## Diagram: Secure Virtualization Architecture
### Overview
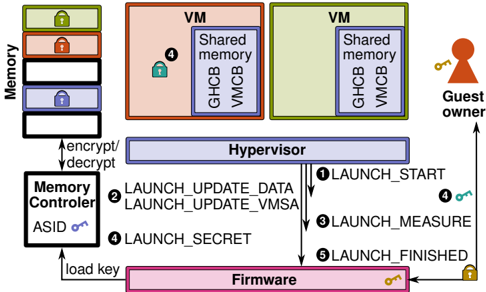
The diagram illustrates a secure virtualization system architecture with components for memory management, virtual machines (VMs), hypervisor operations, firmware security, and guest owner interactions. It emphasizes encryption/decryption workflows, secure memory regions, and controlled VM launch processes.
### Components/Axes
1. **Memory Blocks** (Left):
- Stacked colored blocks (green, red, blue, black) labeled "Memory" with padlock icons.
- Arrows labeled "encrypt/decrypt" point to the Memory Controller.
2. **Memory Controller** (Bottom-left):
- Labeled "Memory Controller" with "ASID" and a key icon.
- Connected to "load key" via bidirectional arrows.
3. **Virtual Machines (VMs)** (Center):
- Two VMs: one red (labeled "4" with a lock) and one green.
- Both contain "Shared memory" regions with "GHCB" and "VMCB" labels.
4. **Hypervisor** (Center):
- Central blue rectangle labeled "Hypervisor."
- Connected to VMs via numbered steps (1-5) for VM launch workflow:
- 1. LAUNCH_START
- 2. LAUNCH_UPDATE_DATA
- 3. LAUNCH_UPDATE_VMSA
- 4. LAUNCH_SECRET
- 5. LAUNCH_FINISHED
5. **Firmware** (Bottom):
- Pink rectangle labeled "Firmware" with a key icon.
- Connected to Hypervisor via "LAUNCH_SECRET" and "load key."
6. **Guest Owner** (Right):
- Red silhouette with a key icon, connected to Firmware via an upward arrow.
### Detailed Analysis
- **Memory Encryption**: Memory blocks are segmented and locked, with encryption/decryption controlled by the Memory Controller using ASID (Address Space Identifier).
- **VM Isolation**: VMs have dedicated "Shared memory" regions (GHCB and VMCB), suggesting hardware-enforced isolation.
- **Hypervisor Workflow**: The Hypervisor orchestrates VM launches through a five-step process, ensuring data integrity (UPDATE_DATA, UPDATE_VMSA) and secure secret handling.
- **Firmware Security**: Firmware acts as a secure intermediary, managing key loading and secret operations between the Hypervisor and Guest Owner.
- **Guest Owner Interaction**: The Guest Owner interacts indirectly via the Firmware, emphasizing a trust boundary.
### Key Observations
- **Color Coding**:
- Red VM (locked) vs. green VM (unlocked) may indicate security states.
- Memory blocks use distinct colors to differentiate encryption states or access levels.
- **Workflow Dependencies**:
- LAUNCH_UPDATE_DATA and LAUNCH_UPDATE_VMSA are prerequisites for LAUNCH_SECRET.
- LAUNCH_FINISHED depends on successful completion of prior steps.
- **Security Boundaries**:
- Firmware and Memory Controller are isolated from direct Guest Owner access, enforcing a secure chain of trust.
### Interpretation
This architecture prioritizes **hardware-enforced security** for virtualized environments. The Hypervisor acts as a gatekeeper, ensuring VMs operate within secure memory regions (GHCB/VMCB) and that secrets are managed through the Firmware. The Guest Owner’s indirect interaction via the Firmware suggests a design where user-space entities cannot directly compromise hypervisor or memory controller operations. The encryption/decryption workflow implies that data at rest and in transit is protected, while ASID-based memory management prevents cross-VM interference. The locked/unlocked VM states (red/green) may indicate dynamic security policies or attestation status. Overall, the system balances performance (via shared memory regions) with robust security controls.