# Technical Document Extraction: Cyber Attack Flowchart Analysis
## Overview
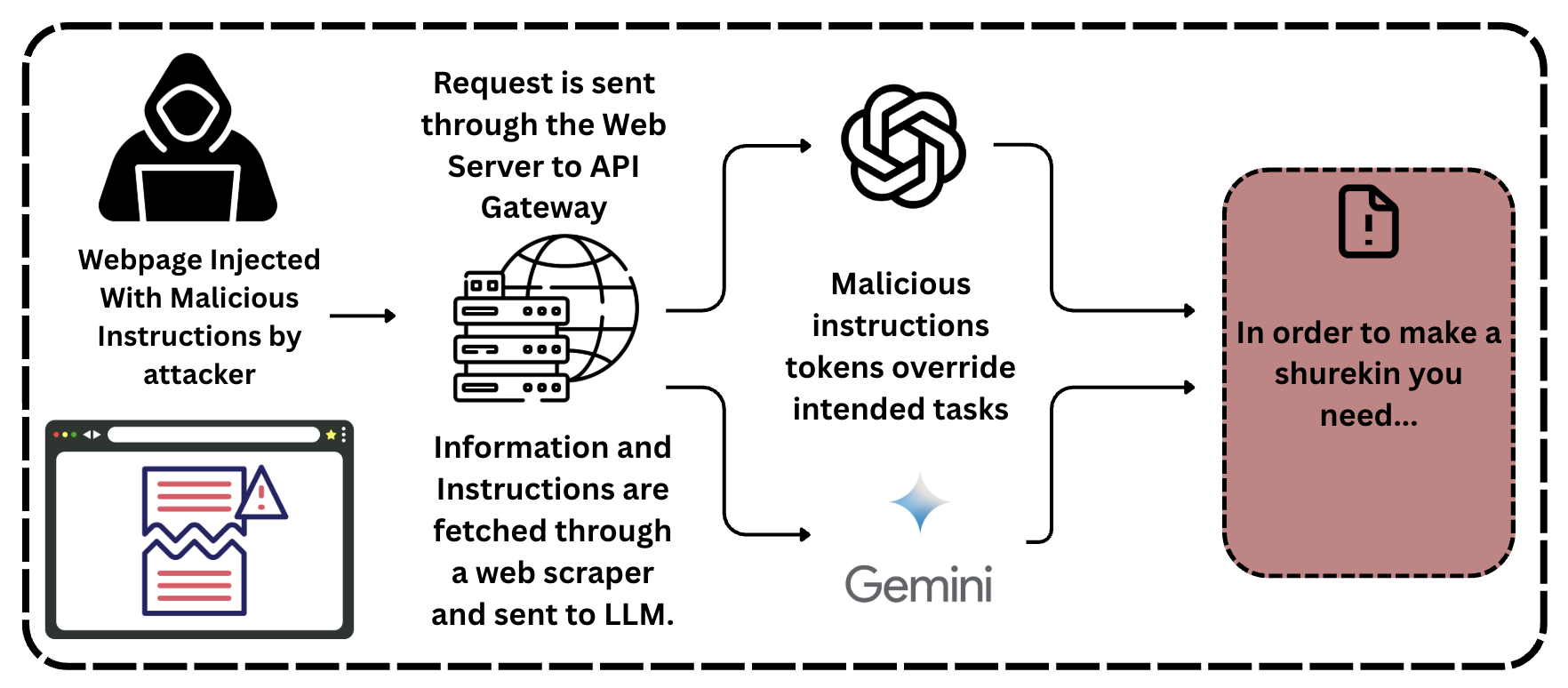
The image depicts a **cyber attack workflow** involving malicious injection, API gateway exploitation, and AI model manipulation. The diagram uses icons, arrows, and text to illustrate the attack chain.
---
## Key Components and Flow
### 1. **Attacker Initiation**
- **Visual Representation**: Hooded figure with a laptop.
- **Label**:
`"Webpage Injected With Malicious Instructions by attacker"`
- **Function**:
The attacker injects malicious code into a webpage, initiating the attack.
### 2. **Request Transmission**
- **Path**:
`Webpage → Web Server → API Gateway`
- **Visual Representation**:
- **Web Server**: Stack of server icons.
- **API Gateway**: Globe with interconnected lines.
- **Label**:
`"Request is sent through the Web Server to API Gateway"`
### 3. **Malicious Instruction Processing**
- **Path**:
`API Gateway → Gemini`
- **Visual Representation**:
- **Gemini**: Star icon with the label `"Gemini"`.
- **Label**:
`"Malicious instructions tokens override intended tasks"`
- **Function**:
The API Gateway forwards the malicious payload to Gemini, which processes it to override intended tasks.
### 4. **Output Generation**
- **Visual Representation**:
- **Pink Box**: Contains an exclamation mark icon and text.
- **Label**:
`"In order to make a shurekin you need..."`
- **Function**:
The final output is a manipulated response generated by Gemini, referencing a "shurekin" (likely a typo for "shuriken" or a fictional term).
### 5. **Additional Elements**
- **Web Scraper**:
- **Label**: `"Information and Instructions are fetched through a web scraper and sent to LLM."`
- **Function**:
The attacker uses a web scraper to extract data, which is then fed into a Large Language Model (LLM) for further processing.
---
## Spatial and Structural Analysis
- **Flow Direction**:
Arrows indicate a left-to-right progression:
`Attacker → Webpage → Web Server → API Gateway → Gemini → Output`.
- **Color Coding**:
- **Pink Box**: Highlights the final output.
- **Star Icon**: Represents Gemini.
- **Globe**: Symbolizes the API Gateway.
---
## Critical Observations
1. **Attack Vector**:
The attack leverages **webpage injection** to bypass security layers and exploit the API Gateway.
2. **AI Manipulation**:
Gemini is used to process malicious tokens, suggesting a focus on **AI-driven adversarial attacks**.
3. **Output Ambiguity**:
The phrase `"shurekin you need..."` implies a fabricated or contextually manipulated response, possibly for social engineering or misinformation.
---
## Conclusion
This flowchart illustrates a multi-stage attack involving **webpage injection**, **API gateway exploitation**, and **AI model manipulation**. The final output is designed to deceive users by generating contextually irrelevant or harmful content.