# Technical Data Extraction: Network Traffic Frequency Distribution
## 1. Document Overview
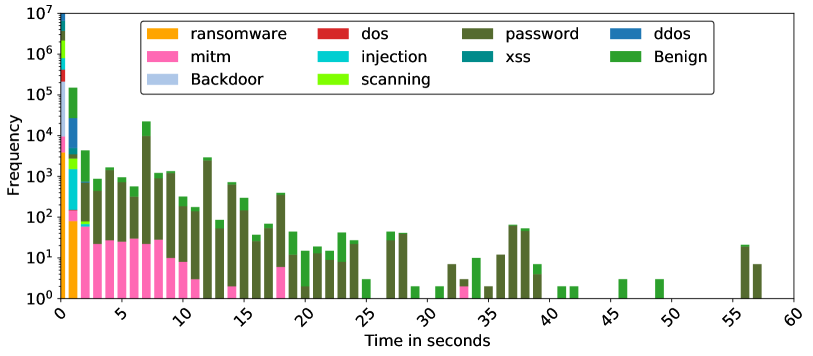
This image is a stacked bar chart (histogram) representing the frequency of different types of network traffic (both malicious and benign) over a duration of time. The data is plotted on a logarithmic scale for the frequency to accommodate a wide range of values.
## 2. Component Isolation
### A. Header / Legend
* **Location:** Top-center, enclosed in a rounded rectangle.
* **Content:** 11 categories of traffic, each associated with a specific color.
* **Orange:** ransomware
* **Red:** dos
* **Dark Olive Green:** password
* **Blue:** ddos
* **Pink:** mitm
* **Cyan:** injection
* **Teal:** xss
* **Green:** Benign
* **Light Blue-Grey:** Backdoor
* **Lime Green:** scanning
### B. Main Chart Area (Axes)
* **Y-Axis (Vertical):**
* **Label:** Frequency
* **Scale:** Logarithmic, ranging from $10^0$ (1) to $10^7$ (10,000,000).
* **Major Markers:** $10^0, 10^1, 10^2, 10^3, 10^4, 10^5, 10^6, 10^7$.
* **X-Axis (Horizontal):**
* **Label:** Time in seconds
* **Scale:** Linear, ranging from 0 to 60 seconds.
* **Major Markers:** 0, 5, 10, 15, 20, 25, 30, 35, 40, 45, 50, 55, 60.
* **Note:** Labels are rotated approximately 45 degrees for readability.
## 3. Data Analysis and Trends
### General Trend
The chart shows a "long tail" distribution. The vast majority of network events occur within the first 0–2 seconds, with frequencies reaching up to $10^7$. As time increases, the frequency of events drops significantly, becoming sporadic and sparse after 40 seconds.
### Category-Specific Observations
* **High-Volume Initial Burst (0-1s):** This column contains almost all categories. The highest frequency is dominated by **Benign** (Green), **ddos** (Blue), and **scanning** (Lime Green) traffic, all exceeding $10^5$ occurrences. **Ransomware** (Orange) is also visible here but is confined to the very beginning of the timeline.
* **Persistent Categories:**
* **Password (Dark Olive Green):** This is the most persistent malicious category. It appears consistently across the timeline from 0 to 58 seconds. It forms significant peaks at 7s, 12s, and 37s.
* **Mitm (Pink):** Frequent in the 0–10 second range, with a small reappearance around 18s and 33s.
* **Benign (Green):** Present throughout most of the timeline, often stacked on top of "password" or "mitm" data.
* **Short-Duration Categories:**
* **Ransomware, Dos, Injection, XSS, Backdoor, and Scanning** are primarily concentrated in the 0–2 second window and do not appear significantly in the later stages of the 60-second window.
## 4. Data Table (Estimated Values)
*Note: Due to the logarithmic scale and stacked nature, values are approximations based on visual alignment with axis markers.*
| Time (s) | Primary Components | Approx. Total Frequency |
| :--- | :--- | :--- |
| **0-1** | All (Benign, ddos, scanning, etc.) | $10^7$ |
| **1-2** | Benign, ddos, scanning, mitm | $10^5$ |
| **2-3** | Benign, password | $5 \times 10^3$ |
| **7-8** | Password, Benign | $2 \times 10^4$ |
| **12-13**| Password, Benign | $3 \times 10^3$ |
| **20-25**| Benign, password | $10^1 - 10^2$ |
| **37-38**| Password | $7 \times 10^1$ |
| **56-58**| Password | $< 10^1$ |
## 5. Summary of Findings
The dataset is heavily skewed toward the start of the capture period. While most attack types (like DDoS and Injection) are instantaneous or very short-lived, **Password**-related attacks and **Benign** traffic are the only types that exhibit sustained activity over the full 60-second duration. The logarithmic scale highlights that while late-stage events are visible, they are several orders of magnitude less frequent than the initial burst.