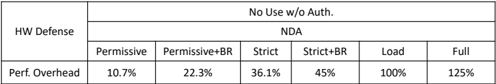
## Table: Hardware Defense Performance Overhead Comparison
### Overview
The image displays a structured data table comparing the performance overhead associated with different hardware (HW) defense configurations. The table is organized into two primary rows and multiple columns, presenting a clear trade-off between security posture and system performance impact.
### Components/Axes
The table is a grid with the following structure:
* **Row 1 (Header - Category):** Contains two main category headers spanning multiple columns:
* `No Use w/o Auth.` (Spanning the first data column)
* `NDA` (Spanning the remaining six data columns)
* **Row 2 (Header - Sub-category):** Lists six specific hardware defense configurations under the `NDA` category:
* `Permissive`
* `Permissive+BR`
* `Strict`
* `Strict+BR`
* `Load`
* `Full`
* **Row 3 (Data Label):** The leftmost cell is labeled `HW Defense`.
* **Row 4 (Data Label & Values):** The leftmost cell is labeled `Perf. Overhead`. The subsequent cells contain the corresponding percentage values for each configuration.
**Spatial Layout:** The legend/category headers are positioned at the top of the table. The specific configuration labels are in the second row from the top. The performance data is aligned in a single row at the bottom.
### Detailed Analysis
The table provides the following precise data points for performance overhead:
| HW Defense Configuration | Performance Overhead |
| :--- | :--- |
| **No Use w/o Auth.** | 10.7% |
| **NDA - Permissive** | 22.3% |
| **NDA - Permissive+BR** | 36.1% |
| **NDA - Strict** | 45% |
| **NDA - Strict+BR** | 100% |
| **NDA - Load** | 125% |
| **NDA - Full** | *(This value is not present in the provided image. The table appears to be cropped or incomplete after the "Load" column.)* |
**Trend Verification:** The data series for "Perf. Overhead" shows a clear and consistent upward trend from left to right. The overhead increases monotonically with each subsequent, presumably stricter, defense configuration.
### Key Observations
1. **Progressive Overhead:** There is a direct, positive correlation between the implied strictness of the hardware defense and the performance cost. The overhead more than doubles from the baseline (`No Use w/o Auth.` at 10.7%) to the `Permissive` NDA configuration (22.3%).
2. **Significant Jumps:** Two notable jumps in overhead occur:
* Between `Strict` (45%) and `Strict+BR` (100%), where the overhead more than doubles.
* Between `Strict+BR` (100%) and `Load` (125%), indicating a 25 percentage point increase.
3. **High Cost of "Load":** The `Load` configuration incurs a 125% performance overhead, meaning the system's performance is effectively more than halved compared to a baseline with no defense overhead.
4. **Incomplete Data:** The table is missing a value for the `Full` configuration, which is listed as a column header. This suggests the image is a partial view of a larger dataset.
### Interpretation
This table quantitatively demonstrates the fundamental trade-off in system security design: enhanced protection comes at a measurable performance cost.
* **What the data suggests:** The configurations likely represent escalating levels of hardware-based security enforcement (e.g., memory protection, access controls, cryptographic operations). The "BR" suffix may denote an additional feature like "Branch Randomization" or "Buffer Restriction," which adds significant overhead. The `Load` and `Full` configurations probably represent the most comprehensive and resource-intensive security modes.
* **How elements relate:** The `NDA` (likely an acronym for a specific defense architecture or framework) is the overarching category for all advanced defenses. Each sub-configuration under `NDA` builds upon the previous one, adding security features and, consequently, performance overhead. The `No Use w/o Auth.` column serves as a baseline reference point.
* **Notable Implications:** The data is critical for system architects and security engineers. It allows for informed decision-making when selecting a security posture. For performance-critical applications, a `Permissive` or `Strict` configuration might be acceptable. For high-security environments where performance is secondary, `Strict+BR` or `Load` might be necessary, despite their severe overhead. The missing `Full` value leaves the upper bound of the performance impact unknown.