## Diagram: Intel SGX Remote Attestation Flow
### Overview
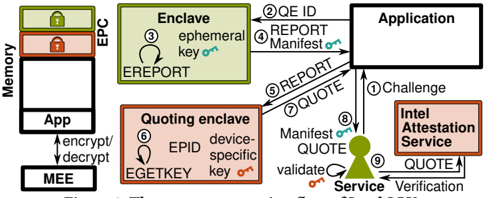
This is a technical flow diagram illustrating the process of remote attestation for an Intel Software Guard Extensions (SGX) enclave. It depicts the interaction between an application, its secure enclave, a quoting enclave, and an external attestation service to verify the integrity and authenticity of the code running within the enclave.
### Components/Axes
The diagram is organized into several key components, connected by numbered, directional arrows indicating the flow of operations.
**Left Column - Memory & Execution Environment:**
* **Memory:** A vertical block representing system memory.
* **EPC (Enclave Page Cache):** A highlighted section within Memory, containing a locked padlock icon.
* **App:** A block within the EPC, representing the untrusted application code.
* **MEE (Memory Encryption Engine):** A block below the EPC, connected to the "App" block with bidirectional arrows labeled **"encrypt/decrypt"**.
**Center - Secure Enclaves:**
* **Enclave (Top):** A green-bordered box.
* Contains text: **"ephemeral key"** with a key icon.
* Contains a circular arrow labeled **"EREPORT"**.
* Contains the step number **"③"**.
* **Quoting enclave (Bottom):** A brown-bordered box.
* Contains text: **"EPID device-specific key"** with a key icon.
* Contains text: **"EGETKEY"**.
* Contains the step number **"⑥"**.
**Right Column - External Entities:**
* **Application:** A large white box at the top right.
* **Intel Attestation Service:** A brown-bordered box at the bottom right.
* **Service:** Represented by a person/user icon, positioned between the Application and the Intel Attestation Service.
**Flow Arrows & Labels (Numbered Steps):**
The process is defined by a sequence of nine numbered steps, each with a specific label:
1. **① Challenge** (From Service to Application)
2. **② QE ID, REPORT, Manifest** (From Application to Enclave)
3. **③** (Within the Enclave, generating a report)
4. **④ REPORT** (From Enclave to Quoting Enclave)
5. **⑤ QUOTE** (From Quoting Enclave to Application)
6. **⑥** (Within the Quoting Enclave, using EGETKEY)
7. **⑦ Manifest, QUOTE** (From Application to Service)
8. **⑧ validate** (From Service to Intel Attestation Service)
9. **⑨ QUOTE, Verification** (Between Service and Intel Attestation Service)
### Detailed Analysis
The diagram details a 9-step cryptographic protocol:
1. **Initiation:** A remote **Service** (verifier) sends a **Challenge** (①) to the local **Application**.
2. **Report Generation:** The Application forwards this request to its **Enclave**, providing a **Quoting Enclave ID (QE ID)**, a **Manifest** (description of enclave code), and the challenge (②). The Enclave generates a cryptographic **REPORT** about its state, signed with its **ephemeral key** (③).
3. **Quote Creation:** The Enclave sends this **REPORT** (④) to the dedicated **Quoting Enclave**. The Quoting Enclave uses its unique, hardware-backed **EPID device-specific key** (accessed via **EGETKEY** (⑥)) to transform the report into a **QUOTE** (⑤). This quote is a signature that can be verified by Intel.
4. **Verification Request:** The Application sends the **Manifest** and the newly created **QUOTE** (⑦) back to the remote **Service**.
5. **Attestation:** The Service **validates** (⑧) the quote by communicating with the **Intel Attestation Service**. This involves submitting the **QUOTE** for **Verification** (⑨) to confirm it was generated by a genuine Intel SGX enclave with the expected configuration (as described in the Manifest).
### Key Observations
* **Component Isolation:** The diagram clearly separates the untrusted world (Application, Service) from the trusted execution environment (Enclave, Quoting Enclave, EPC, MEE).
* **Key Hierarchy:** Two distinct keys are highlighted: a temporary **ephemeral key** within the target enclave and a permanent, hardware-rooted **EPID device-specific key** within the Quoting Enclave.
* **Data Flow:** The flow is not linear but involves a round-trip: Service -> App -> Enclave -> Quoting Enclave -> App -> Service -> Intel.
* **Central Role of the Manifest:** The **Manifest** is passed in steps ② and ⑦, indicating it is a critical piece of evidence describing the enclave's identity and code, which is ultimately verified against the quote.
### Interpretation
This diagram explains the **chain of trust** in SGX remote attestation. The core problem it solves is: "How can a remote service trust that a specific, secure enclave is running on a genuine Intel platform with untampered code?"
The process demonstrates a **Peircean investigative** approach:
* **Sign (①-⑤):** The initial challenge and report generation create a *sign*—a cryptographic measurement of the enclave's state.
* **Object (⑥):** The Quoting Enclave's hardware key is the *object* that gives the sign its authority. The quote is an indexical sign pointing directly to that specific hardware.
* **Interpretant (⑦-⑨):** The remote Service, by validating the quote with Intel, forms an *interpretant*—a reasoned belief that the enclave is trustworthy.
The notable **anomaly** or complexity is the necessity of the separate **Quoting Enclave**. This is a security design choice: the target enclave (running user code) is not trusted to sign its own report. Instead, it must request a signature from a higher-privilege, Intel-signed quoting enclave, preventing a compromised application enclave from forging attestations. The entire flow ensures that the **Verification** (⑨) by Intel is based on a hardware-anchored signature, not software that could be manipulated.