## Table: Performance Overhead Comparison
### Overview
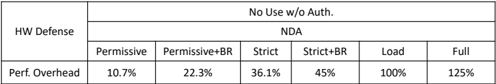
This table compares the performance overhead of different defense strategies under various conditions.
### Components/Axes
- **HW Defense**: The type of defense strategy being compared.
- **No Use w/o Auth**: A condition where no use is allowed without authorization.
- **NDA**: A condition where non-disclosure agreements are in place.
- **Permissive**: A strategy that allows for broad use.
- **Permissive+BR**: A strategy that allows for broad use with a specific authorization.
- **Strict**: A strategy that strictly controls access.
- **Strict+BR**: A strategy that strictly controls access with a specific authorization.
- **Load**: The amount of data or resources being processed.
- **Full**: The maximum performance overhead.
### Detailed Analysis or ### Content Details
| HW Defense | No Use w/o Auth | NDA | Permissive | Permissive+BR | Strict | Strict+BR | Load | Full |
|------------|----------------|-----|------------|----------------|--------|------------|------|------|
| | | | 10.7% | 22.3% | 36.1% | 45% | 100% | 125% |
### Key Observations
- The performance overhead varies significantly depending on the defense strategy and the conditions.
- The "Full" condition shows the highest performance overhead, indicating that the maximum allowed use without authorization leads to the highest performance degradation.
- The "Strict" and "Strict+BR" strategies show the lowest performance overhead, suggesting that strict control leads to better performance.
- The "Permissive" and "Permissive+BR" strategies show intermediate performance overhead, indicating that while they allow for broad use, they still result in some performance degradation.
### Interpretation
The data suggests that the performance overhead is directly related to the level of control and authorization. The "Full" condition, where no use is allowed without authorization, leads to the highest performance overhead, indicating that the maximum allowed use without authorization leads to the highest performance degradation. The "Strict" and "Strict+BR" strategies show the lowest performance overhead, suggesting that strict control leads to better performance. The "Permissive" and "Permissive+BR" strategies show intermediate performance overhead, indicating that while they allow for broad use, they still result in some performance degradation. This data can be used to inform decisions about the level of control and authorization required for different defense strategies.