## Table: Feature Comparison of Security Technologies
### Overview
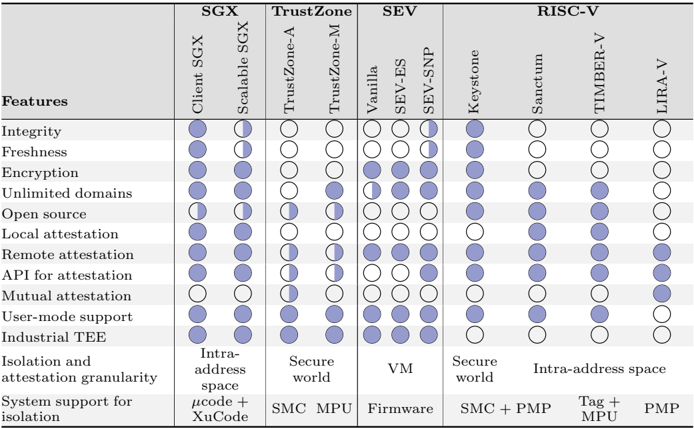
The image is a comparison table evaluating security technologies across 14 features. Each technology is represented by columns, with features listed as rows. Support is indicated by filled (blue) or empty (white) circles, with some partial fills (half-circles) for partial support.
### Components/Axes
- **Columns (Technologies)**:
- SGX: Client SGX, Scalable SGX
- TrustZone: TrustZone-A, TrustZone-M
- SEV: Vanilla, SEV-ES, SEV-SNP
- RISC-V: Keystone, Sanctum, TIMBER-V, LIRA-V
- **Rows (Features)**:
1. Integrity
2. Freshness
3. Encryption
4. Unlimited domains
5. Open source
6. Local attestation
7. Remote attestation
8. API for attestation
9. Mutual attestation
10. User-mode support
11. Industrial TEE
12. Isolation and attestation granularity
13. System support for isolation
### Detailed Analysis
- **Integrity, Freshness, Encryption, Unlimited domains**: All technologies support these features (all circles filled).
- **Open source**: Only Client SGX (50% fill), TrustZone-M (50% fill), and SEV-SNP (50% fill) show partial support.
- **Local attestation**: All technologies except TrustZone-A and TrustZone-M support this (partial fill for TrustZone-M).
- **Remote attestation**: All technologies support this (partial fill for TrustZone-A and TrustZone-M).
- **API for attestation**: All technologies support this (partial fill for TrustZone-A and TrustZone-M).
- **Mutual attestation**: Only LIRA-V supports this (filled circle).
- **User-mode support**: All technologies except Keystone and LIRA-V support this (filled circles).
- **Industrial TEE**: All technologies except Keystone, Sanctum, TIMBER-V, and LIRA-V support this (filled circles).
- **Isolation and attestation granularity**:
- SGX: Intra-address space
- TrustZone: Secure world
- SEV: VM
- RISC-V: Secure world (Keystone, Sanctum, TIMBER-V), Intra-address space (LIRA-V)
- **System support for isolation**:
- SGX: μcode + XuCode
- TrustZone: SMC MPU
- SEV: Firmware
- RISC-V: SMC + PMP (Keystone, Sanctum), Tag + MPU (TIMBER-V), PMP (LIRA-V)
### Key Observations
1. **SGX Dominance**: Client and Scalable SGX support the most features, including mutual attestation and industrial TEE.
2. **TrustZone Limitations**: TrustZone-A and TrustZone-M lack support for mutual attestation and industrial TEE.
3. **SEV Variability**: SEV-SNP has the most comprehensive feature set among SEV variants.
4. **RISC-V Gaps**: Keystone and LIRA-V lack industrial TEE support; TIMBER-V lacks user-mode support.
5. **Attestation Granularity**: SGX and RISC-V use intra-address space, while TrustZone and SEV use secure world/VM.
### Interpretation
The table highlights SGX as the most feature-complete technology, particularly for attestation capabilities. TrustZone variants show significant gaps in advanced features like mutual attestation. RISC-V implementations vary widely, with LIRA-V offering unique intra-address space isolation but missing industrial TEE. SEV-SNP emerges as a strong contender among SEV variants, supporting most features except open source and mutual attestation. The data suggests SGX remains the gold standard for comprehensive security features, while RISC-V and TrustZone require further development to match SGX's capabilities.