\n
## Diagram: Secure Launch Process
### Overview
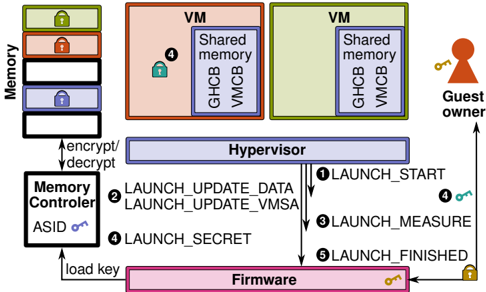
The image depicts a diagram illustrating a secure launch process involving firmware, a hypervisor, virtual machines (VMs), a memory controller, and a guest owner. The diagram shows the flow of operations and data exchange between these components during the launch sequence. It highlights security aspects like encryption/decryption and key loading.
### Components/Axes
The diagram includes the following components:
* **Memory:** Represented as a vertical stack of locked boxes.
* **Memory Controller:** Located on the bottom-left, labeled "Memory Controller" with "ASID" and a key icon.
* **Firmware:** Located at the bottom, labeled "Firmware" with a key icon.
* **Hypervisor:** A large blue rectangle in the center, labeled "Hypervisor".
* **VM (Virtual Machine):** Two rectangular boxes, one peach-colored and one green, both labeled "VM" and containing "Shared memory", "GHCB", and "VMCB".
* **Guest Owner:** A key icon on the right side, labeled "Guest owner".
The diagram also shows the following operations/data flows:
1. LAUNCH\_START
2. LAUNCH\_UPDATE\_DATA
3. LAUNCH\_UPDATE\_VMSA
4. LAUNCH\_SECRET
5. LAUNCH\_FINISHED
Additionally, there are labels indicating "encrypt/decrypt" and "load key".
### Detailed Analysis or Content Details
The diagram illustrates a sequential process:
1. **LAUNCH\_START (1):** An arrow originates from the Hypervisor and points towards the Guest Owner, accompanied by a key icon, indicating a key exchange.
2. **LAUNCH\_UPDATE\_DATA (2):** An arrow originates from the Hypervisor and points towards the Firmware, labeled "LAUNCH\_UPDATE\_DATA".
3. **LAUNCH\_UPDATE\_VMSA (2):** An arrow originates from the Hypervisor and points towards the Firmware, labeled "LAUNCH\_UPDATE\_VMSA".
4. **LAUNCH\_SECRET (4):** An arrow originates from the Memory Controller and points towards the Hypervisor, labeled "LAUNCH\_SECRET". The Memory Controller has a key icon indicating key loading.
5. **LAUNCH\_MEASURE (3):** An arrow originates from the Hypervisor and points towards the Firmware, labeled "LAUNCH\_MEASURE".
6. **LAUNCH\_FINISHED (5):** An arrow originates from the Firmware and points towards the Hypervisor, accompanied by a locked key icon, indicating a secure completion.
The Memory Controller is connected to the Memory stack via an arrow labeled "ASID". The Hypervisor is connected to the two VMs. The VMs both contain "Shared memory", "GHCB", and "VMCB". The Hypervisor encrypts/decrypts data from the Memory stack. The peach VM has a lock icon (4) within it.
### Key Observations
The diagram emphasizes a secure launch process with multiple stages involving key exchange, data updates, measurement, and secure completion. The use of encryption/decryption and key loading suggests a focus on protecting sensitive data and ensuring the integrity of the launch process. The ASID in the Memory Controller suggests address space isolation. The two VMs indicate a virtualized environment.
### Interpretation
The diagram illustrates a trusted launch sequence, likely within a virtualized environment. The process begins with the firmware loading keys and receiving updates from the hypervisor. The hypervisor then initiates the launch process with the guest owner, exchanging keys. The memory controller plays a role in securing memory access using ASID. The hypervisor manages the VMs, providing shared memory and virtual machine control blocks (VMCB). The final stage, "LAUNCH\_FINISHED", signifies a secure and verified launch. The lock icons suggest encryption or access control mechanisms. The diagram highlights the importance of a secure boot process to establish a trusted computing base. The flow suggests a root of trust starting with the firmware and extending through the hypervisor to the VMs. The diagram is a high-level overview and does not provide specific details about the algorithms or protocols used for encryption, key exchange, or measurement.