TECHNICAL ASSET FINGERPRINT
e981e40c421396e60b625e3c
Click to view fullscreen
Press ESC or click to close
FOUND IN PAPERS
EXPERT: gemini-2.0-flash VERSION 1
RUNTIME: nugit/gemini/gemini-2.0-flash
INTEL_VERIFIED
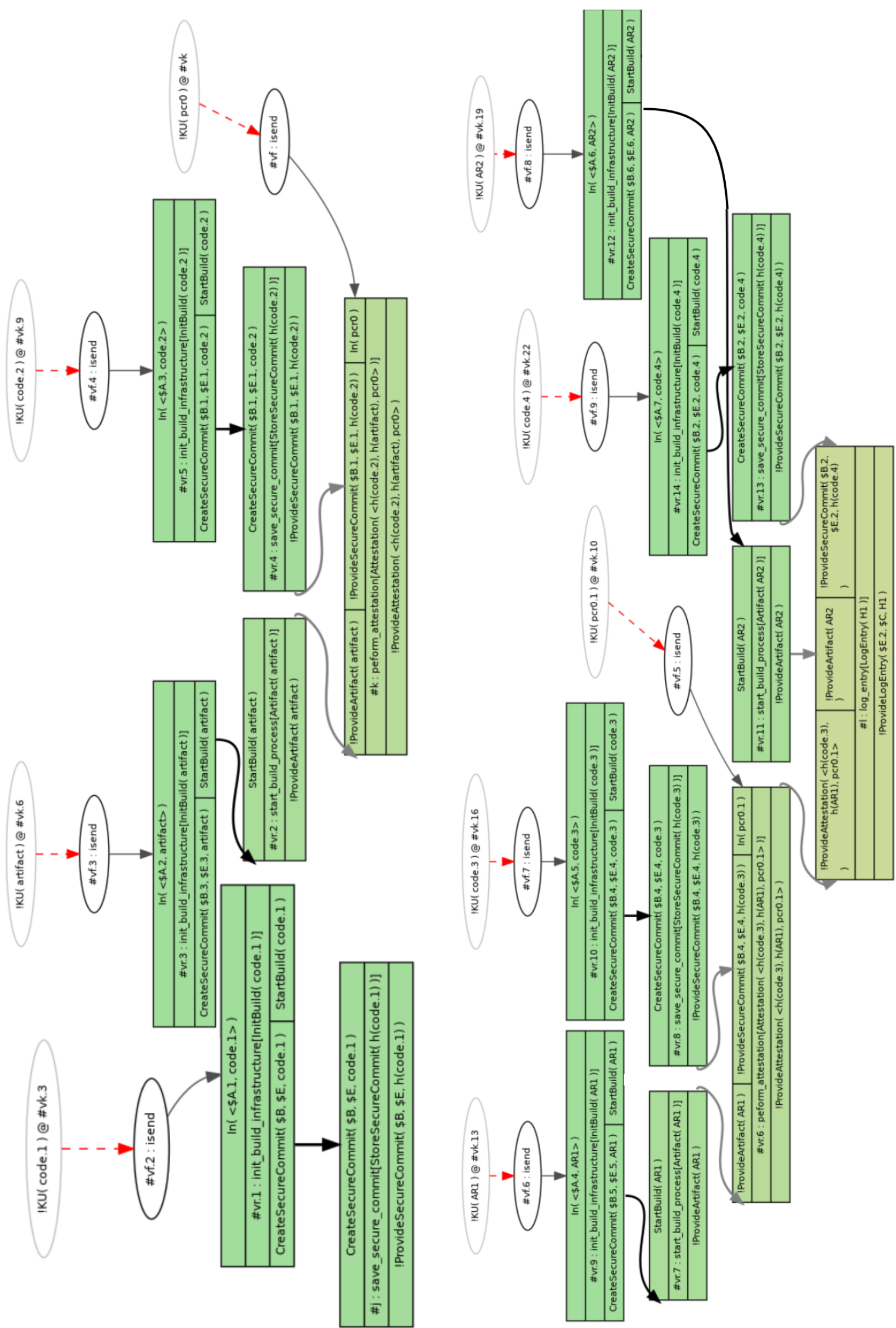
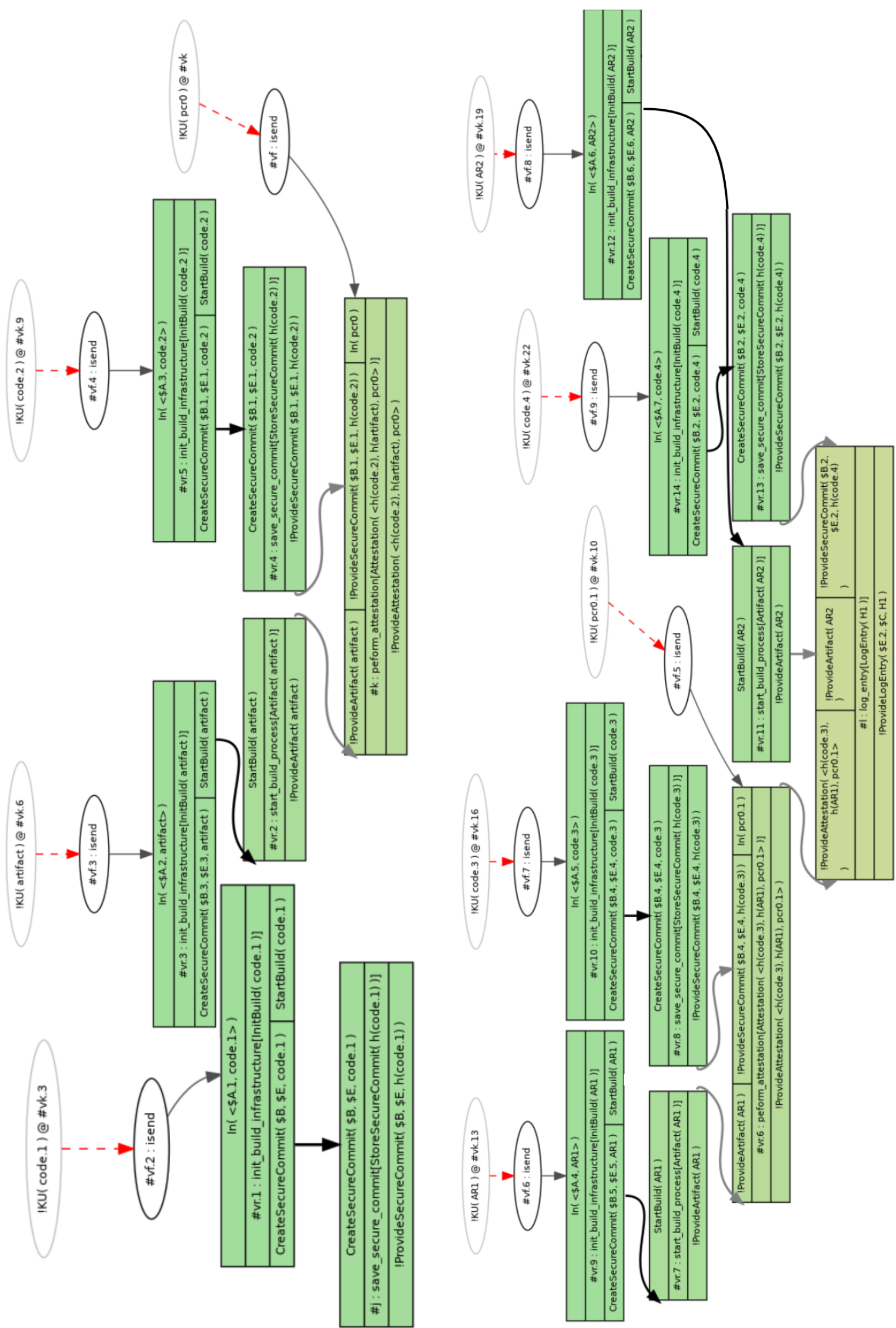
## Diagram: Build Infrastructure and Secure Commit Process
### Overview
The image presents two similar diagrams illustrating a build infrastructure and secure commit process. Each diagram depicts a series of steps involving initialization, secure commit creation, and attestation, with variations in the artifacts and parameters used. The diagrams use nodes to represent processes and edges to represent the flow of data or control.
