\n
## Diagram: Transient Execution Attack Classification
### Overview
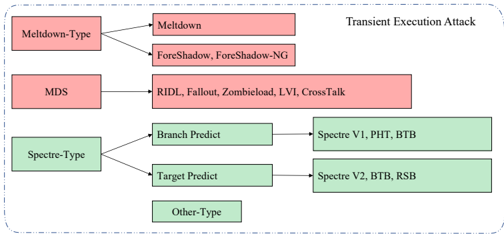
The image is a diagram illustrating a classification of Transient Execution Attacks. It categorizes these attacks into three main types: Meltdown-Type, MDS, and Spectre-Type, and then further breaks down each type into specific attack variants. The diagram uses boxes and arrows to show the relationships between the attack types and their sub-categories.
### Components/Axes
The diagram consists of:
* **Main Categories:** Meltdown-Type, MDS, Spectre-Type, Other-Type. These are represented by rectangular boxes on the left side of the diagram.
* **Attack Variants:** Specific attacks falling under each category. These are represented by rectangular boxes on the right side of the diagram.
* **Arrows:** Arrows connect the main categories to their corresponding attack variants, indicating a "is a type of" relationship.
* **Title:** "Transient Execution Attack" located in the top-right corner.
* **Color Coding:** Meltdown-Type and MDS attacks are represented with a reddish-pink color, while Spectre-Type and Other-Type attacks are represented with a light green color.
### Detailed Analysis or Content Details
The diagram details the following relationships:
* **Meltdown-Type:**
* Meltdown
* Foreshadow, Foreshadow-NG
* **MDS:**
* RIDL, Fallout, Zombieload, LVI, CrossTalk
* **Spectre-Type:**
* Branch Predict -> Spectre V1, PHT, BTB
* Target Predict -> Spectre V2, BTB, RSB
* **Other-Type:** No specific attacks are listed under this category.
### Key Observations
The diagram clearly categorizes the different types of transient execution attacks. The color coding helps to visually distinguish between the Meltdown/MDS and Spectre attack families. The diagram does not provide any quantitative data or trends, but rather a qualitative classification. The "Other-Type" category is present but empty, suggesting that there may be other transient execution attacks that don't fit neatly into the defined categories.
### Interpretation
This diagram serves as a taxonomy of transient execution attacks. It demonstrates how these attacks can be grouped based on their underlying mechanisms. The classification is useful for understanding the landscape of these vulnerabilities and for developing mitigation strategies. The separation into Meltdown, MDS, and Spectre types reflects fundamental differences in how these attacks exploit processor vulnerabilities.
* **Meltdown** attacks exploit speculative execution to gain access to kernel memory.
* **MDS** attacks exploit microarchitectural data sampling to leak sensitive information.
* **Spectre** attacks trick the processor into speculatively executing instructions that it wouldn't normally execute, leading to information leakage.
The inclusion of specific attack names (e.g., Foreshadow, RIDL, Spectre V1) highlights the diversity of these attacks and the ongoing research into new variants. The empty "Other-Type" category suggests that the field is still evolving and that new attack vectors may emerge. The diagram is a high-level overview and doesn't delve into the technical details of each attack.