## Heatmap: Vulnerability and Mitigation Strategies
### Overview
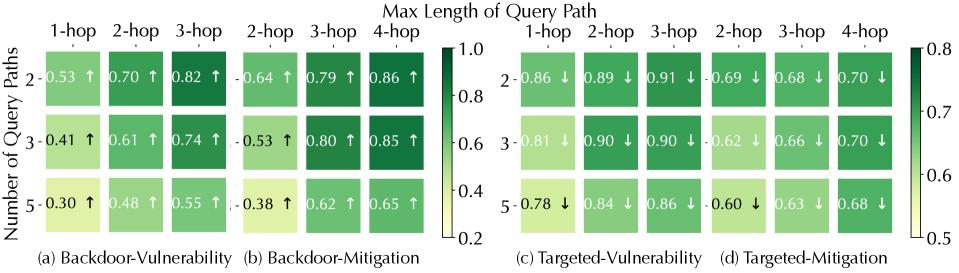
The image presents four heatmaps comparing vulnerability and mitigation strategies for backdoor and targeted attacks. The heatmaps visualize the relationship between the number of query paths (2, 3, and 5) and the maximum length of the query path (1-hop, 2-hop, 3-hop, and 4-hop). The color intensity represents the effectiveness of the strategy, with darker green indicating higher effectiveness and lighter yellow indicating lower effectiveness. Each cell contains a numerical value and an arrow indicating the trend (increase or decrease).
### Components/Axes
* **Title:** Max Length of Query Path
* **Y-axis Title:** Number of Query Paths
* **Y-axis Labels:** 2, 3, 5
* **X-axis Labels (Backdoor-Vulnerability):** 1-hop, 2-hop, 3-hop
* **X-axis Labels (Backdoor-Mitigation):** 2-hop, 3-hop, 4-hop
* **X-axis Labels (Targeted-Vulnerability):** 1-hop, 2-hop, 3-hop
* **X-axis Labels (Targeted-Mitigation):** 2-hop, 3-hop, 4-hop
* **Color Scale:** Ranges from approximately 0.2 (light yellow) to 1.0 (dark green) on the left side, and from 0.5 to 0.8 on the right side.
* **Subplot Titles:** (a) Backdoor-Vulnerability, (b) Backdoor-Mitigation, (c) Targeted-Vulnerability, (d) Targeted-Mitigation
* **Trend Indicators:** Upward arrow (↑) indicates an increasing trend, downward arrow (↓) indicates a decreasing trend.
### Detailed Analysis
#### (a) Backdoor-Vulnerability
| Number of Query Paths | 1-hop | 2-hop | 3-hop |
| :-------------------- | :----- | :----- | :----- |
| 2 | 0.53 ↑ | 0.70 ↑ | 0.82 ↑ |
| 3 | 0.41 ↑ | 0.61 ↑ | 0.74 ↑ |
| 5 | 0.30 ↑ | 0.48 ↑ | 0.55 ↑ |
* **Trend:** The values increase as the hop length increases for each number of query paths.
#### (b) Backdoor-Mitigation
| Number of Query Paths | 2-hop | 3-hop | 4-hop |
| :-------------------- | :----- | :----- | :----- |
| 2 | 0.64 ↑ | 0.79 ↑ | 0.86 ↑ |
| 3 | 0.53 ↑ | 0.80 ↑ | 0.85 ↑ |
| 5 | 0.38 ↑ | 0.62 ↑ | 0.65 ↑ |
* **Trend:** The values increase as the hop length increases for each number of query paths.
#### (c) Targeted-Vulnerability
| Number of Query Paths | 1-hop | 2-hop | 3-hop |
| :-------------------- | :----- | :----- | :----- |
| 2 | 0.86 ↓ | 0.89 ↓ | 0.91 ↓ |
| 3 | 0.81 ↓ | 0.90 ↓ | 0.90 ↓ |
| 5 | 0.78 ↓ | 0.84 ↓ | 0.86 ↓ |
* **Trend:** The values are generally high (dark green) and decrease slightly as the number of query paths increases.
#### (d) Targeted-Mitigation
| Number of Query Paths | 2-hop | 3-hop | 4-hop |
| :-------------------- | :----- | :----- | :----- |
| 2 | 0.69 ↓ | 0.68 ↓ | 0.70 ↓ |
| 3 | 0.62 ↓ | 0.66 ↓ | 0.70 ↓ |
| 5 | 0.60 ↓ | 0.63 ↓ | 0.68 ↓ |
* **Trend:** The values are relatively consistent across different hop lengths and decrease slightly as the number of query paths increases.
### Key Observations
* **Backdoor-Vulnerability:** Vulnerability increases significantly with longer query paths.
* **Backdoor-Mitigation:** Mitigation effectiveness also increases with longer query paths.
* **Targeted-Vulnerability:** Vulnerability is generally high but decreases slightly with more query paths.
* **Targeted-Mitigation:** Mitigation effectiveness is relatively stable and decreases slightly with more query paths.
* The color scales are different for the left and right heatmaps. The left heatmaps range from 0.2 to 1.0, while the right heatmaps range from 0.5 to 0.8.
### Interpretation
The heatmaps suggest that for backdoor attacks, longer query paths increase both vulnerability and the effectiveness of mitigation strategies. This indicates a trade-off where longer paths might be more susceptible to exploitation but also more amenable to defense. For targeted attacks, vulnerability is generally high, and mitigation strategies show a relatively stable effectiveness, with a slight decrease as the number of query paths increases. This could imply that targeted attacks are inherently more difficult to defend against, and increasing the number of query paths does not significantly improve mitigation. The different color scales between the left and right heatmaps suggest that the range of effectiveness is different for backdoor and targeted attacks, with targeted attacks having a narrower range.