TECHNICAL ASSET FINGERPRINT
e981e40c421396e60b625e3c
Click to view fullscreen
Press ESC or click to close
FOUND IN PAPERS
EXPERT: gemini-2.0-flash VERSION 1
RUNTIME: nugit/gemini/gemini-2.0-flash
INTEL_VERIFIED
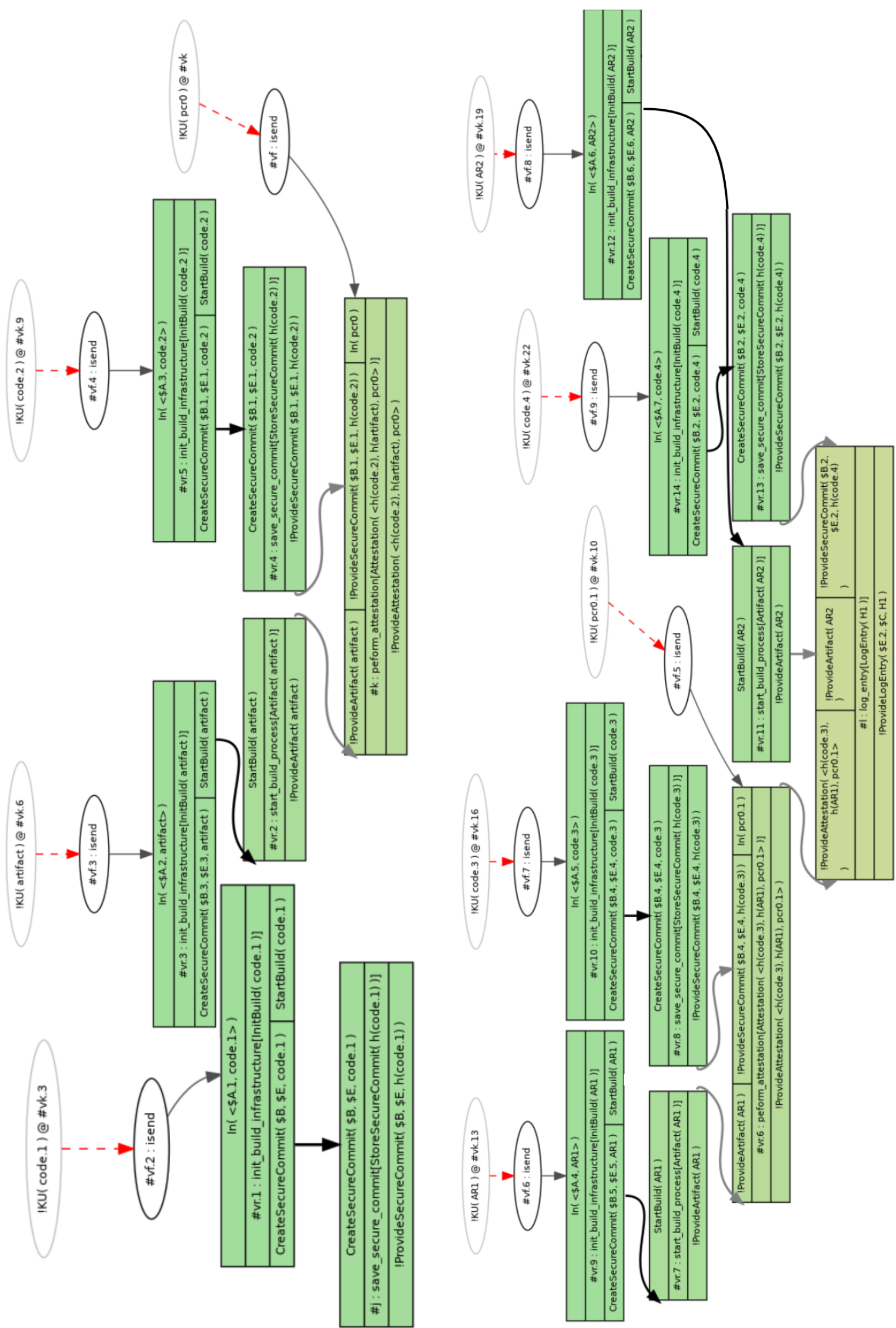
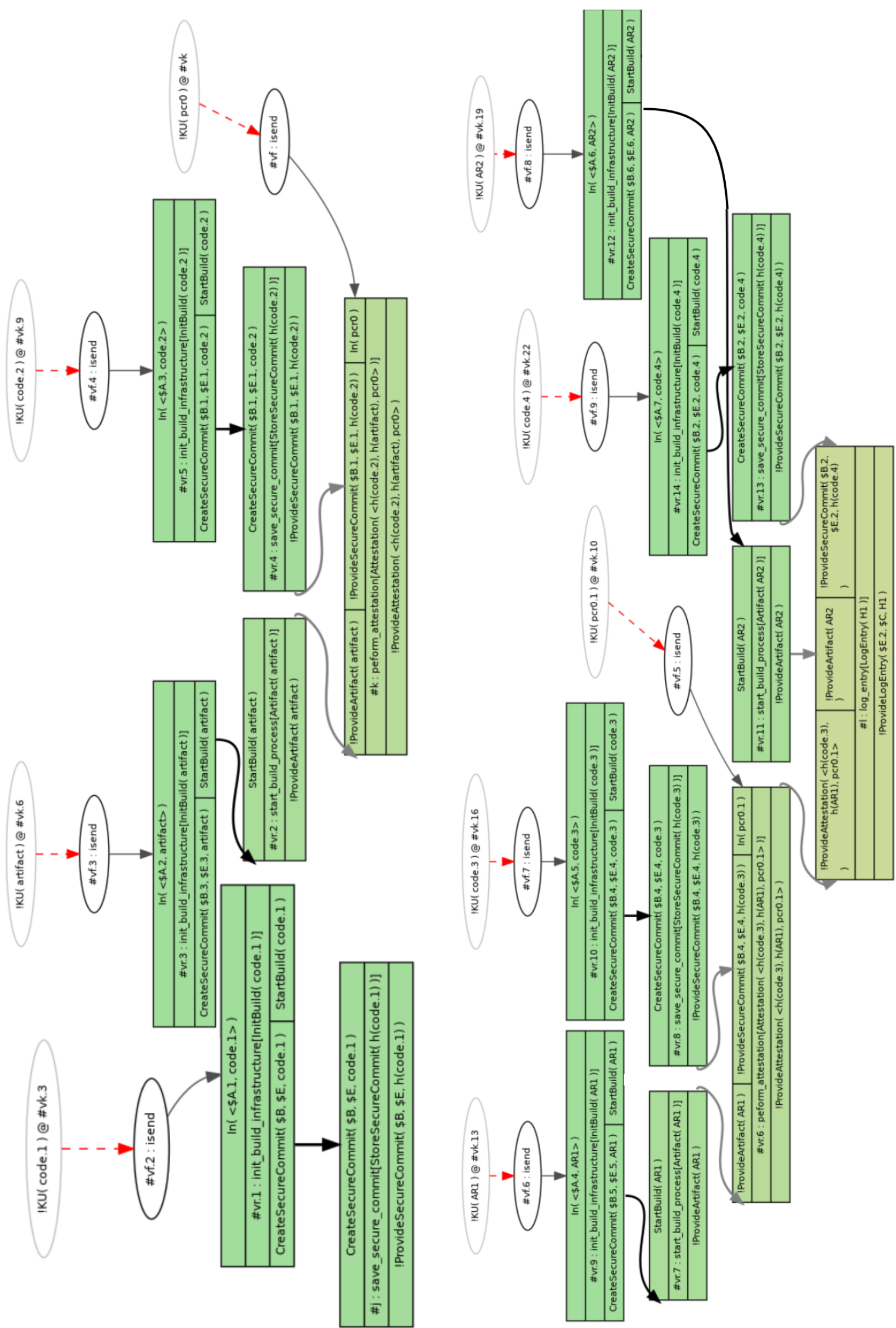
## Diagram: Build Infrastructure and Secure Commit Process
### Overview
The image presents two similar diagrams illustrating a build infrastructure and secure commit process. Each diagram depicts a series of steps involving initialization, secure commit creation, and attestation, with variations in the artifacts and parameters used. The diagrams use nodes to represent processes and edges to represent the flow of data or control.
### Components/Axes
* **Nodes:** Represented as rounded rectangles (green) or ovals (gray). Green rectangles contain process descriptions, while gray ovals denote entities like `!KU(code.x) @ #vk.y` or `!KU(ARx) @ #vk.y` or `!KU(pcr0.x) @ #vk.y`.
* **Edges:** Represented as arrows, indicating the flow of data or control. Black arrows indicate a standard flow, while dashed red arrows indicate a specific type of interaction (likely an "isend" operation). Gray arrows indicate attestation or artifact provision.
* **Labels:** Each node has a label indicating its function or state, such as `#vr.1: init_build_infrastructure[InitBuild(code.1)]` or `#vr.4: save_secure_commit[StoreSecureCommit(h(code.2))]`.
* **Entities:** `!KU(code.x) @ #vk.y`, `!KU(ARx) @ #vk.y`, `!KU(pcr0.x) @ #vk.y` represent entities with attributes like code version, artifact version, or PCR (Platform Configuration Register) values.
