## Flowchart: Cryptographic Protocol for Secure Multi-Party Computation
### Overview
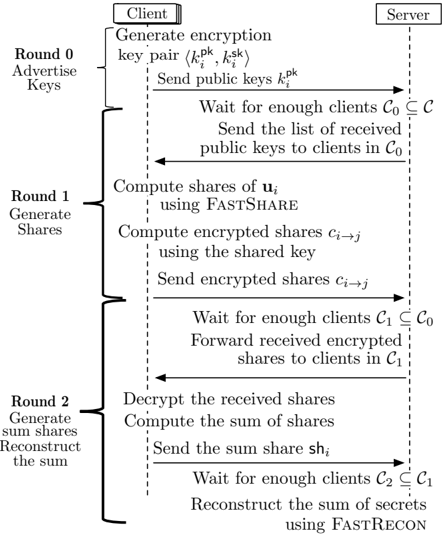
The flowchart depicts a three-round cryptographic protocol for securely computing the sum of secrets among multiple clients. It involves a **Client** and a **Server**, with bidirectional communication flows. Each round builds on the previous one, using encryption, secret sharing, and reconstruction to ensure privacy and correctness.
---
### Components/Axes
1. **Rounds**:
- **Round 0**: Advertise Keys
- **Round 1**: Generate Shares
- **Round 2**: Generate Sum Shares & Reconstruct the Sum
2. **Actors**:
- **Client**: Initiates key generation, share computation, and sum reconstruction.
- **Server**: Coordinates key distribution, encrypted share forwarding, and final sum reconstruction.
3. **Key Cryptographic Primitives**:
- `FastShare`: Secret sharing algorithm.
- `FastRecon`: Secret reconstruction algorithm.
- Encryption/Decryption using shared keys.
---
### Detailed Analysis
#### Round 0: Advertise Keys
- **Client**:
- Generates an encryption key pair: ⟨`k_i^pk`, `k_i^sk`⟩.
- Sends public key `k_i^pk` to the Server.
- **Server**:
- Waits for enough clients (`C₀ ⊆ C`).
- Sends the list of received public keys to clients in `C₀`.
#### Round 1: Generate Shares
- **Client**:
- Computes shares of `u_i` using `FastShare`.
- Encrypts shares `c_i→j` using the shared key.
- Sends encrypted shares to the Server.
- **Server**:
- Waits for enough clients (`C₁ ⊆ C₀`).
- Forwards received encrypted shares to clients in `C₁`.
#### Round 2: Generate Sum Shares & Reconstruct the Sum
- **Client**:
- Decrypts received shares.
- Computes the sum of shares.
- Sends the sum share `sh_i` to the Server.
- **Server**:
- Waits for enough clients (`C₂ ⊆ C₁`).
- Reconstructs the sum of secrets using `FastRecon`.
---
### Key Observations
1. **Hierarchical Dependency**: Each round depends on the completion of the prior round (e.g., `C₁ ⊆ C₀`, `C₂ ⊆ C₁`).
2. **Privacy Preservation**: Encryption and secret sharing ensure no single client knows the full secret.
3. **Efficiency**: Use of `FastShare` and `FastRecon` suggests optimized algorithms for scalability.
4. **Server as Coordinator**: The Server acts as a central authority to enforce participation thresholds.
---
### Interpretation
This protocol enables **secure multi-party computation (MPC)** by distributing trust across clients. The three-round structure ensures:
- **Round 0** establishes trust via key distribution.
- **Round 1** computes encrypted shares to prevent leakage.
- **Round 2** aggregates results while maintaining privacy.
The use of `FastShare`/`FastRecon` implies a focus on computational efficiency, critical for large-scale deployments. Potential risks include reliance on the Server’s integrity and the security of the cryptographic primitives. The protocol assumes clients follow the steps correctly, highlighting the importance of robust implementation.