\n
## Data Table: HW Defense Performance Overhead
### Overview
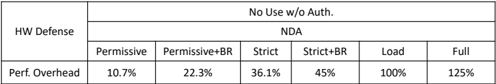
The image presents a data table detailing the performance overhead associated with different Hardware (HW) Defense configurations. The table compares various levels of security settings ("Permissive", "Permissive+BR", "Strict", "Strict+BR", "Load", "Full") against a single metric: "Perf. Overhead" (Performance Overhead). A header indicates "No Use w/o Auth."
### Components/Axes
* **Rows:** HW Defense (single entry)
* **Columns:** Security Levels: Permissive, Permissive+BR, Strict, Strict+BR, Load, Full.
* **Metric:** Perf. Overhead (expressed as a percentage)
* **Header:** "No Use w/o Auth."
### Detailed Analysis or Content Details
The table contains the following data points:
| Security Level | Perf. Overhead |
|---|---|
| Permissive | 10.7% |
| Permissive+BR | 22.3% |
| Strict | 36.1% |
| Strict+BR | 45% |
| Load | 100% |
| Full | 125% |
The "Perf. Overhead" values increase consistently as the security level becomes more restrictive. The overhead starts at 10.7% for the "Permissive" setting and rises to 125% for the "Full" setting.
### Key Observations
* The performance overhead increases significantly with each step up in security level.
* The largest jump in overhead occurs between "Strict+BR" (45%) and "Load" (100%).
* The "Full" setting has the highest performance overhead, at 125%.
### Interpretation
The data suggests a clear trade-off between security and performance. Higher levels of HW Defense provide greater security but come at the cost of increased performance overhead. The "No Use w/o Auth." header implies that these settings are not intended for use without proper authorization, likely due to the significant performance impact. The data could be used to inform decisions about which security level is appropriate for a given application, balancing security needs with performance requirements. The "BR" suffix likely refers to a specific security feature or configuration (e.g., Branch Register protection), and its inclusion further increases the overhead. The jump from Strict+BR to Load suggests a fundamental change in the defense mechanism, potentially involving more extensive checks or resource allocation.