* **Operations:** `#vf.x: isend` represents an "isend" operation, likely indicating a message send.
### Detailed Analysis or ### Content Details
**Left Diagram:**
1. **Top-Left Node:** `!KU(code.1) @ #vk.3`
2. **Second Node:** `#vf.2: isend`
3. **Third Node (Green Rectangle):**
* `In(<$A.1, code.1>)`
* `#vr.1: init_build_infrastructure[InitBuild(code.1)]`
* `CreateSecureCommit($B, $E, code.1)`
* `StartBuild(code.1)`
4. **Fourth Node (Green Rectangle):**
* `#j: save_secure_commit[StoreSecureCommit(h(code.1))]`
* `!Provide SecureCommit($B, $E, h(code.1))`
5. **Fifth Node (Top):** `!KU(code.2) @ #vk.9`
6. **Sixth Node:** `#vf.4: isend`
7. **Seventh Node (Green Rectangle):**
* `In(<$A.3, code.2>)`
* `#vr.5: init_build_infrastructure[InitBuild(code.2)]`
* `CreateSecureCommit($B.1, $E.1, code.2)`
* `StartBuild(code.2)`
8. **Eighth Node (Green Rectangle):**
* `#vr.4: save_secure_commit[StoreSecureCommit(h(code.2))]`
* `!Provide SecureCommit($B.1, $E.1, h(code.2))`
9. **Ninth Node (Top):** `!KU(pcr0) @ #vk`
10. **Tenth Node (Green Rectangle):**
* `!Provide SecureCommit($B.1, $E.1, h(code.2)) In(pcr0)`
* `#k: peform_attestation [Attestation(<h(code.2), h(artifact), pcr0>)]`
* `!Provide Attestation( <h(code.2), h(artifact), pcr0>)`
11. **Eleventh Node (Top):** `!KU(artifact) @ #vk.6`
12. **Twelfth Node:** `#vf.3: isend`
13. **Thirteenth Node (Green Rectangle):**
* `In(<$A.2, artifact>)`
* `#vr.3: init_build_infrastructure[InitBuild(artifact)]`
* `CreateSecureCommit($B.3, $E.3, artifact) StartBuild(artifact)`
14. **Fourteenth Node (Green Rectangle):**
* `#vr.2: start_build_process[Artifact(artifact)]`
* `!Provide Artifact(artifact)`
15. **Fifteenth Node (Green Rectangle):**
* `!ProvideArtifact( artifact )`
**Right Diagram:**
1. **Top-Left Node:** `!KU(AR1) @ #vk.13`
2. **Second Node:** `#vf.6: isend`
3. **Third Node (Green Rectangle):**
* `In(<$A.4, AR1>)`
* `#vr.9: init_build_infrastructure [InitBuild(AR1)]`
* `CreateSecureCommit($B.5, $E.5, AR1)`
* `StartBuild(AR1)`
4. **Fourth Node (Green Rectangle):**
* `#vr.7: start_build_process[Artifact(AR1)]`
* `!Provide Artifact (AR1)`
5. **Fifth Node (Top):** `!KU(code.3) @ #vk.16`
6. **Sixth Node:** `#vf.7: isend`
7. **Seventh Node (Green Rectangle):**
* `In(<$A.5, code.3>)`
* `#vr.10: init_build_infrastructure[InitBuild(code.3)]`
* `CreateSecureCommit($B.4, $E.4, code.3)`
* `StartBuild(code.3)`
8. **Eighth Node (Green Rectangle):**
* `#vr.8: save_secure_commit[StoreSecureCommit(h(code.3))]`
* `!Provide SecureCommit($B.4. $E.4, h(code.3))`
9. **Ninth Node (Top):** `!KU(code.4) @ #vk.22`
10. **Tenth Node:** `#vf.9: isend`
11. **Eleventh Node (Green Rectangle):**
* `In(<$A.7, code.4>)`
* `#vr.14: init_build_infrastructure[InitBuild(code.4)]`
* `CreateSecureCommit($B.2. $E.2, code.4)`
* `StartBuild(code.4)`
12. **Twelfth Node (Green Rectangle):**
* `#vr.13: save_secure_commit[StoreSecureCommit(h(code.4))]`
* `!Provide SecureCommit($B.2, $E.2, h(code.4))`
13. **Thirteenth Node (Top):** `!KU(pcr0.1) @ #vk.10`
14. **Fourteenth Node:** `#vf.5: isend`
15. **Fifteenth Node (Top):** `!KU(AR2) @ #vk.19`
16. **Sixteenth Node:** `#vf.8: isend`
17. **Seventeenth Node (Green Rectangle):**
* `In(<$A.6, AR2>)`
* `#vr.12: init_build_infrastructure[InitBuild(AR2)]`
* `CreateSecureCommit($B.6. $E.6, AR2) StartBuild(AR2)`
18. **Eighteenth Node (Green Rectangle):**
* `#vr.11: start_build_process [Artifact( AR2)]`
* `!Provide Artifact(AR2)`
19. **Nineteenth Node (Green Rectangle):**
* `!ProvideArtifact( AR2 )`
20. **Twentieth Node (Green Rectangle):**
* `!Provide SecureCommit($B.4, $E.4, h(code.3))`
* `#vr.6: peform_attestation[Attestation(<h(code.3), h(AR1), pcr0.1>)]`
* `!Provide Attestation(<h(code.3), h(AR1), pcr0.1>)`
21. **Twenty-First Node (Green Rectangle):**
* `#1: log_entry[LogEntry(H1)]`
* `!Provide LogEntry($E.2, $C, H1)`
### Key Observations
* Both diagrams follow a similar pattern: initialization, secure commit, and attestation.
