## Diagram: Taxonomy of Transient Execution Attacks
### Overview
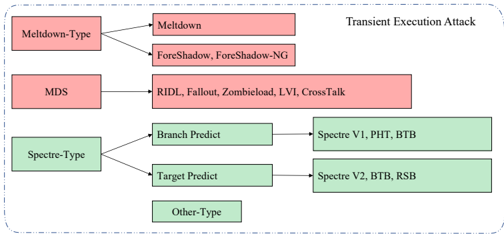
The image is a hierarchical classification diagram (taxonomy) illustrating different families and specific examples of transient execution attacks in computer security. It organizes attacks into three primary categories, with some further subdivided, and includes a separate, unconnected category. The diagram uses color-coding and directional arrows to show relationships.
### Components/Axes
* **Title:** Located in the top-right corner: "Transient Execution Attack".
* **Primary Categories (Left Column):**
* `Meltdown-Type` (Red box)
* `MDS` (Red box)
* `Spectre-Type` (Green box)
* **Secondary Categories/Examples (Middle & Right Columns):**
* Connected to `Meltdown-Type`:
* `Meltdown` (Red box)
* `ForeShadow, ForeShadow-NG` (Red box)
* Connected to `MDS`:
* `RIDL, Fallout, Zombieload, LVI, CrossTalk` (Red box)
* Connected to `Spectre-Type`:
* `Branch Predict` (Green box) → leads to `Spectre V1, PHT, BTB` (Green box)
* `Target Predict` (Green box) → leads to `Spectre V2, BTB, RSB` (Green box)
* **Standalone Element:**
* `Other-Type` (Green box, positioned below the Spectre hierarchy, with no connecting arrows).
* **Visual Structure:** The diagram flows from left to right. Primary categories on the left branch out via arrows to their constituent attack types or specific attack names on the right. The entire diagram is enclosed in a dashed-line border.
### Detailed Analysis
The taxonomy is structured as follows:
1. **Meltdown-Type Family (Red):**
* This category branches into two specific attack groups.
* The first is the foundational `Meltdown` attack.
* The second is `ForeShadow` and its variant `ForeShadow-NG`.
2. **MDS Family (Red):**
* MDS (Microarchitectural Data Sampling) is presented as a distinct primary category.
* It encompasses a list of specific attacks: `RIDL`, `Fallout`, `Zombieload`, `LVI`, and `CrossTalk`.
3. **Spectre-Type Family (Green):**
* This category is subdivided based on the prediction mechanism exploited.
* **Branch Predict:** This sub-type leads to `Spectre V1` and attacks targeting the `PHT` (Pattern History Table) and `BTB` (Branch Target Buffer).
* **Target Predict:** This sub-type leads to `Spectre V2` and attacks targeting the `BTB` and `RSB` (Return Stack Buffer).
* Note: The `BTB` is listed under both sub-types, indicating it is a target for multiple Spectre variants.
4. **Other-Type (Green):**
* This is a standalone, unconnected box, suggesting a category for transient execution attacks that do not fall under the Meltdown, MDS, or Spectre classifications as defined in this diagram.
### Key Observations
* **Color Coding:** A clear visual distinction is made between attack families. `Meltdown-Type` and `MDS` are colored red, while `Spectre-Type` and `Other-Type` are colored green. This likely groups attacks by their fundamental mechanism or discovery lineage.
* **Structural Difference:** The `Spectre-Type` category has a more complex, two-level hierarchy (Type → Prediction Mechanism → Specific Attacks/Variants) compared to the single-level branching of `Meltdown-Type` and the flat list of `MDS`.
* **Component Overlap:** The `BTB` (Branch Target Buffer) is explicitly listed as a target under both the `Branch Predict` and `Target Predict` sub-categories of Spectre.
* **Isolated Element:** The `Other-Type` box is visually isolated, indicating it is a catch-all category not integrated into the main relational flow of the diagram.
### Interpretation
This diagram serves as a conceptual map for understanding the landscape of transient execution attacks, which exploit speculative execution in modern CPUs. It demonstrates that these attacks are not monolithic but belong to distinct families with different root causes:
* The **red group (Meltdown, MDS)** typically involves attacks that exploit speculative execution to read data from the CPU's internal buffers and caches, often bypassing basic privilege boundaries.
* The **green group (Spectre)** primarily involves attacks that trick the CPU's branch predictors into speculatively executing code paths that leak data, exploiting the blurring of privilege boundaries between different security domains (e.g., between different processes or between user space and kernel space).
* The separation of `Spectre-Type` into `Branch Predict` and `Target Predict` highlights a key technical distinction in how the speculation is misdirected.
* The inclusion of `Other-Type` acknowledges that the taxonomy is not exhaustive and that the field of transient execution attacks continues to evolve, with new attack variants potentially falling outside these established categories.
The diagram effectively communicates that while these attacks share the high-level characteristic of using transient (speculative) execution, their specific mechanisms, targets, and the hardware structures they exploit (PHT, BTB, RSB) are diverse. This categorization is crucial for developing targeted mitigations.