## Diagram: Malware Process Flow and Threat Scenarios
### Overview
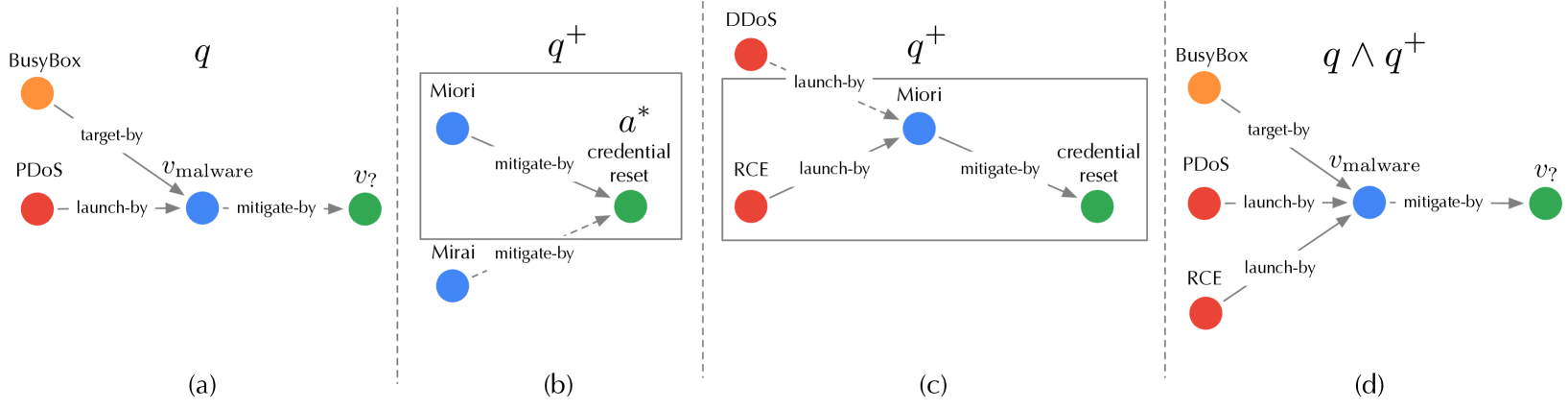
The image consists of four interconnected diagrams (a-d) illustrating malware-related processes, threat actors, and mitigation strategies. Nodes are color-coded (orange, red, blue, green) with directional arrows labeled with actions like "launch-by" and "mitigate-by". Key elements include threat actors (BusyBox, PDoS, RCE), malware variants (v_malware, v?), and defensive/reset mechanisms (credential reset).
---
### Components/Axes
- **Nodes**:
- Orange: BusyBox
- Red: PDoS (Process Denial of Service), RCE (Remote Code Execution)
- Blue: Malware (v_malware), Miori, Mirai
- Green: v? (unknown malware?), credential reset
- **Arrows**: Labeled with actions (e.g., "launch-by", "mitigate-by", "target-by")
- **Boxes**:
- `q`: Basic threat scenario
- `q+`: Enhanced threat scenario with credential reset
- `q ∧ q+`: Combined threat scenario
---
### Detailed Analysis
#### Diagram (a): Basic Threat (`q`)
- **Flow**:
- BusyBox → PDoS via "launch-by"
- PDoS → Malware (v_malware) via "launch-by"
- Malware → v? via "mitigate-by"
- **Key Labels**:
- "target-by" (BusyBox → v_malware)
- "launch-by" (PDoS → Malware)
- "mitigate-by" (Malware → v?)
#### Diagram (b): Enhanced Threat (`q+`)
- **Flow**:
- Mirai → Miori via "mitigate-by"
- Miori → a* (credential reset) via "credential reset"
- Mirai → a* via "mitigate-by"
- **Key Labels**:
- "mitigate-by" (Mirai → Miori, Mirai → a*)
- "credential reset" (Miori → a*)
#### Diagram (c): DDoS and RCE Integration (`q+`)
- **Flow**:
- DDoS → Miori via "launch-by"
- RCE → Miori via "launch-by"
- Miori → Credential Reset via "mitigate-by"
- **Key Labels**:
- "launch-by" (DDoS → Miori, RCE → Miori)
- "mitigate-by" (Miori → Credential Reset)
#### Diagram (d): Combined Threat (`q ∧ q+`)
- **Flow**:
- BusyBox → PDoS via "launch-by"
- PDoS → Malware (v_malware) via "launch-by"
- Malware → v? via "mitigate-by"
- RCE → Malware via "launch-by"
- BusyBox → v_malware via "target-by"
- **Key Labels**:
- "target-by" (BusyBox → v_malware)
- "launch-by" (RCE → Malware)
- "mitigate-by" (Malware → v?)
---
### Key Observations
1. **Threat Escalation**:
- `q` → `q+` → `q ∧ q+` shows increasing complexity, with credential reset (`a*`) and RCE integration.
2. **Mitigation Pathways**:
- "mitigate-by" actions appear in all diagrams, targeting malware (v_malware) and credential reset (a*).
3. **Actor Roles**:
- BusyBox and RCE act as initiators ("launch-by"), while Miori/Mirai serve as intermediaries.
4. **Credential Reset**:
- Appears as both a defensive mechanism (a*) and a threat actor (Miori).
---
### Interpretation
The diagrams model a layered malware attack lifecycle:
1. **Initialization**: BusyBox/RCE launch PDoS/DDoS to disrupt services.
2. **Malware Deployment**: PDoS/Miori deploy malware (v_malware) or credential reset (a*).
3. **Mitigation**: Defenders (v?, credential reset) attempt to neutralize threats.
4. **Synergy**: Combined threats (`q ∧ q+`) suggest attackers exploit multiple vectors (e.g., DDoS