* The left diagram uses `code.1`, `code.2`, and `artifact` as parameters, while the right diagram uses `AR1`, `code.3`, `code.4`, and `AR2`.
* The `isend` operations (`#vf.x: isend`) appear to trigger the initialization processes.
* The attestation process involves PCR values and hash values of artifacts.
### Interpretation
The diagrams illustrate a process for securely building and committing code and artifacts. The process involves initializing a build infrastructure, creating secure commits, and performing attestation to ensure the integrity of the build process. The variations in parameters (code versions, artifact versions, PCR values) suggest that the process can be adapted to different types of builds and artifacts. The use of "isend" operations suggests a distributed or asynchronous build process. The attestation step is crucial for verifying the integrity of the build and ensuring that the resulting artifacts are trustworthy. The log entry at the end of the right diagram suggests that the entire process is auditable.
DECODING INTELLIGENCE...
EXPERT: gemma-3-27b-it-free VERSION 1
RUNTIME: google-free/gemma-3-27b-it
INTEL_VERIFIED
\n
## Flowchart: Process Flow Diagram
### Overview
This image depicts a complex flowchart illustrating a process with multiple decision points, loops, and parallel paths. The flowchart appears to model a system involving "Commitment" and "Procurement" processes, with various checks and balances. The diagram uses rectangular boxes for processes, diamonds for decisions, and ovals for start/end points. Arrows indicate the flow of the process.
### Components/Axes
The diagram does not have traditional axes. Instead, it relies on the visual arrangement of components and the direction of arrows to convey the process flow. Key components include:
* **Start:** Oval labeled "Start"
* **End:** Oval labeled "#4 paid" (appears multiple times)
* **Process Boxes:** Rectangular boxes containing descriptions of actions or steps.
* **Decision Diamonds:** Diamond-shaped boxes containing conditions or questions.
* **Arrows:** Indicate the direction of the process flow.
* **Labels:** Text within boxes and diamonds describing the process steps or conditions.
* **Variables:** Text within boxes like "N=1 (<=3)", "N=2 (>=4)", "K01 (<=2) @ 6%"
* **Text annotations:** Text annotations like "paid", "closed", "discarded"
### Detailed Analysis or Content Details
The flowchart can be broken down into several key paths:
**1. Initial Path (Left Side):**
* **Start** -> "Create/secure commitment (level 1)" -> "ProcurementCommitmentK01 (<= 1)"
* **Decision:** "ProcurementCommitmentK01 (<= 1)?"
* **Yes:** -> "N=1 Mill local/international (code 1) Supplier (detail 1)" -> "N=1 paid" -> "#4 paid"
* **No:** -> "ProcurementCommitmentK02 (<= 2)"
* **Decision:** "ProcurementCommitmentK02 (<= 2)?"
* **Yes:** -> "N=2 Mill local/international (code 2) Supplier (detail 2)" -> "N=2 paid" -> "#4 paid"
* **No:** -> "ProcurementCommitmentK03 (<= 3)"
* **Decision:** "ProcurementCommitmentK03 (<= 3)?"
* **Yes:** -> "N=3 Mill local/international (code 3) Supplier (detail 3)" -> "N=3 paid" -> "#4 paid"
* **No:** -> "ProcurementCommitmentK04 (<= 4)"
* **Decision:** "ProcurementCommitmentK04 (<= 4)?"
* **Yes:** -> "N=4 Mill local/international (code 4) Supplier (detail 4)" -> "N=4 paid" -> "#4 paid"
* **No:** -> "discarded"
**2. Middle Path:**
* "Create secure commitment K01 (<=2)" -> "ProcurementK01 (<= 2)?"
