\n
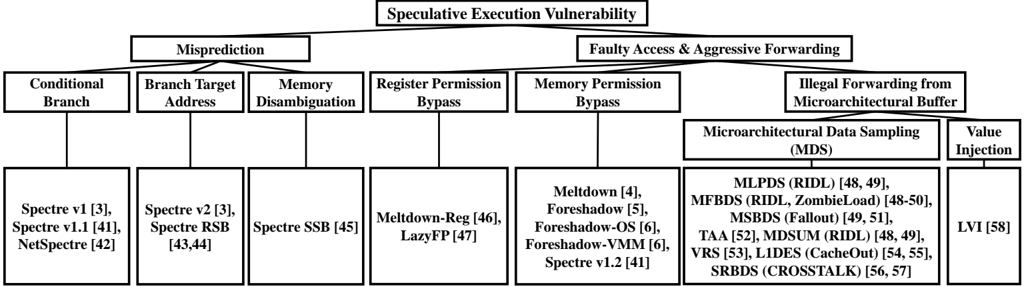
## Diagram: Speculative Execution Vulnerability Taxonomy
### Overview
This image is a hierarchical classification diagram (taxonomy tree) that categorizes different types of speculative execution vulnerabilities in computer processors. It organizes known vulnerabilities based on their underlying root cause or exploitation mechanism, branching from a central concept down to specific named attacks and their academic citations.
### Components/Axes
The diagram is structured as a top-down tree with the following hierarchical levels:
1. **Root Node (Top Center):** "Speculative Execution Vulnerability"
2. **Primary Branches (Level 2):** Two main categories stemming from the root:
* **Left Branch:** "Misprediction"
* **Right Branch:** "Faulty Access & Aggressive Forwarding"
3. **Secondary Categories (Level 3):** Specific mechanisms under each primary branch.
* Under **Misprediction**:
* "Conditional Branch"
* "Branch Target Address"
* "Memory Disambiguation"
* Under **Faulty Access & Aggressive Forwarding**:
* "Register Permission Bypass"
* "Memory Permission Bypass"
* "Illegal Forwarding from Microarchitectural Buffer"
4. **Tertiary Categories / Specific Vulnerabilities (Level 4):** Lists of named attacks and their reference numbers, contained within rectangular boxes. The "Illegal Forwarding..." category further splits into two sub-groups: "Microarchitectural Data Sampling (MDS)" and "Value Injection".
### Detailed Analysis
**Textual Content and Relationships:**
* **Misprediction Branch:**
* **Conditional Branch** leads to: `Spectre v1 [3], Spectre v1.1 [41], NetSpectre [42]`
* **Branch Target Address** leads to: `Spectre v2 [3], Spectre RSB [43,44]`
* **Memory Disambiguation** leads to: `Spectre SSB [45]`
* **Faulty Access & Aggressive Forwarding Branch:**
* **Register Permission Bypass** leads to: `Meltdown-Reg [46], LazyFP [47]`
* **Memory Permission Bypass** leads to: `Meltdown [4], Foreshadow [5], Foreshadow-OS [6], Foreshadow-VMM [6], Spectre v1.2 [41]`
* **Illegal Forwarding from Microarchitectural Buffer** splits into:
* **Microarchitectural Data Sampling (MDS)** leads to: `MLPDS (RIDL) [48, 49], MFBDS (RIDL, ZombieLoad) [48-50], MSBDS (Fallout) [49, 51], TAA [52], MDSUM (RIDL) [48, 49], VRS [53], LIDES (CacheOut) [54, 55], SRBDS (CROSSTALK) [56, 57]`
* **Value Injection** leads to: `LVI [58]`
**Spatial Grounding:**
* The root title is centered at the top.
* The two primary branches are positioned symmetrically left and right below the root.
* The secondary categories are arranged horizontally beneath their respective primary branch.
* The specific vulnerability boxes are aligned vertically below their parent category. The box for "Illegal Forwarding..." is the widest, accommodating its two sub-groups and extensive list of MDS variants.
### Key Observations
1. **Categorization Logic:** Vulnerabilities are grouped by the CPU microarchitectural component or prediction mechanism they exploit (e.g., branch predictor, memory disambiguation unit, permission checks, internal buffers).
2. **Spectre Family:** The "Spectre" variants are distributed across the "Misprediction" branch, highlighting their reliance on mis-speculation.
3. **Meltdown Family:** "Meltdown" and its variants ("Meltdown-Reg", "Foreshadow" series) are clustered under "Faulty Access," specifically related to permission bypass.
4. **MDS Cluster:** A significant number of recent vulnerabilities (RIDL, ZombieLoad, Fallout, CacheOut, CROSSTALK) are grouped under "Microarchitectural Data Sampling (MDS)," indicating a major class of attacks targeting internal CPU buffers.
5. **Citation Density:** The diagram is heavily referenced, with nearly every specific vulnerability linked to one or more academic papers or disclosures (e.g., `[3]`, `[48, 49]`).
### Interpretation
This diagram serves as a **conceptual map for understanding the attack surface of speculative execution**. It moves beyond a simple list of CVEs to explain *how* different attacks work at a fundamental level.
* **Relationships:** It shows that many seemingly distinct vulnerabilities (e.g., Spectre v1, Spectre v1.1, NetSpectre) share a common root cause (conditional branch misprediction). Conversely, it clarifies that "Meltdown" and "Spectre" exploit different mechanisms (permission bypass vs. misprediction).
* **Trends:** The dense cluster under "Microarchitectural Data Sampling" suggests a fertile area of research and a systemic issue in how modern CPUs handle data in internal, non-architectural buffers during speculative execution.
* **Anomalies/Notable Points:** "Spectre v1.2" is listed under "Memory Permission Bypass," which is interesting as it suggests a Spectre-variant that crosses the typical categorization boundary, potentially blending misprediction with permission logic flaws.
* **Why it Matters:** For security researchers, system architects, and compiler developers, this taxonomy is crucial. It helps in designing holistic mitigations (like retpolines for branch misprediction or buffer flushing for MDS) rather than patching individual vulnerabilities. It also predicts that future vulnerabilities will likely be discovered within these established categories or in new, yet-to-be-defined branches of the tree.