\n
## Diagram: Intel Attestation Service Flow
### Overview
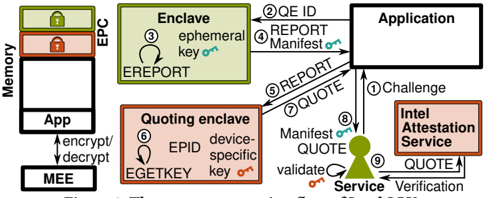
This diagram illustrates the flow of data and interactions between different components involved in Intel's attestation service. The process involves an Application, an Enclave (within an EPC - Enhanced Privacy Component), a Quoting Enclave, and the Intel Attestation Service. The diagram highlights the exchange of reports, quotes, and validation steps to verify the integrity of the Enclave.
### Components/Axes
The diagram features the following components:
* **Memory:** Represented on the left side, showing the App and Enclave residing within it.
* **Application:** A rectangular block on the top-right, interacting with both the Enclave and the Intel Attestation Service.
* **Enclave:** A light green rectangular block labeled "Enclave" and "EPC".
* **Quoting Enclave:** An orange rectangular block labeled "Quoting enclave".
* **Intel Attestation Service:** A red rectangular block on the bottom-right.
* **Service:** A green triangular shape labeled "Service" positioned between the Quoting Enclave and the Intel Attestation Service.
* **MEE:** (Management Engine Interface) - Located at the bottom left, connected to the App.
The diagram also includes numbered arrows indicating the flow of information:
1. Challenge
2. QE ID REPORT
3. ephemeral key
4. REPORT Manifest
5. REPORT
6. EPID device-specific key
7. QUOTE
8. Manifest QUOTE
9. QUOTE
Additionally, text labels are embedded within the components:
* "ephemeral key on" (within the Enclave)
* "device-specific key on" (within the Quoting Enclave)
* "validate on" (below the Service)
* "encrypt/decrypt" (connecting MEE to App)
### Detailed Analysis / Content Details
The diagram depicts a sequence of operations:
1. The **Application** initiates a **Challenge** to the **Intel Attestation Service**.
2. The **Application** requests a **QE ID REPORT** from the **Enclave**.
3. The **Enclave** generates an **ephemeral key**.
4. The **Application** requests a **REPORT Manifest** from the **Enclave**.
5. The **Enclave** sends a **REPORT** to the **Application**.
6. The **Quoting Enclave** generates an **EPID device-specific key**.
7. The **Application** sends a **QUOTE** to the **Intel Attestation Service**.
8. The **Quoting Enclave** sends a **Manifest QUOTE** to the **Service**.
9. The **Service** **validates** the quote and sends a **QUOTE** to the **Intel Attestation Service** for **Verification**.
The diagram shows the App interacting with the Enclave via the MEE, using "encrypt/decrypt" operations. The Enclave resides within the EPC in Memory.
### Key Observations
The diagram emphasizes the secure communication flow between the Application and the Intel Attestation Service, mediated by the Enclave and Quoting Enclave. The use of keys (ephemeral and device-specific) and reports/quotes suggests a cryptographic attestation process. The validation step performed by the Service is crucial for ensuring the integrity of the Enclave.
### Interpretation
This diagram illustrates a remote attestation process, where the Application verifies the integrity of the Enclave running on a remote platform. The Intel Attestation Service acts as a trusted third party, providing a mechanism for verifying the Enclave's identity and configuration. The process involves generating cryptographic evidence (reports and quotes) and validating them against a trusted authority. The use of EPC and Enclaves suggests a focus on secure execution environments, protecting sensitive data and code from unauthorized access. The flow highlights the importance of secure key management and cryptographic verification in establishing trust in remote computing environments. The diagram suggests a layered security approach, with multiple components working together to ensure the integrity of the system.