* **Yes:** -> "K01 (<=2) @ 6%" -> "#4 paid"
* **No:** -> "ProcurementK02 (<= 3)?"
* **Yes:** -> "K02 (<=3) @ 5%" -> "#4 paid"
* **No:** -> "ProcurementK03 (<= 4)?"
* **Yes:** -> "K03 (<=4) @ 4%" -> "#4 paid"
* **No:** -> "ProcurementK04 (<= 5)?"
* **Yes:** -> "K04 (<=5) @ 3%" -> "#4 paid"
* **No:** -> "ProcurementK05 (<= 6)?"
* **Yes:** -> "K05 (<=6) @ 2%" -> "#4 paid"
* **No:** -> "ProcurementK06 (<= 7)?"
* **Yes:** -> "K06 (<=7) @ 1%" -> "#4 paid"
* **No:** -> "discarded"
**3. Right Side Path:**
* "Create secure commitment K02 (<= 2)" -> "ProcurementCommitmentK02 (<= 2)?"
* **Yes:** -> "ProcurementCommitmentK02 (<= 2) Mill local/international (code 1) Supplier (detail 1)" -> "#4 paid"
* **No:** -> "ProcurementCommitmentK03 (<= 3)?"
* **Yes:** -> "ProcurementCommitmentK03 (<= 3) Mill local/international (code 2) Supplier (detail 2)" -> "#4 paid"
* **No:** -> "ProcurementCommitmentK04 (<= 4)?"
* **Yes:** -> "ProcurementCommitmentK04 (<= 4) Mill local/international (code 3) Supplier (detail 3)" -> "#4 paid"
* **No:** -> "ProcurementCommitmentK05 (<= 5)?"
* **Yes:** -> "ProcurementCommitmentK05 (<= 5) Mill local/international (code 4) Supplier (detail 4)" -> "#4 paid"
* **No:** -> "discarded"
**4. Bottom Path:**
* "Create secure commitment K03 (<= 2)" -> "ProcurementCommitmentK03 (<= 2)?"
* **Yes:** -> "ProcurementCommitmentK03 (<= 2) Mill local/international (code 1) Supplier (detail 1)" -> "#4 paid"
* **No:** -> "ProcurementCommitmentK04 (<= 3)?"
* **Yes:** -> "ProcurementCommitmentK04 (<= 3) Mill local/international (code 2) Supplier (detail 2)" -> "#4 paid"
* **No:** -> "ProcurementCommitmentK05 (<= 4)?"
* **Yes:** -> "ProcurementCommitmentK05 (<= 4) Mill local/international (code 3) Supplier (detail 3)" -> "#4 paid"
* **No:** -> "ProcurementCommitmentK06 (<= 5)?"
* **Yes:** -> "ProcurementCommitmentK06 (<= 5) Mill local/international (code 4) Supplier (detail 4)" -> "#4 paid"
* **No:** -> "discarded"
### Key Observations
* The flowchart has multiple paths leading to "#4 paid", indicating successful completion of the process.
* The "discarded" outcome suggests a failure or rejection point in the process.
* The decision points are based on numerical thresholds (e.g., "K01 (<= 2)?", "ProcurementCommitmentK01 (<= 1)?").
* The process involves multiple levels of "Commitment" (K01, K02, K03) and "Procurement" (ProcurementK01, ProcurementK02, etc.).
* The process appears to be tiered, with different paths based on the value of commitment levels.
* The percentages associated with K01-K06 (6%, 5%, 4%, 3%, 2%, 1%) likely represent some form of cost or fee.
### Interpretation
This flowchart represents a complex procurement and commitment process with multiple decision points and potential outcomes. The process seems designed to handle varying levels of commitment and procurement, with different paths based on numerical thresholds. The "discarded" outcome suggests a quality control or rejection mechanism. The percentages associated with the K values likely represent fees or costs associated with each level of commitment. The diagram suggests a hierarchical structure, where initial commitments are evaluated and then routed through a series of procurement steps. The repeated "#4 paid" outcome indicates a successful completion of the process, regardless of the specific path taken. The diagram is a visual representation of a business process, likely used for documentation, training, or process improvement. The complexity suggests a significant investment in process control and management.
DECODING INTELLIGENCE...
EXPERT: healer-alpha-free VERSION 1
RUNTIME: free/openrouter/healer-alpha
INTEL_VERIFIED
## Process Flow Diagram: Secure Build and Attestation Workflows
### Overview
The image displays a complex technical flowchart illustrating multiple parallel workflows for secure software build processes, infrastructure initialization, and attestation generation. The diagram is organized into several vertical lanes, each representing a distinct process flow initiated by a specific input. The primary language is English, with technical notation and identifiers.
