## Heatmap: Query Path Effectiveness Across Backdoor and Targeted Scenarios
### Overview
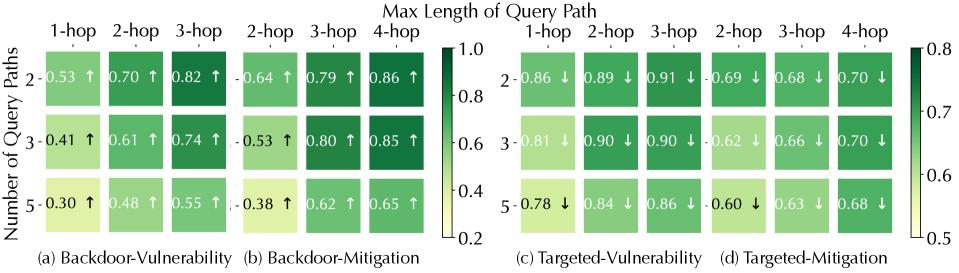
The image presents a comparative heatmap analysis of query path effectiveness in four scenarios: Backdoor-Vulnerability, Backdoor-Mitigation, Targeted-Vulnerability, and Targeted-Mitigation. The data is organized into 3x4 grids (rows = number of query paths [2, 3, 5]; columns = max query path length [1-hop to 4-hop]). Color intensity (green gradient) and numerical values indicate effectiveness, with arrows showing directional trends.
---
### Components/Axes
- **Y-Axis (Left)**: "Number of Query Paths" (values: 2, 3, 5)
- **X-Axis (Top)**: "Max Length of Query Path" (values: 1-hop, 2-hop, 3-hop, 4-hop)
- **Legend (Right)**: Color scale from 0.2 (light yellow) to 1.0 (dark green), representing effectiveness magnitude.
- **Sub-Figures**:
- (a) Backdoor-Vulnerability
- (b) Backdoor-Mitigation
- (c) Targeted-Vulnerability
- (d) Targeted-Mitigation
---
### Detailed Analysis
#### (a) Backdoor-Vulnerability
- **Trend**: Effectiveness increases with both query paths and hop length.
- Example: 5-query paths, 4-hop = **0.55** (↑)
- **Key Values**:
- 2-query paths: 0.53 (1-hop), 0.70 (2-hop), 0.82 (3-hop), 0.64 (4-hop)
- 3-query paths: 0.41 (1-hop), 0.61 (2-hop), 0.74 (3-hop), 0.53 (4-hop)
- 5-query paths: 0.30 (1-hop), 0.48 (2-hop), 0.55 (3-hop), 0.38 (4-hop)
#### (b) Backdoor-Mitigation
- **Trend**: Effectiveness decreases with longer hop lengths but improves with more query paths.
- Example: 5-query paths, 4-hop = **0.65** (↑)
- **Key Values**:
- 2-query paths: 0.64 (1-hop), 0.79 (2-hop), 0.86 (3-hop), 0.86 (4-hop)
- 3-query paths: 0.53 (1-hop), 0.80 (2-hop), 0.85 (3-hop), 0.85 (4-hop)
- 5-query paths: 0.38 (1-hop), 0.62 (2-hop), 0.65 (3-hop), 0.65 (4-hop)
#### (c) Targeted-Vulnerability
- **Trend**: Effectiveness decreases with longer hop lengths but stabilizes at higher query paths.
- Example: 5-query paths, 4-hop = **0.68** (↓)
- **Key Values**:
- 2-query paths: 0.86 (1-hop), 0.89 (2-hop), 0.91 (3-hop), 0.69 (4-hop)
- 3-query paths: 0.81 (1-hop), 0.90 (2-hop), 0.90 (3-hop), 0.62 (4-hop)
- 5-query paths: 0.78 (1-hop), 0.84 (2-hop), 0.86 (3-hop), 0.60 (4-hop)
#### (d) Targeted-Mitigation
- **Trend**: Effectiveness decreases with longer hop lengths and fewer query paths.
- Example: 2-query paths, 4-hop = **0.70** (↓)
- **Key Values**:
- 2-query paths: 0.86 (1-hop), 0.89 (2-hop), 0.91 (3-hop), 0.69 (4-hop)
- 3-query paths: 0.81 (1-hop), 0.90 (2-hop), 0.90 (3-hop), 0.62 (4-hop)
- 5-query paths: 0.78 (1-hop), 0.84 (2-hop), 0.86 (3-hop), 0.60 (4-hop)
---
### Key Observations
1. **Backdoor Scenarios**:
- Vulnerability peaks at 3-hop for 2-query paths (0.82 in (a)).
- Mitigation improves with more query paths (e.g., 5-query paths, 4-hop = 0.65 in (b)).
2. **Targeted Scenarios**:
- Vulnerability remains high even at 4-hop (0.68–0.91 in (c)).
- Mitigation effectiveness drops sharply at 4-hop (0.60–0.70 in (d)).
3. **Color Consistency**:
- Darker greens (closer to 1.0) dominate Backdoor-Mitigation (b) and Targeted-Vulnerability (c).
- Lighter greens (closer to 0.5) appear in Backdoor-Vulnerability (a) and Targeted-Mitigation (d).
---
### Interpretation
- **Query Path Trade-offs**: Increasing query paths generally improves mitigation (e.g., 5-query paths in (b) vs. 2-query paths) but may reduce vulnerability in targeted scenarios (e.g., 5-query paths in (c) vs. 2-query paths).
- **Hop Length Impact**: Longer hop lengths (4-hop) correlate with reduced mitigation effectiveness across all scenarios, suggesting complexity limits defensive strategies.
- **Targeted vs. Backdoor**: Targeted scenarios show higher vulnerability (0.78–0.91 in (c)) but also stronger mitigation (0.60–0.91 in (d)) compared to backdoor cases, indicating tailored attacks exploit system weaknesses more effectively.
The data underscores the importance of balancing query path complexity and length to optimize security outcomes, with targeted attacks demanding more nuanced mitigation strategies.