## Diagram Type: Flowchart
### Overview
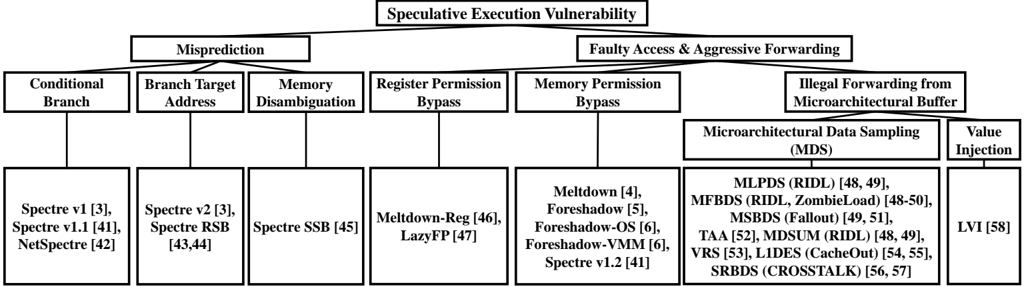
The image is a flowchart that illustrates the various stages and components involved in a speculative execution vulnerability. The flowchart is organized into a hierarchical structure with different levels of detail, starting from the top-level concept of "Speculative Execution Vulnerability" to the bottom-level components and their relationships.
### Components/Axes
- **Misprediction**: This is the starting point of the flowchart, indicating that mispredictions are a key factor in the vulnerability.
- **Conditional Branch**: This component is connected to the misprediction and represents the conditional branching in the code.
- **Branch Target Address**: This is another component connected to the misprediction, indicating the target address of the conditional branch.
- **Memory Disambiguation**: This component is connected to the misprediction and represents the process of disambiguating memory addresses.
- **Register Permission Bypass**: This component is connected to the misprediction and represents the bypassing of register permissions.
- **Memory Permission Bypass**: This component is connected to the misprediction and represents the bypassing of memory permissions.
- **Illegal Forwarding from Microarchitectural Buffer**: This component is connected to the faulty access and aggressive forwarding and represents the illegal forwarding of data from the microarchitectural buffer.
- **Microarchitectural Data Sampling (MDS)**: This component is connected to the illegal forwarding from the microarchitectural buffer and represents the sampling of microarchitectural data.
- **Value Injection**: This component is connected to the MDS and represents the injection of values into the system.
### Detailed Analysis or ### Content Details
The flowchart uses a combination of rectangles and arrows to represent the different components and their relationships. The rectangles are labeled with the name of the component, and the arrows indicate the flow of information from one component to another. The flowchart also includes numerical values and text descriptions to provide additional context and detail.
### Key Observations
The flowchart highlights the importance of mispredictions in the vulnerability, as they can lead to conditional branches and memory disambiguation. The flowchart also shows the potential for register and memory permission bypassing, as well as illegal forwarding from the microarchitectural buffer. The flowchart also indicates the role of microarchitectural data sampling and value injection in the vulnerability.
### Interpretation
The flowchart suggests that speculative execution vulnerabilities can be complex and multifaceted, involving a combination of mispredictions, conditional branches, memory disambiguation, register and memory permission bypassing, illegal forwarding from the microarchitectural buffer, microarchitectural data sampling, and value injection. The flowchart also highlights the importance of understanding the relationships between these components to develop effective countermeasures against speculative execution vulnerabilities.