### Components/Axes
The diagram is structured as a directed graph with the following key components:
1. **Starting Nodes (Ovals):** Located at the top of each vertical lane. Each is labeled with a pattern: `!KU( <identifier> ) @ #vk.<number>`. These represent the initiation points or inputs for each workflow.
2. **Intermediate Nodes (Ovals):** Labeled `#vf.<number> : isend`. These appear to be message or event forwarding steps.
3. **Process Steps (Green Rectangles):** The core of the diagram. Each box contains a step identifier (e.g., `#vr.1`), a descriptive function name, and parameters in parentheses. Steps are connected by arrows indicating sequence and data flow.
4. **Connectors:**
* **Solid Black Arrows:** Indicate the primary flow of control or data between process steps.
* **Red Dashed Arrows:** Connect the initial `!KU` nodes to the first `#vf` node in their respective lanes.
* **Grey Arrows:** Indicate secondary or data flow connections, often pointing to attestation or artifact provision steps.
### Detailed Analysis
The diagram details at least seven distinct, parallel workflows. Below is a transcription of the text and structure for each major lane, processed from left to right.
**Lane 1 (Far Left):**
* **Start:** `!KU( code.1 ) @ #vk.3`
* **Flow:** `#vf.2 : isend` → `In( <$A.1, code.1> )`
* **Process Steps:**
* `#vr.1 : init_build_infrastructure[InitBuild( code.1 )]`
* `CreateSecureCommit( $B, $E, code.1 )`
* `StartBuild( code.1 )`
* `#j : save_secure_commit[StoreSecureCommit( h(code.1) )]`
* `!ProvideSecureCommit( $B, $E, h(code.1) )`
**Lane 2:**
* **Start:** `!KU( artifact ) @ #vk.6`
* **Flow:** `#vf.3 : isend` → `In( <$A.2, artifact> )`
* **Process Steps:**
* `#vr.3 : init_build_infrastructure[InitBuild( artifact )]`
* `CreateSecureCommit( $B.3, $E.3, artifact )`
* `StartBuild( artifact )`
* `#vr.2 : start_build_process[Artifact( artifact )]`
* `!ProvideArtifact( artifact )`
**Lane 3:**
* **Start:** `!KU( code.2 ) @ #vk.9`
* **Flow:** `#vf.4 : isend` → `In( <$A.3, code.2> )`
* **Process Steps:**
* `#vr.5 : init_build_infrastructure[InitBuild( code.2 )]`
* `CreateSecureCommit( $B.1, $E.1, code.2 )`
* `StartBuild( code.2 )`
* `#vr.4 : save_secure_commit[StoreSecureCommit( h(code.2) )]`
* `!ProvideSecureCommit( $B.1, $E.1, h(code.2) )`
* `!ProvideAttestation( <h(code.2), h(artifact), pcr0> )`
* `#k : perform_attestation[Attestation( h(code.2), pcr0 )]`
* `!ProvideAttestation( <h(code.2), h(artifact), pcr0> )`
**Lane 4 (Center):**
* **Start:** `!KU( pcr0 ) @ #vk`
* **Flow:** `#vf.1 : isend` → `In( pcr0 )`
* **Process Step:**
* `!ProvideAttestation( <h(code.2), h(artifact), pcr0> )` (This step receives input from Lane 3).
