## Vulnerability Tree: Speculative Execution Vulnerability
### Overview
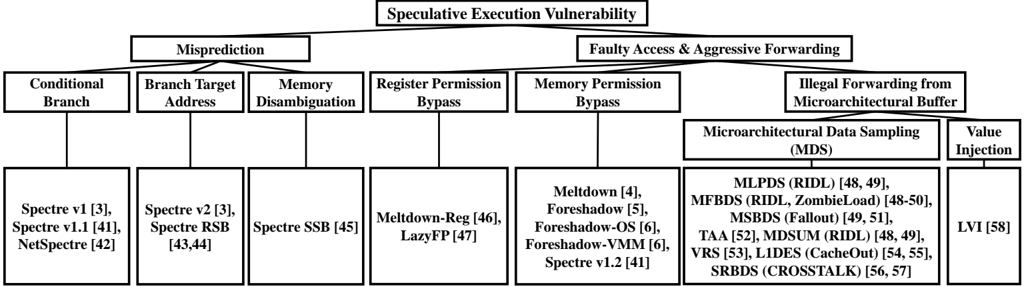
The image is a tree diagram illustrating the classification of speculative execution vulnerabilities. The diagram branches from the general category of "Speculative Execution Vulnerability" into two main categories: "Misprediction" and "Faulty Access & Aggressive Forwarding". Each of these categories is further subdivided into specific types of vulnerabilities and their corresponding exploits, along with associated reference numbers.
### Components/Axes
* **Root Node:** Speculative Execution Vulnerability
* **First Level Branches:**
* Misprediction
* Faulty Access & Aggressive Forwarding
* **Second Level Branches (under Misprediction):**
* Conditional Branch
* Branch Target Address
* Memory Disambiguation
* Register Permission Bypass
* **Second Level Branches (under Faulty Access & Aggressive Forwarding):**
* Memory Permission Bypass
* Illegal Forwarding from Microarchitectural Buffer
* **Third Level Branches (under Memory Permission Bypass):**
* Meltdown [4]
* Foreshadow [5]
* Foreshadow-OS [6]
* Foreshadow-VMM [6]
* Spectre v1.2 [41]
* **Third Level Branches (under Illegal Forwarding from Microarchitectural Buffer):**
* Microarchitectural Data Sampling (MDS)
* Value Injection
* **Fourth Level Branches (under Microarchitectural Data Sampling (MDS)):**
* MLPDS (RIDL) [48, 49]
* MFBDS (RIDL, ZombieLoad) [48-50]
* MSBDS (Fallout) [49, 51]
* TAA [52], MDSUM (RIDL) [48, 49]
* VRS [53], LIDES (CacheOut) [54, 55]
* SRBDS (CROSSTALK) [56, 57]
* **Fourth Level Branches (under Value Injection):**
* LVI [58]
* **Third Level Branches (under Conditional Branch):**
* Spectre v1 [3]
* Spectre v1.1 [41]
* NetSpectre [42]
* **Third Level Branches (under Branch Target Address):**
* Spectre v2 [3]
* Spectre RSB [43, 44]
* **Third Level Branches (under Memory Disambiguation):**
* Spectre SSB [45]
* **Third Level Branches (under Register Permission Bypass):**
* Meltdown-Reg [46]
* LazyFP [47]
### Detailed Analysis or Content Details
The diagram presents a hierarchical breakdown of speculative execution vulnerabilities. It starts with the broad category and then branches into more specific types. Each vulnerability type is associated with specific exploits or attacks, indicated by names like "Spectre," "Meltdown," "Foreshadow," and "LVI," along with corresponding reference numbers in square brackets.
* **Speculative Execution Vulnerability** is the root of the tree.
* **Misprediction** branches into:
* **Conditional Branch:** Includes Spectre v1 [3], Spectre v1.1 [41], and NetSpectre [42].
* **Branch Target Address:** Includes Spectre v2 [3] and Spectre RSB [43, 44].
* **Memory Disambiguation:** Includes Spectre SSB [45].
* **Register Permission Bypass:** Includes Meltdown-Reg [46] and LazyFP [47].
* **Faulty Access & Aggressive Forwarding** branches into:
* **Memory Permission Bypass:** Includes Meltdown [4], Foreshadow [5], Foreshadow-OS [6], Foreshadow-VMM [6], and Spectre v1.2 [41].
* **Illegal Forwarding from Microarchitectural Buffer:** Branches into:
* **Microarchitectural Data Sampling (MDS):** Includes MLPDS (RIDL) [48, 49], MFBDS (RIDL, ZombieLoad) [48-50], MSBDS (Fallout) [49, 51], TAA [52], MDSUM (RIDL) [48, 49], VRS [53], LIDES (CacheOut) [54, 55], and SRBDS (CROSSTALK) [56, 57].
* **Value Injection:** Includes LVI [58].
### Key Observations
* The diagram provides a structured overview of speculative execution vulnerabilities.
* It categorizes vulnerabilities based on their root cause (Misprediction vs. Faulty Access & Aggressive Forwarding).
* It lists specific exploits associated with each vulnerability type, along with reference numbers.
* The diagram highlights the complexity of speculative execution vulnerabilities and the variety of attacks that can exploit them.
### Interpretation
The diagram serves as a taxonomy of speculative execution vulnerabilities, illustrating the relationships between different types of vulnerabilities and their corresponding exploits. It demonstrates that speculative execution vulnerabilities can arise from various sources, including mispredictions and faulty access/forwarding mechanisms. The diagram is useful for understanding the landscape of speculative execution vulnerabilities and for identifying potential attack vectors. The reference numbers likely point to research papers or other documentation that provide more detailed information about each vulnerability and exploit. The presence of multiple exploits under each category suggests that these vulnerabilities can be exploited in various ways. The diagram emphasizes the importance of addressing speculative execution vulnerabilities to ensure the security of computer systems.