## [Diagram]: Cloud Environment TEE Attestation Flow
### Overview
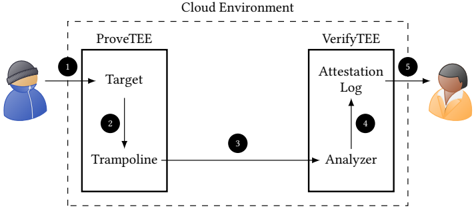
The image is a technical diagram illustrating a two-phase attestation process within a "Cloud Environment." It depicts a secure workflow between two Trusted Execution Environments (TEEs), labeled **ProveTEE** and **VerifyTEE**, facilitated by a user/operator and involving a sequence of five numbered steps. The diagram uses a clean, schematic style with icons, labeled boxes, and directional arrows to show the flow of data or control.
### Components/Axes
The diagram is contained within a dashed rectangular border labeled **"Cloud Environment"** at the top center.
**Primary Components:**
1. **ProveTEE (Left Box):** A rectangular container representing the proving TEE. It contains two internal components:
* **Target** (top)
* **Trampoline** (bottom)
2. **VerifyTEE (Right Box):** A rectangular container representing the verifying TEE. It contains two internal components:
* **Attestation Log** (top)
* **Analyzer** (bottom)
3. **User Icons:**
* A blue-shirted user icon on the far left, initiating the process.
* An orange-shirted user icon on the far right, receiving the output.
**Flow Indicators (Numbered Steps):**
* **Step 1:** Arrow from the left user icon to the **Target** component in ProveTEE.
* **Step 2:** Arrow from **Target** down to **Trampoline** within ProveTEE.
* **Step 3:** Arrow from **Trampoline** (ProveTEE) across to the **Analyzer** (VerifyTEE).
* **Step 4:** Arrow from **Analyzer** up to **Attestation Log** within VerifyTEE.
* **Step 5:** Arrow from **Attestation Log** to the right user icon.
### Detailed Analysis
The diagram outlines a clear, linear sequence of operations:
1. **Initiation (Step 1):** An external user or process (left icon) sends a request or data to the **Target** within the ProveTEE.
2. **Internal Processing in ProveTEE (Step 2):** The **Target** processes the input and passes it to the **Trampoline**. The term "Trampoline" suggests a mechanism for secure code execution or data transfer within the TEE boundary.
3. **Cross-TEE Communication (Step 3):** The **Trampoline** sends information (likely an attestation report or proof) to the **Analyzer** component in the separate VerifyTEE. This is the critical handoff between the proving and verifying environments.
4. **Verification & Logging in VerifyTEE (Step 4):** The **Analyzer** processes the received data and writes the result or a verified record to the **Attestation Log**.
5. **Output (Step 5):** The final result from the **Attestation Log** is made available to an external verifier or user (right icon).
### Key Observations
* **Asymmetric Roles:** The two TEEs have distinct, complementary functions. ProveTEE is responsible for generating a proof from a target, while VerifyTEE is responsible for analyzing and logging that proof.
* **Unidirectional Flow:** The process is strictly sequential and one-way, from left to right, with no feedback loops shown.
* **Component Isolation:** Each TEE (ProveTEE, VerifyTEE) is a self-contained unit with its own internal components, emphasizing security boundaries.
* **Human-in-the-Loop:** The process is bookended by human operators (or external systems represented by human icons), indicating it is likely a managed or auditable procedure.
### Interpretation
This diagram represents a **secure remote attestation architecture** for cloud-based Trusted Execution Environments. The flow demonstrates how a workload (the "Target") can prove its integrity and configuration to a remote verifier.
* **What it demonstrates:** It shows a standardized protocol for establishing trust. The ProveTEE generates evidence about its internal state (via the Target and Trampoline), which is then securely transmitted to and evaluated by the independent VerifyTEE. The final attestation log provides a verifiable record of this assessment.
* **Relationships:** The security of the system hinges on the isolation of the two TEEs and the integrity of the communication channel (Step 3). The VerifyTEE acts as a trusted third party, validating claims made by the ProveTEE without being co-located with it.
* **Notable Implications:** The use of "Trampoline" and "Analyzer" as specific component names suggests a modular design where the attestation logic (Analyzer) is separated from the proof generation logic (Trampoline). This separation of concerns enhances security and flexibility. The entire process is encapsulated within a "Cloud Environment," indicating this is a model for secure computation in multi-tenant or untrusted infrastructure.