\n
## Diagram: Secure Front-End Data Flow
### Overview
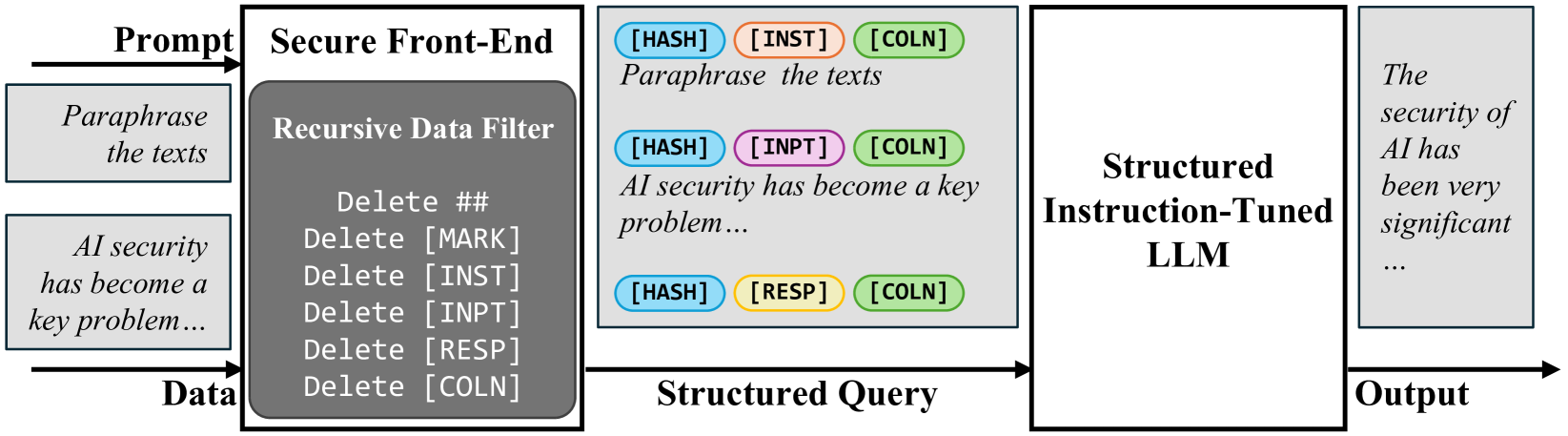
This diagram illustrates a data flow process for enhancing AI security through a secure front-end system. The process involves a prompt, a recursive data filter, a structured query, and a structured instruction-tuned Large Language Model (LLM) to generate an output. The diagram highlights data manipulation steps within the filter, including deletion of specific markers.
### Components/Axes
The diagram consists of four main rectangular blocks representing stages in the process:
1. **Prompt:** Top-left, input stage.
2. **Recursive Data Filter:** Center-left, processing stage.
3. **Structured Query:** Center-right, intermediate stage.
4. **Structured Instruction-Tuned LLM:** Bottom-right, output stage.
Additionally, there are connecting arrows indicating the flow of data between these stages. Text labels are embedded within each block and along the arrows.
### Detailed Analysis or Content Details
**1. Prompt Block (Top-Left):**
- Label: "Prompt"
- Contains the text: "Paraphrase the texts"
- An arrow originates from this block, leading to the "Recursive Data Filter" block.
**2. Recursive Data Filter Block (Center-Left):**
- Label: "Recursive Data Filter"
- Contains the text: "Delete ##", "Delete [MARK]", "Delete [INST]", "Delete [INPT]", "Delete [RESP]", "Delete [COLN]".
- Contains the text: "AI security has become a key problem..."
- Contains the text: "Data"
- An arrow originates from this block, leading to the "Structured Query" block.
**3. Structured Query Block (Center-Right):**
- Label: "Structured Query"
- Contains the text: "AI security has become a key problem..."
- Contains the text: "[HASH] [INST] [COLN]" (in the top section)
- Contains the text: "[HASH] [INPT] [COLN]" (in the middle section)
- Contains the text: "[HASH] [RESP] [COLN]" (in the bottom section)
- An arrow originates from this block, leading to the "Structured Instruction-Tuned LLM" block.
**4. Structured Instruction-Tuned LLM Block (Bottom-Right):**
- Label: "Structured Instruction-Tuned LLM"
- Contains the text: "The security of AI has been very significant..."
- An arrow originates from this block, labeled "Output".
### Key Observations
- The diagram demonstrates a data processing pipeline designed to refine and secure input data before it reaches an LLM.
- The "Recursive Data Filter" block specifically targets and removes certain markers ([HASH], [INST], [COLN], [MARK], [INPT], [RESP]) from the input data.
- The "Structured Query" block appears to re-format the data, potentially adding hash tags and the markers that were deleted in the previous step.
- The final output from the LLM is a paraphrased and potentially more secure version of the original prompt.
### Interpretation
The diagram illustrates a method for improving the security and quality of data fed into an LLM. The recursive data filter likely aims to remove potentially harmful or irrelevant information (represented by the deleted markers) from the input. The re-formatting in the "Structured Query" block might be preparing the data for optimal processing by the LLM. The overall process suggests a focus on mitigating risks associated with prompt injection or other vulnerabilities in LLM-based systems. The markers likely represent metadata or control signals that are not needed for the LLM's core task and could be exploited. The diagram highlights a layered approach to security, with data filtering and structured querying preceding the LLM interaction.