### Components/Axes
* **Nodes:** Represented as rounded rectangles (green) or ovals (gray). Green rectangles contain process descriptions, while gray ovals denote entities like `!KU(code.x) @ #vk.y` or `!KU(ARx) @ #vk.y` or `!KU(pcr0.x) @ #vk.y`.
* **Edges:** Represented as arrows, indicating the flow of data or control. Black arrows indicate a standard flow, while dashed red arrows indicate a specific type of interaction (likely an "isend" operation). Gray arrows indicate attestation or artifact provision.
* **Labels:** Each node has a label indicating its function or state, such as `#vr.1: init_build_infrastructure[InitBuild(code.1)]` or `#vr.4: save_secure_commit[StoreSecureCommit(h(code.2))]`.
* **Entities:** `!KU(code.x) @ #vk.y`, `!KU(ARx) @ #vk.y`, `!KU(pcr0.x) @ #vk.y` represent entities with attributes like code version, artifact version, or PCR (Platform Configuration Register) values.
* **Operations:** `#vf.x: isend` represents an "isend" operation, likely indicating a message send.
### Detailed Analysis or ### Content Details
**Left Diagram:**
1. **Top-Left Node:** `!KU(code.1) @ #vk.3`
2. **Second Node:** `#vf.2: isend`
3. **Third Node (Green Rectangle):**
* `In(<$A.1, code.1>)`
* `#vr.1: init_build_infrastructure[InitBuild(code.1)]`
* `CreateSecureCommit($B, $E, code.1)`
* `StartBuild(code.1)`
4. **Fourth Node (Green Rectangle):**
* `#j: save_secure_commit[StoreSecureCommit(h(code.1))]`
* `!Provide SecureCommit($B, $E, h(code.1))`
5. **Fifth Node (Top):** `!KU(code.2) @ #vk.9`
6. **Sixth Node:** `#vf.4: isend`
7. **Seventh Node (Green Rectangle):**
* `In(<$A.3, code.2>)`
* `#vr.5: init_build_infrastructure[InitBuild(code.2)]`
* `CreateSecureCommit($B.1, $E.1, code.2)`
* `StartBuild(code.2)`
8. **Eighth Node (Green Rectangle):**
* `#vr.4: save_secure_commit[StoreSecureCommit(h(code.2))]`
* `!Provide SecureCommit($B.1, $E.1, h(code.2))`
9. **Ninth Node (Top):** `!KU(pcr0) @ #vk`
10. **Tenth Node (Green Rectangle):**
* `!Provide SecureCommit($B.1, $E.1, h(code.2)) In(pcr0)`
* `#k: peform_attestation [Attestation(<h(code.2), h(artifact), pcr0>)]`
* `!Provide Attestation( <h(code.2), h(artifact), pcr0>)`
11. **Eleventh Node (Top):** `!KU(artifact) @ #vk.6`
12. **Twelfth Node:** `#vf.3: isend`
13. **Thirteenth Node (Green Rectangle):**
* `In(<$A.2, artifact>)`
* `#vr.3: init_build_infrastructure[InitBuild(artifact)]`
* `CreateSecureCommit($B.3, $E.3, artifact) StartBuild(artifact)`
14. **Fourteenth Node (Green Rectangle):**
* `#vr.2: start_build_process[Artifact(artifact)]`
* `!Provide Artifact(artifact)`
15. **Fifteenth Node (Green Rectangle):**
* `!ProvideArtifact( artifact )`
**Right Diagram:**
1. **Top-Left Node:** `!KU(AR1) @ #vk.13`
2. **Second Node:** `#vf.6: isend`
3. **Third Node (Green Rectangle):**
* `In(<$A.4, AR1>)`
* `#vr.9: init_build_infrastructure [InitBuild(AR1)]`
* `CreateSecureCommit($B.5, $E.5, AR1)`
* `StartBuild(AR1)`
4. **Fourth Node (Green Rectangle):**
