\n
## Diagram: Secure Multi-Party Computation Protocol Flow
### Overview
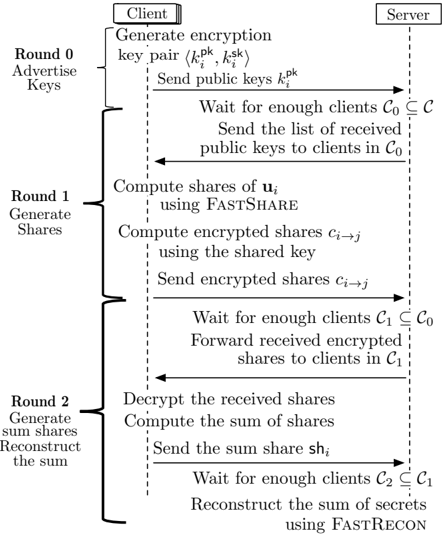
The image depicts a flowchart illustrating a secure multi-party computation protocol involving a client and a server, executed over three rounds. The protocol appears to focus on key exchange, share generation, and sum reconstruction, likely for a privacy-preserving computation. The diagram uses arrows to indicate the flow of information between the client and server.
### Components/Axes
The diagram is structured into three main sections, labeled "Round 0: Advertise Keys", "Round 1: Generate Shares", and "Round 2: Generate sum/shares Reconstruct the sum". These sections are vertically aligned and separated by horizontal lines. The diagram features two primary actors: "Client" (positioned at the top-left) and "Server" (positioned at the top-right). The flow of communication is indicated by dashed arrows. Mathematical notations and algorithm names (FASTSHARE, FASTRECON) are embedded within the process steps. The diagram also includes set notation (C₀, C₁, C₂) to represent client subsets.
### Detailed Analysis or Content Details
**Round 0: Advertise Keys**
1. **Client:** "Generate encryption key pair (kₚᵏ, kₛᵏ)"
2. **Client → Server:** "Send public keys kₚᵏ" (dashed arrow)
3. **Server:** "Wait for enough clients C₀ ⊆ C"
4. **Server → Clients in C₀:** "Send the list of received public keys to clients in C₀" (dashed arrow)
**Round 1: Generate Shares**
1. **Client:** "Compute shares of uᵢ using FASTSHARE"
2. **Client:** "Compute encrypted shares cᵢ→ⱼ using the shared key"
3. **Client → Server:** "Send encrypted shares cᵢ→ⱼ" (dashed arrow)
4. **Server:** "Wait for enough clients C₁ ⊆ C₀"
5. **Server → Clients in C₁:** "Forward received encrypted shares to clients in C₁" (dashed arrow)
**Round 2: Generate sum/shares Reconstruct the sum**
1. **Client:** "Decrypt the received shares"
2. **Client:** "Compute the sum of shares"
3. **Client → Server:** "Send the sum share shᵢ" (dashed arrow)
4. **Server:** "Wait for enough clients C₂ ⊆ C₁"
5. **Server:** "Reconstruct the sum of secrets using FASTRECON"
**Notations:**
* kₚᵏ: Public key
* kₛᵏ: Secret key
* uᵢ: Shares of a value
* cᵢ→ⱼ: Encrypted shares
* shᵢ: Sum share
* C₀, C₁, C₂: Subsets of clients, with C₂ ⊆ C₁ ⊆ C₀ ⊆ C
### Key Observations
The protocol is iterative, progressing through three rounds. Each round involves waiting for a sufficient number of clients to participate, indicated by the set notation (C₀, C₁, C₂). The use of FASTSHARE and FASTRECON suggests optimized algorithms for share generation and reconstruction. The encryption and decryption steps highlight the privacy-preserving nature of the protocol. The server acts as a facilitator, forwarding shares between clients.
### Interpretation
This diagram illustrates a secure multi-party computation (MPC) protocol. The goal is to allow multiple clients to jointly compute a function (likely a sum in this case) on their private inputs without revealing those inputs to each other or the server.
* **Round 0 (Key Exchange):** Establishes a secure communication channel between clients and the server through public key exchange.
* **Round 1 (Share Generation):** Clients generate shares of their inputs using FASTSHARE and encrypt them using shared keys. This distributes the input data among the clients, preventing any single client from knowing the complete input.
* **Round 2 (Sum Reconstruction):** Clients decrypt the received shares, compute the sum of shares, and send sum shares to the server. The server then reconstructs the final sum using FASTRECON.
The use of subsets (C₀, C₁, C₂) suggests a threshold scheme, where a minimum number of clients must participate in each round to ensure the protocol's security and correctness. The server's role is limited to forwarding messages, minimizing its potential to compromise the computation. The FASTSHARE and FASTRECON algorithms likely employ techniques like secret sharing and homomorphic encryption to achieve privacy and efficiency.
The diagram does not provide specific details about the function being computed or the security guarantees of the protocol. However, it clearly demonstrates a structured approach to secure multi-party computation. The diagram is a high-level overview and does not delve into the mathematical details of the algorithms.