\n
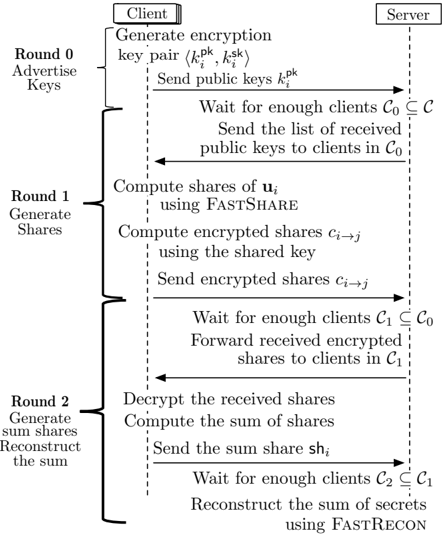
## Protocol Diagram: Three-Round Secure Summation Protocol
### Overview
The image is a technical diagram illustrating a three-round cryptographic protocol for securely computing the sum of secrets held by multiple clients, facilitated by a server. The protocol uses public-key encryption, secret sharing (via FASTSHARE), and a reconstruction mechanism (FASTRECON). The diagram is structured as a sequence chart with three vertical timelines: a left column labeling the rounds, a central "Client" column, and a right "Server" column. Arrows indicate message flow between Client and Server.
### Components/Axes
* **Vertical Timelines:**
* **Left Column:** Labels the three protocol rounds: "Round 0 Advertise Keys", "Round 1 Generate Shares", and "Round 2 Generate sum shares Reconstruct the sum".
* **Center Column:** Labeled "Client" at the top. Represents the actions performed by a participating client (denoted with subscript *i*).
* **Right Column:** Labeled "Server" at the top. Represents the actions performed by the central server.
* **Message Flow:** Horizontal arrows indicate messages sent between Client and Server. Solid arrows point from Client to Server; dashed arrows point from Server to Client.
* **Mathematical Notation:**
* \( k_i^{pk} \), \( k_i^{sk} \): Public and secret key pair for client *i*.
* \( \mathbf{u}_i \): The secret value held by client *i*.
* \( c_{i \rightarrow j} \): Encrypted share of client *i*'s secret intended for client *j*.
* \( sh_i \): The sum share computed by client *i*.
* \( \mathcal{C} \): The set of all clients.
* \( \mathcal{C}_0 \subseteq \mathcal{C} \), \( \mathcal{C}_1 \subseteq \mathcal{C}_0 \), \( \mathcal{C}_2 \subseteq \mathcal{C}_1 \): Subsets of clients participating in successive rounds, indicating a filtering or threshold process.
### Detailed Analysis
The protocol proceeds in three sequential rounds:
**Round 0: Advertise Keys**
1. **Client Action:** "Generate encryption key pair \( (k_i^{pk}, k_i^{sk}) \)".
2. **Client -> Server Message:** "Send public keys \( k_i^{pk} \)".
3. **Server Action:** "Wait for enough clients \( \mathcal{C}_0 \subseteq \mathcal{C} \)".
4. **Server -> Client Message:** "Send the list of received public keys to clients in \( \mathcal{C}_0 \)".
**Round 1: Generate Shares**
1. **Client Action:** "Compute shares of \( \mathbf{u}_i \) using FASTSHARE".
2. **Client Action:** "Compute encrypted shares \( c_{i \rightarrow j} \) using the shared key". (The "shared key" likely refers to pairwise keys established using the public keys from Round 0).
3. **Client -> Server Message:** "Send encrypted shares \( c_{i \rightarrow j} \)".
4. **Server Action:** "Wait for enough clients \( \mathcal{C}_1 \subseteq \mathcal{C}_0 \)".
5. **Server -> Client Message:** "Forward received encrypted shares to clients in \( \mathcal{C}_1 \)".
**Round 2: Generate sum shares / Reconstruct the sum**
1. **Client Action:** "Decrypt the received shares".
2. **Client Action:** "Compute the sum of shares".
3. **Client -> Server Message:** "Send the sum share \( sh_i \)".
4. **Server Action:** "Wait for enough clients \( \mathcal{C}_2 \subseteq \mathcal{C}_1 \)".
5. **Server Action:** "Reconstruct the sum of secrets using FASTRECON".
### Key Observations
* **Progressive Client Subsetting:** The protocol uses nested subsets of clients (\( \mathcal{C} \supseteq \mathcal{C}_0 \supseteq \mathcal{C}_1 \supseteq \mathcal{C}_2 \)). This suggests a robustness or security mechanism where the protocol only proceeds if a sufficient number of clients remain active at each stage.
* **Hybrid Cryptographic Approach:** It combines asymmetric encryption (public/private keys for secure channel setup) with secret sharing (FASTSHARE for distributing the secret) and a specialized reconstruction algorithm (FASTRECON).
* **Server's Role:** The server acts primarily as a communication relay and coordinator. It does not learn the individual secrets \( \mathbf{u}_i \) or the intermediate shares \( c_{i \rightarrow j} \), as these are encrypted. Its final role is to aggregate the public "sum shares" (\( sh_i \)) to compute the global sum.
* **Client's Role:** Clients perform the core cryptographic operations: key generation, secret sharing, encryption/decryption, and local summation of shares.
### Interpretation
This diagram outlines a **privacy-preserving distributed summation protocol**. Its purpose is to allow a group of clients to collectively compute the sum of their private values (\( \sum \mathbf{u}_i \)) without revealing any individual \( \mathbf{u}_i \) to the server or to other clients.
* **How it works:** Each client splits their secret into shares (Round 1). These shares are encrypted and distributed. After receiving and decrypting shares from others, each client computes a local sum of shares and sends a single "sum share" to the server (Round 2). The server, receiving these sum shares from enough clients, can reconstruct the final total sum using FASTRECON, but cannot determine any individual's contribution.
* **Security & Robustness:** The use of public keys establishes secure channels. The secret sharing scheme (FASTSHARE) ensures that no single party learns the secret from the shares they receive. The nested client subsets (\( \mathcal{C}_0, \mathcal{C}_1, \mathcal{C}_2 \)) provide fault tolerance, allowing the protocol to complete even if some clients drop out, as long as a minimum threshold remains.
* **Notable Design:** The protocol is efficient for the server, which only handles encrypted data and final sum shares, offloading the more computationally intensive cryptographic operations (sharing, encryption, decryption) to the clients. The names "FASTSHARE" and "FASTRECON" imply these are optimized algorithms for the sharing and reconstruction phases, respectively.