* `#vr.7: start_build_process[Artifact(AR1)]`
* `!Provide Artifact (AR1)`
5. **Fifth Node (Top):** `!KU(code.3) @ #vk.16`
6. **Sixth Node:** `#vf.7: isend`
7. **Seventh Node (Green Rectangle):**
* `In(<$A.5, code.3>)`
* `#vr.10: init_build_infrastructure[InitBuild(code.3)]`
* `CreateSecureCommit($B.4, $E.4, code.3)`
* `StartBuild(code.3)`
8. **Eighth Node (Green Rectangle):**
* `#vr.8: save_secure_commit[StoreSecureCommit(h(code.3))]`
* `!Provide SecureCommit($B.4. $E.4, h(code.3))`
9. **Ninth Node (Top):** `!KU(code.4) @ #vk.22`
10. **Tenth Node:** `#vf.9: isend`
11. **Eleventh Node (Green Rectangle):**
* `In(<$A.7, code.4>)`
* `#vr.14: init_build_infrastructure[InitBuild(code.4)]`
* `CreateSecureCommit($B.2. $E.2, code.4)`
* `StartBuild(code.4)`
12. **Twelfth Node (Green Rectangle):**
* `#vr.13: save_secure_commit[StoreSecureCommit(h(code.4))]`
* `!Provide SecureCommit($B.2, $E.2, h(code.4))`
13. **Thirteenth Node (Top):** `!KU(pcr0.1) @ #vk.10`
14. **Fourteenth Node:** `#vf.5: isend`
15. **Fifteenth Node (Top):** `!KU(AR2) @ #vk.19`
16. **Sixteenth Node:** `#vf.8: isend`
17. **Seventeenth Node (Green Rectangle):**
* `In(<$A.6, AR2>)`
* `#vr.12: init_build_infrastructure[InitBuild(AR2)]`
* `CreateSecureCommit($B.6. $E.6, AR2) StartBuild(AR2)`
18. **Eighteenth Node (Green Rectangle):**
* `#vr.11: start_build_process [Artifact( AR2)]`
* `!Provide Artifact(AR2)`
19. **Nineteenth Node (Green Rectangle):**
* `!ProvideArtifact( AR2 )`
20. **Twentieth Node (Green Rectangle):**
* `!Provide SecureCommit($B.4, $E.4, h(code.3))`
* `#vr.6: peform_attestation[Attestation(<h(code.3), h(AR1), pcr0.1>)]`
* `!Provide Attestation(<h(code.3), h(AR1), pcr0.1>)`
21. **Twenty-First Node (Green Rectangle):**
* `#1: log_entry[LogEntry(H1)]`
* `!Provide LogEntry($E.2, $C, H1)`
### Key Observations
* Both diagrams follow a similar pattern: initialization, secure commit, and attestation.
* The left diagram uses `code.1`, `code.2`, and `artifact` as parameters, while the right diagram uses `AR1`, `code.3`, `code.4`, and `AR2`.
* The `isend` operations (`#vf.x: isend`) appear to trigger the initialization processes.
* The attestation process involves PCR values and hash values of artifacts.
### Interpretation
The diagrams illustrate a process for securely building and committing code and artifacts. The process involves initializing a build infrastructure, creating secure commits, and performing attestation to ensure the integrity of the build process. The variations in parameters (code versions, artifact versions, PCR values) suggest that the process can be adapted to different types of builds and artifacts. The use of "isend" operations suggests a distributed or asynchronous build process. The attestation step is crucial for verifying the integrity of the build and ensuring that the resulting artifacts are trustworthy. The log entry at the end of the right diagram suggests that the entire process is auditable.
DECODING INTELLIGENCE...