## Diagram: Secure Application Workflow
### Overview
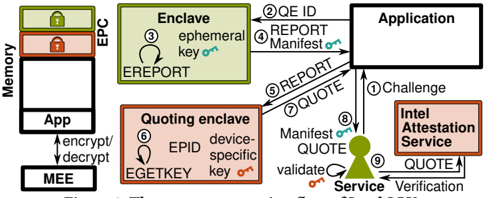
The image illustrates a secure application workflow, detailing the interactions between different components such as the Application, Enclave, Quoting Enclave, Intel Attestation Service, and a Service. The diagram highlights the flow of information and cryptographic operations involved in attestation and verification.
### Components/Axes
* **Memory:** Contains "App" and "EPC" (Enclave Page Cache). The memory region has two locked icons, one green and one red, at the top.
* **App:** Represents the application running in memory.
* **MEE:** (Bottom-left) Interacts with the App for encryption/decryption.
* **EPC:** Enclave Page Cache, a protected memory region.
* **Enclave:** (Top-right) A secure execution environment.
* Contains "ephemeral key".
* **Quoting Enclave:** (Bottom-left) Generates quotes for attestation.
* Contains "EPID device-specific key".
* **Intel Attestation Service:** (Right) Provides attestation services.
* **Service:** (Bottom-right) Verifies the attestation quote.
* **Numbered Arrows:** Indicate the sequence of operations.
### Detailed Analysis
The diagram depicts the following steps:
1. **Challenge:** The Intel Attestation Service sends a challenge to the Application.
2. **QE ID:** The Application sends the Quoting Enclave ID to the Enclave.
3. **EREPORT:** The Enclave generates a report using an ephemeral key.
4. **REPORT Manifest:** The Enclave sends a report and manifest to the Application.
5. **REPORT QUOTE:** The Application sends a report and quote to the Quoting Enclave.
6. **EGETKEY:** The Quoting Enclave uses EGETKEY to obtain a device-specific key.
7. **QUOTE:** The Quoting Enclave sends a quote to the Application.
8. **Manifest QUOTE:** The Application sends a manifest and quote to the Service.
9. **QUOTE:** The Intel Attestation Service sends a quote to the Service for verification.
* The Service validates the quote.
### Key Observations
* The diagram emphasizes the use of cryptographic keys and reports for secure attestation.
* The flow involves multiple components, each with specific roles in the attestation process.
* The Enclave and Quoting Enclave are central to generating and signing the attestation quote.
* The Intel Attestation Service and Service are responsible for verifying the quote and ensuring the integrity of the application.
### Interpretation
The diagram illustrates a secure application workflow that leverages Intel's SGX (Software Guard Extensions) technology for attestation and verification. The process involves generating a quote within a secure enclave, which is then verified by a trusted service. This ensures that the application is running in a trusted environment and has not been tampered with. The use of ephemeral keys and device-specific keys adds an extra layer of security to the attestation process. The workflow is designed to protect sensitive data and code from unauthorized access and modification.