**Lane 5:**
* **Start:** `!KU( code.3 ) @ #vk.16`
* **Flow:** `#vf.7 : isend` → `In( <$A.5, code.3> )`
* **Process Steps:**
* `#vr.10 : init_build_infrastructure[InitBuild( code.3 )]`
* `CreateSecureCommit( $B.4, $E.4, code.3 )`
* `StartBuild( code.3 )`
* `#vr.8 : save_secure_commit[StoreSecureCommit( h(code.3) )]`
* `!ProvideSecureCommit( $B.4, $E.4, h(code.3) )`
* `!ProvideAttestation( <h(code.3), h(AR1), pcr0.1> )`
* `#vr.9 : perform_attestation[Attestation( h(code.3), pcr0.1 )]`
* `!ProvideAttestation( <h(code.3), h(AR1), pcr0.1> )`
**Lane 6:**
* **Start:** `!KU( AR1 ) @ #vk.13`
* **Flow:** `#vf.6 : isend` → `In( <$A.4, AR1> )`
* **Process Steps:**
* `#vr.9 : init_build_infrastructure[InitBuild( AR1 )]`
* `CreateSecureCommit( $B.5, $E.5, AR1 )`
* `StartBuild( AR1 )`
* `#vr.7 : start_build_process[Artifact( AR1 )]`
* `!ProvideArtifact( AR1 )`
**Lane 7 (Right Side):**
* **Start:** `!KU( pcr0.1 ) @ #vk.10`
* **Flow:** `#vf.5 : isend` → `In( pcr0.1 )`
* **Process Step:**
* `#vr.11 : start_build_process[Artifact( AR2 )]`
* `!ProvideArtifact( AR2 )`
**Lane 8:**
* **Start:** `!KU( code.4 ) @ #vk.22`
* **Flow:** `#vf.9 : isend` → `In( <$A.7, code.4> )`
* **Process Steps:**
* `#vr.14 : init_build_infrastructure[InitBuild( code.4 )]`
* `CreateSecureCommit( $B.2, $E.2, code.4 )`
* `StartBuild( code.4 )`
* `#vr.13 : save_secure_commit[StoreSecureCommit( h(code.4) )]`
* `!ProvideSecureCommit( $B.2, $E.2, h(code.4) )`
**Lane 9 (Far Right):**
* **Start:** `!KU( AR2 ) @ #vk.19`
* **Flow:** `#vf.8 : isend` → `In( <$A.6, AR2> )`
* **Process Steps:**
* `#vr.12 : init_build_infrastructure[InitBuild( AR2 )]`
* `CreateSecureCommit( $B.6, $E.6, AR2 )`
* `StartBuild( AR2 )`
* **Additional Steps (connected via grey arrows):**
* `!ProvideSecureCommit( $B.2, $E.2, h(code.4) )` (from Lane 8)
* `#l : log_entry[LogEntry( H1 )]`
* `!ProvideLogEntry( $E.2, $C, H1 )`
### Key Observations
1. **Parallel Structure:** The diagram shows multiple independent but structurally similar workflows running in parallel, each handling different inputs (`code.1`, `artifact`, `code.2`, `pcr0`, `code.3`, `AR1`, `pcr0.1`, `code.4`, `AR2`).
2. **Common Pattern:** Most workflows follow a pattern: `Initiate` → `Forward Event` → `Initialize Build Infrastructure` → `Create Secure Commit` → `Start Build`. Some then proceed to `Save Commit` or `Start Build Process`.
3. **Attestation Generation:** Workflows for `code.2` and `code.3` include explicit steps for performing attestation (`#k`, `#vr.9`) and providing attestation data that references hashes (`h(...)`) of code and artifacts, as well as Platform Configuration Register values (`pcr0`, `pcr0.1`).
4. **Cross-Lane Dependencies:** There are clear dependencies between lanes. For example:
* The `pcr0` lane (Lane 4) receives attestation data generated in the `code.2` lane (Lane 3).
* The `pcr0.1` lane (Lane 7) triggers a build process for `AR2`.
* The `AR2` lane (Lane 9) receives a secure commit from the `code.4` lane (Lane 8) and generates a log entry.
5. **Notation:** The diagram uses a formal notation with symbols like `!` (likely indicating an output or message), `$` (variables or parameters), `h()` (hash function), and `#` (step or node identifier).
### Interpretation
This diagram models a sophisticated, secure software supply chain or trusted execution environment workflow. It demonstrates how different inputs (source code, artifacts, attestation measurements like PCRs) trigger parallel processes for building, committing, and attesting to the integrity of software components.
The key relationships are:
* **Build & Commit:** Source code or artifact inputs trigger infrastructure initialization and the creation of secure commits, which are then stored or provided as outputs.
* **Attestation:** The system generates cryptographic attestations linking the hashes of built code (`h(code)`) and artifacts (`h(artifact)`) with platform configuration state (`pcr0`). This creates verifiable proof of the build environment's integrity.
* **Chaining & Logging:** Later stages (like `AR2`) depend on outputs from earlier stages (secure commits from `code.4`), and actions are logged (`log_entry`), creating an auditable trail.
The overall purpose is to establish a verifiable chain of trust from initial inputs (code, artifacts) through the build process to final, attested outputs. The parallel lanes likely represent different components or stages of a larger system, with the attestation and logging steps serving as critical checkpoints for security and compliance. The complexity suggests this is a design for a high-assurance system where provenance and integrity are paramount.
DECODING INTELLIGENCE...
EXPERT: nemotron-free VERSION 1
RUNTIME: free/nvidia/nemotron-nano-12b-v2-vl:free
INTEL_VERIFIED
## Flowchart: Secure Commit Process Workflow
### Overview
The image contains two interconnected diagrams illustrating a secure commit process workflow in software development. The diagrams use code references (e.g., `$B1`, `$E1`, `$A1`), component labels (e.g., "StartBuild(AR1)"), and directional arrows to depict the flow of operations. The left diagram focuses on initial stages, while the right diagram expands to include attestation, log entry, and broader infrastructure interactions.
