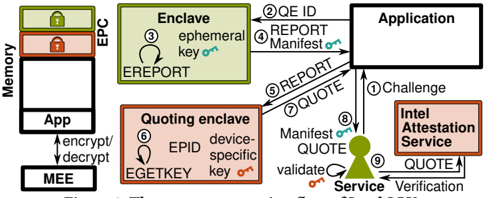
## Flowchart: Secure Enclave Attestation Process
### Overview
The diagram illustrates a secure enclave attestation workflow involving multiple components: Memory (EPC/App), Enclave, Quoting Enclave, Application, Intel Attestation Service, and Service. Arrows depict data flow and cryptographic operations, emphasizing encryption, validation, and attestation processes.
### Components/Axes
1. **Memory**: Contains EPC (Enclave Page Cache) and Application memory, with EPC marked as "locked" (green) and Application memory as "locked" (orange).
2. **Enclave**: Labeled "Enclave" with a circular arrow indicating "EREPORT" (Ephemeral Key Reporting).
3. **Quoting Enclave**: Contains "EGETKEY" (device-specific key) and "EID" (Enclave Identity).
4. **Application**: A generic box labeled "Application."
5. **Intel Attestation Service**: A box labeled "Intel Attestation Service" with bidirectional arrows for "QUOTE" and "Verification."
6. **Service**: A green icon labeled "Service" with "validate" and "QUOTE" arrows.
### Detailed Analysis
- **Flow Sequence**:
1. **Challenge**: Application initiates a "Challenge" to the Intel Attestation Service.
2. **Quote**: Service responds with a "QUOTE," which the Application validates.
3. **Report Manifest**: Application sends a "REPORT Manifest" to the Enclave.
4. **Enclave Operations**: Enclave enclaves an "ephemeral key" (EPC) and generates an "EREPORT."
5. **Quoting Enclave**: Uses "EGETKEY" (device-specific key) to generate a "QUOTE," validated by the Service.
6. **Encryption/Decryption**: MEE (Memory Encryption Engine) handles encryption/decryption between Memory and Application.
- **Cryptographic Elements**:
- **EPC**: Green box with "locked" status, indicating secure enclave memory.
- **EGETKEY**: Orange box with device-specific key for quoting.
- **EID**: Enclave Identity tied to the Quoting Enclave.
- **Manifest**: Transmitted between Application and Enclave for attestation.
### Key Observations
- **Security Layers**: Multiple encryption/decryption steps (MEE) and attestation (Intel Attestation Service) ensure data integrity.
- **Ephemeral Keys**: Temporary keys (EPC, EGETKEY) are used for short-lived security operations.
- **Validation Loop**: The Service validates "QUOTE" and "Manifest," creating a feedback loop for trust.
### Interpretation
This diagram represents a hardware-based secure enclave architecture, likely leveraging Intel SGX technology. The workflow ensures that sensitive data (e.g., ephemeral keys) is protected within isolated memory regions (EPC) and validated through cryptographic attestation. The Intel Attestation Service acts as a central authority for verifying the integrity of enclave operations, while the Quoting Enclave generates device-specific proofs. The use of "locked" memory regions and MEE encryption highlights a focus on confidentiality and tamper resistance. The bidirectional "QUOTE" flow suggests mutual authentication between the Application and Service, reinforcing trust in the system.