\n
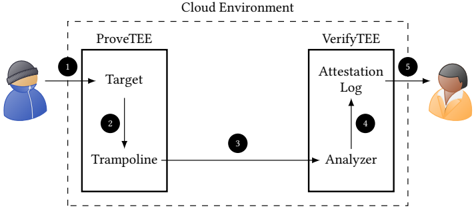
## Diagram: Cloud Environment Attestation Flow
### Overview
The image depicts a diagram illustrating a cloud environment attestation flow between a user, a "ProveTEE" component, and a "VerifyTEE" component. The diagram shows the sequence of interactions and data flow for verifying the integrity of a target environment. The entire process is contained within a box labeled "Cloud Environment".
### Components/Axes
The diagram consists of the following components:
* **User (Left):** Represented by a cartoon figure wearing a hoodie.
* **ProveTEE:** A rectangular block containing "Target" and "Trampoline" components.
* **VerifyTEE:** A rectangular block containing "Analyzer" and "Attestation Log" components.
* **Target:** A component within ProveTEE.
* **Trampoline:** A component within ProveTEE.
* **Analyzer:** A component within VerifyTEE.
* **Attestation Log:** A component within VerifyTEE.
* **Cloud Environment:** A dashed-line rectangle encompassing ProveTEE and VerifyTEE.
* **Numbered Arrows:** Indicate the flow of data/interaction. Numbers 1 through 5 mark the sequence.
### Detailed Analysis / Content Details
The diagram illustrates the following sequence of events:
1. **User to ProveTEE:** An arrow (labeled '1') originates from the user and points towards the "Target" component within "ProveTEE". This represents an initial request or interaction.
2. **Target to Trampoline:** An arrow (labeled '2') originates from the "Target" component and points to the "Trampoline" component within "ProveTEE". This suggests a transition or execution flow within the trusted environment.
3. **Trampoline to Analyzer:** An arrow (labeled '3') originates from the "Trampoline" component and points to the "Analyzer" component within "VerifyTEE". This indicates the transfer of data or attestation information.
4. **Analyzer to Attestation Log:** An arrow (labeled '4') originates from the "Analyzer" component and points to the "Attestation Log" component within "VerifyTEE". This suggests the recording of analysis results.
5. **Attestation Log to User:** An arrow (labeled '5') originates from the "Attestation Log" component and points to the user. This represents the final attestation result being delivered to the user.
### Key Observations
The diagram highlights a clear separation between the "ProveTEE" and "VerifyTEE" components. The flow is sequential, starting with a user request, proceeding through the trusted execution environment ("ProveTEE"), analysis by "VerifyTEE", and finally, a result delivered back to the user. The "Trampoline" component within "ProveTEE" suggests a mechanism for transitioning between different execution contexts or security domains.
### Interpretation
This diagram illustrates a remote attestation process within a cloud environment. The "ProveTEE" component likely represents a Trusted Execution Environment (TEE) where sensitive computations are performed. The "Target" could be the application or code being attested. The "Trampoline" might be a mechanism to enter or exit the TEE. The "VerifyTEE" component acts as a verifier, analyzing the attestation data provided by the TEE and recording the results in the "Attestation Log". The user receives the final attestation result, confirming the integrity of the target environment.
The diagram suggests a security model where a remote party (the user) relies on a trusted third party ("VerifyTEE") to verify the integrity of a remote computation ("ProveTEE"). This is a common pattern in cloud security, where users need to trust that their data and computations are being performed in a secure and trustworthy environment. The numbered arrows are crucial for understanding the order of operations and the flow of information.