active learning and querying stages are used to generate synthetic data that can be used to train the substitute model. The "Adversarial attack" loop indicates that the attacker iteratively refines their attack strategy based on the victim network's responses. This process aims to create a substitute model that can effectively mimic the victim network's behavior, allowing the attacker to craft adversarial inputs that can fool the victim network.