## Diagram: Data Privacy Vault Data Flow and Redaction
### Overview
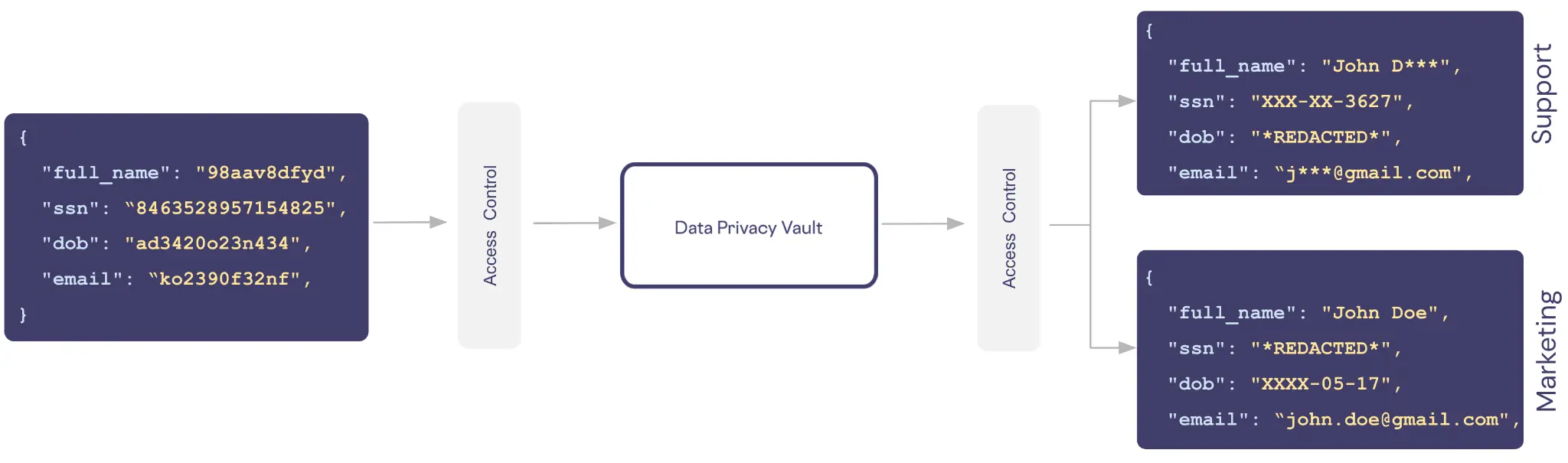
This diagram illustrates a data privacy architecture where sensitive user data is ingested, processed through a central "Data Privacy Vault," and then released in different, redacted forms to different internal consumers (Support and Marketing). The flow demonstrates how raw, tokenized data is transformed into role-based, partially masked outputs.
### Components/Axes
The diagram is a horizontal flowchart with the following components, arranged from left to right:
1. **Input Data Object (Left):** A dark blue rounded rectangle containing a JSON object with tokenized/masked sensitive data.
2. **First Access Control Block:** A light gray vertical rectangle labeled "Access Control" with an arrow pointing from the input data to it.
3. **Central Processing Unit:** A white rounded rectangle with a dark blue border labeled "Data Privacy Vault". An arrow points from the first Access Control block to this vault.
4. **Second Access Control Block:** Another light gray vertical rectangle labeled "Access Control". An arrow points from the Data Privacy Vault to this block.
5. **Output Data Objects (Right):** Two dark blue rounded rectangles, each containing a JSON object with differently redacted data. They are labeled vertically on their right side:
* **Top Output:** Labeled "Support".
* **Bottom Output:** Labeled "Marketing".
Arrows point from the second Access Control block to each of these output objects.
### Detailed Analysis
**1. Input Data (Left Block):**
The initial data payload is a JSON object with four key-value pairs. The values appear to be tokenized or hashed placeholders, not real data.
```json
{
"full_name": "98aav8dfyd",
"ssn": "8463528957154825",
"dob": "ad3420o23n434",
"email": "ko2390f32nf"
}
```
**2. Data Flow & Transformation:**
* The tokenized input data passes through an **Access Control** layer.
* It enters the **Data Privacy Vault**, which is the core processing engine. This vault likely contains the logic and secure storage to map tokens to real data and apply redaction policies.
* The processed data exits through a second **Access Control** layer, which routes it based on the consumer's role.
**3. Output for "Support" (Top-Right Block):**
The Support team receives a JSON object where data is partially redacted to show just enough for verification while protecting full identifiers.
```json
{
"full_name": "John D***",
"ssn": "XXX-XX-3627",
"dob": "*REDACTED*",
"email": "j***@gmail.com"
}
```
* **Trend/Pattern:** The `full_name` shows the first name and last initial. The `ssn` reveals only the last four digits. The `dob` is completely redacted. The `email` shows the first initial and the domain.
**4. Output for "Marketing" (Bottom-Right Block):**
The Marketing team receives a different JSON object with a distinct redaction strategy, prioritizing different data elements.
```json
{
"full_name": "John Doe",
"ssn": "*REDACTED*",
"dob": "XXXX-05-17",
"email": "john.doe@gmail.com"
}
```
* **Trend/Pattern:** The `full_name` is fully visible. The `ssn` is completely redacted. The `dob` shows only the month and day (with the year redacted as "XXXX"). The `email` is fully visible.
### Key Observations
1. **Role-Based Data Masking:** The system provides different "views" of the same underlying data based on the consumer's role (Support vs. Marketing).
2. **Redaction Strategy Variance:**
* **Support View:** Focuses on partial identifiers for customer service verification (last 4 of SSN, name initial). Completely hides the date of birth.
* **Marketing View:** Provides full name and email for communication but heavily redacts government ID (SSN) and partially redacts the date of birth (hiding the year).
3. **Data Tokenization:** The input data is not in a human-readable format, suggesting it is already tokenized or encrypted before entering this privacy workflow.
4. **Centralized Policy Enforcement:** The "Data Privacy Vault" acts as a single point of control for applying complex, context-aware data masking rules, rather than having each downstream system implement its own logic.
### Interpretation
This diagram depicts a **Privacy-by-Design** architecture, specifically a **Data Privacy Vault** pattern. Its purpose is to decouple sensitive data from applications and provide controlled, auditable access.
* **What it demonstrates:** It shows how an organization can safely utilize sensitive user data (like PII) for multiple business functions (Support, Marketing) without exposing the raw data to any internal team. The vault acts as a secure broker.
* **How elements relate:** The two "Access Control" blocks represent policy enforcement points. The first likely handles authentication and authorization for data ingestion, while the second handles authorization for data egress based on the requesting service's role. The Vault is the trusted processing core.
* **Notable Anomalies/Patterns:** The most significant pattern is the deliberate difference in redaction between the two outputs. This is not an error but a feature, illustrating **data minimization**—each service receives only the data fields and granularity necessary for its specific function, reducing internal risk and aiding compliance with regulations like GDPR or CCPA.
* **Underlying Principle:** The architecture shifts the burden of data protection from individual application teams to a centralized, specialized platform, enabling consistent security and privacy policy enforcement across the organization.