## Flowchart: AI Security Processing Pipeline
### Overview
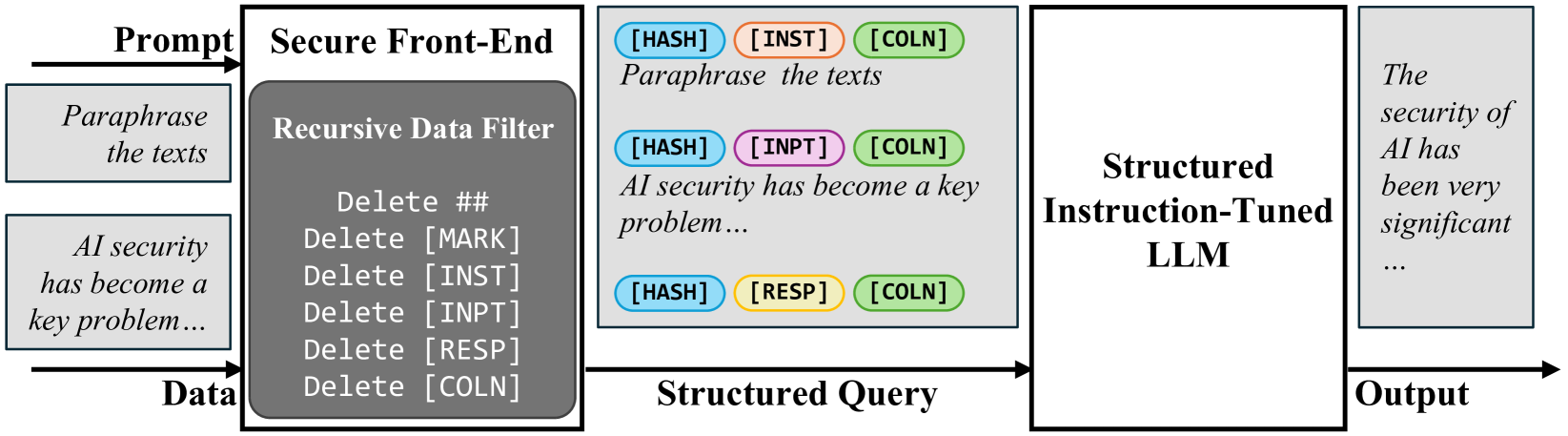
The diagram illustrates a multi-stage AI processing pipeline focused on security and structured data handling. It begins with input prompts and data, progresses through a secure front-end with recursive filtering, generates structured queries, and concludes with an instruction-tuned language model (LLM) producing security-focused outputs.
### Components/Axes
1. **Input Section**
- **Prompt**: "Paraphrase the texts"
- **Data**: "AI security has become a key problem..."
2. **Secure Front-End**
- **Recursive Data Filter**: Contains repeated "Delete" commands targeting:
- `##` (metadata?)
- `[MARK]` (sensitive markers)
- `[INST]` (instruction tokens)
- `[INPT]` (input tokens)
- `[RESP]` (response tokens)
- `[COLN]` (columnar data)
3. **Structured Query**
- Three colored blocks with hierarchical relationships:
- **Blue (HASH)**: "Paraphrase the texts"
- **Orange (INST)**: "AI security has become a key problem..."
- **Green (COLN)**: Columnar data marker
- **Purple (INPT)**: Input token placeholder
- **Yellow (RESP)**: Response token placeholder
4. **Structured Instruction-Tuned LLM**
- Final processing unit generating security-focused outputs
5. **Output**
- "The security of AI has been very significant..."
### Detailed Analysis
- **Recursive Data Filter**:
- Systematically removes metadata (`##`), sensitive markers (`[MARK]`), and tokenized data (`[INST]`, `[INPT]`, `[RESP]`, `[COLN]`).
- Suggests a sanitization process to eliminate non-essential or security risks.
- **Structured Query**:
- Retains `HASH` (data integrity) and `COLN` (structural markers) across all blocks.
- Introduces `INST` (instruction context) and `INPT`/`RESP` (input/output tokens) in later stages.
- Color coding implies hierarchical processing:
- Blue (`HASH`): Foundational data integrity
- Orange (`INST`): Instructional context
- Green (`COLN`): Structural alignment
- Purple/Yellow (`INPT`/`RESP`): Dynamic input/output handling
- **Output**:
- Final response emphasizes AI security's significance, aligning with the input's focus on security challenges.
### Key Observations
1. **Security-Centric Design**:
- The Recursive Data Filter aggressively removes potential security risks (e.g., `[MARK]`, `[INST]`).
- Output explicitly highlights AI security, reinforcing the pipeline's purpose.
2. **Structured Data Flow**:
- `HASH` and `COLN` persist throughout, ensuring data integrity and structural consistency.
- `INST` and `INPT`/`RESP` tokens suggest adaptive processing of instructions and responses.
3. **Color-Coded Hierarchy**:
- Blue (`HASH`): Core data integrity
- Orange (`INST`): Instructional logic
- Green (`COLN`): Structural scaffolding
- Purple/Yellow (`INPT`/`RESP`): Dynamic interaction points
### Interpretation
This pipeline demonstrates a **security-first AI architecture** where:
1. **Input Sanitization**: The Recursive Data Filter acts as a gatekeeper, removing sensitive or irrelevant data early in the process.
2. **Structured Query Generation**: The colored blocks represent a layered approach to data structuring, balancing integrity (`HASH`), context (`INST`), and adaptability (`INPT`/`RESP`).
3. **LLM Specialization**: The final stage focuses on generating outputs that emphasize AI security, suggesting the LLM is fine-tuned for this domain.
The diagram implies a **trade-off between security and functionality**: while aggressive filtering enhances security, it may risk losing nuanced context. The persistent use of `HASH` and `COLN` ensures that critical structural and integrity markers survive the filtering process, enabling the LLM to produce coherent, security-focused outputs.