\n
## Diagram: Speculative Execution Vulnerability Taxonomy
### Overview
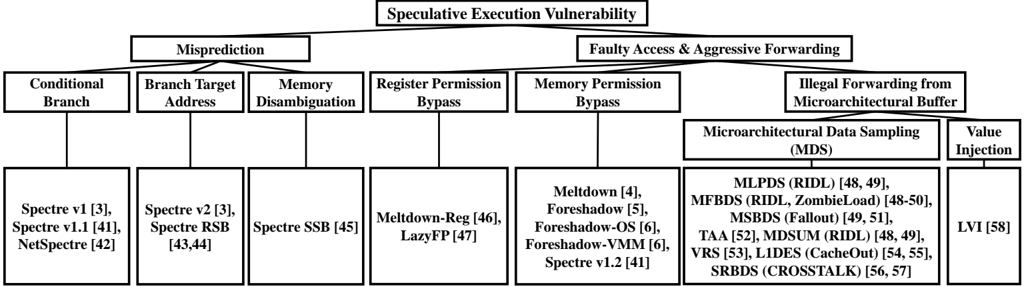
The image is a hierarchical diagram illustrating the taxonomy of speculative execution vulnerabilities. It categorizes these vulnerabilities into two main branches: "Misprediction" and "Faulty Access & Aggressive Forwarding," then further subdivides each branch into more specific vulnerability types. Each vulnerability type is associated with a list of related attacks or research papers, indicated by names and numerical references in square brackets.
### Components/Axes
The diagram is structured as a tree. The root node is "Speculative Execution Vulnerability." The two main branches are "Misprediction" and "Faulty Access & Aggressive Forwarding." These branches are further divided into:
* **Misprediction:**
* Conditional Branch
* Branch Target Address
* Memory Disambiguation
* Register Permission Bypass
* **Faulty Access & Aggressive Forwarding:**
* Memory Permission Bypass
* Illegal Forwarding from Microarchitectural Buffer
* Microarchitectural Data Sampling (MDS)
* Value Injection
Each of these sub-categories is then associated with a list of specific vulnerabilities.
### Detailed Analysis or Content Details
**Misprediction Branch:**
* **Conditional Branch:** Associated with Spectre v1 [3], Spectre v1.1 [41], NetSpectre [42].
* **Branch Target Address:** Associated with Spectre v2 [3], Spectre RSB [43,44].
* **Memory Disambiguation:** Associated with Spectre SSB [45].
* **Register Permission Bypass:** Associated with Meltdown-Reg [46], LazyFP [47].
**Faulty Access & Aggressive Forwarding Branch:**
* **Memory Permission Bypass:** Associated with Meltdown [4], Foreshadow [5], Foreshadow-OS [6], Foreshadow-VMM [6], Spectre v1.2 [41].
* **Illegal Forwarding from Microarchitectural Buffer:**
* **Microarchitectural Data Sampling (MDS):** Associated with MLPDS (RIDL) [48, 49], MFBDs (RIDL, ZombieLoad) [48-50], MSBDS (Fallout) [49, 51], TAA [52], MDSUM (RIDL) [48, 49], VRS [53], LIDES (CacheOut) [54, 55], SRBDS (CROSSTALK) [56, 57].
* **Value Injection:** Associated with LVI [58].
### Key Observations
The diagram demonstrates a clear categorization of speculative execution vulnerabilities. The "Misprediction" branch focuses on vulnerabilities arising from incorrect prediction of program behavior, while the "Faulty Access & Aggressive Forwarding" branch focuses on vulnerabilities related to improper handling of data access and forwarding within the processor. The MDS sub-category has a significantly larger number of associated vulnerabilities compared to other categories, indicating its complexity and prevalence.
### Interpretation
This diagram serves as a taxonomy for understanding the landscape of speculative execution vulnerabilities. It highlights the different attack vectors and the specific vulnerabilities that exploit them. The inclusion of research paper references suggests that this diagram is based on academic research and is intended for a technical audience. The hierarchical structure allows for a systematic understanding of the relationships between different vulnerabilities. The large number of associated attacks under MDS suggests that this is a particularly active area of research and a significant threat to system security. The diagram is a valuable resource for security researchers, system architects, and anyone interested in understanding the intricacies of speculative execution vulnerabilities.