---
### Components/Axes
#### Key Components (Left Diagram):
1. **StartBuild(AR1)**
- Code references: `$B1`, `$E1`, `$A1`
- Action: `int.build_infrastructure(initBuild(artifact))`
2. **CreateSecureCommit**
- Code references: `$B4`, `$E4`, `$A4`
- Action: `int.build_infrastructure(initBuild(artifact))`
3. **ProvideAttestation(AR2)**
- Code references: `$B2`, `$E2`, `$A2`
- Action: `int.build_infrastructure(initBuild(artifact))`
4. **CreateSecureCommit (Secondary)**
- Code references: `$B3`, `$E3`, `$A3`
- Action: `int.build_infrastructure(initBuild(artifact))`
#### Key Components (Right Diagram):
1. **StartBuild(AR1)**
- Code references: `$B1`, `$E1`, `$A1`
- Action: `int.build_infrastructure(initBuild(artifact))`
2. **CreateSecureCommit**
- Code references: `$B4`, `$E4`, `$A4`
- Action: `int.build_infrastructure(initBuild(artifact))`
3. **ProvideAttestation(AR2)**
- Code references: `$B2`, `$E2`, `$A2`
- Action: `int.build_infrastructure(initBuild(artifact))`
4. **ProvideLogEntry(H1)**
- Code references: `$B5`, `$E5`, `$A5`
- Action: `int.build_infrastructure(initBuild(artifact))`
5. **CreateSecureCommit (Secondary)**
- Code references: `$B3`, `$E3`, `$A3`
- Action: `int.build_infrastructure(initBuild(artifact))`
6. **ProvideAttestation(AR3)**
- Code references: `$B6`, `$E6`, `$A6`
- Action: `int.build_infrastructure(initBuild(artifact))`
#### Arrows and Flow:
- Arrows indicate sequential or conditional execution (e.g., `→`, `→→`).
- Dashed arrows (`→→→`) suggest optional or parallel paths.
---
### Detailed Analysis
#### Left Diagram:
1. **StartBuild(AR1)** → **CreateSecureCommit** → **ProvideAttestation(AR2)**
- Initial build infrastructure setup (`$B1`, `$E1`, `$A1`).
- Secure commit process (`$B4`, `$E4`, `$A4`).
- Attestation generation (`$B2`, `$E2`, `$A2`).
2. **CreateSecureCommit (Secondary)** → **StartBuild(AR1)**
- Feedback loop for re-initialization.
#### Right Diagram:
1. **StartBuild(AR1)** → **CreateSecureCommit** → **ProvideAttestation(AR2)**
- Core workflow with attestation.
2. **CreateSecureCommit** → **ProvideLogEntry(H1)**
- Logging of commit events (`$B5`, `$E5`, `$A5`).
3. **ProvideAttestation(AR2)** → **CreateSecureCommit (Secondary)**
- Attestation validation triggers secondary commit.
4. **CreateSecureCommit (Secondary)** → **ProvideAttestation(AR3)**
- Expanded attestation for additional stages (`$B6`, `$E6`, `$A6`).
---
### Key Observations
1. **Code References**:
- `$B1`, `$E1`, `$A1` consistently appear in initial build steps.
- `$B4`, `$E4`, `$A4` dominate secure commit operations.
- `$B2`, `$E2`, `$A2` are tied to attestation.
2. **Flow Complexity**:
- The right diagram introduces branching (e.g., attestation → secondary commit).
- Dashed arrows suggest optional steps (e.g., log entry).
3. **Component Isolation**:
- Left diagram focuses on core commit and attestation.
- Right diagram adds logging and expanded attestation.
---
### Interpretation
1. **Purpose**:
- The diagrams model a secure commit workflow with emphasis on infrastructure validation (`int.build_infrastructure`), attestation, and logging.
2. **Relationships**:
- Attestation (`ProvideAttestation`) acts as a gatekeeper for subsequent commits.
- Logging (`ProvideLogEntry`) ensures auditability.
3. **Notable Patterns**:
- Repetition of `int.build_infrastructure` suggests modularity in infrastructure setup.
- Secondary commit steps imply iterative validation.
4. **Anomalies**:
- No explicit error-handling paths are depicted.
- The right diagram’s complexity may indicate scalability challenges.
---
**Note**: No numerical data or legends are present. All textual elements are transcribed directly from the diagrams.
DECODING INTELLIGENCE...