\n
## Donut Chart: Overall Attack Prevention
### Overview
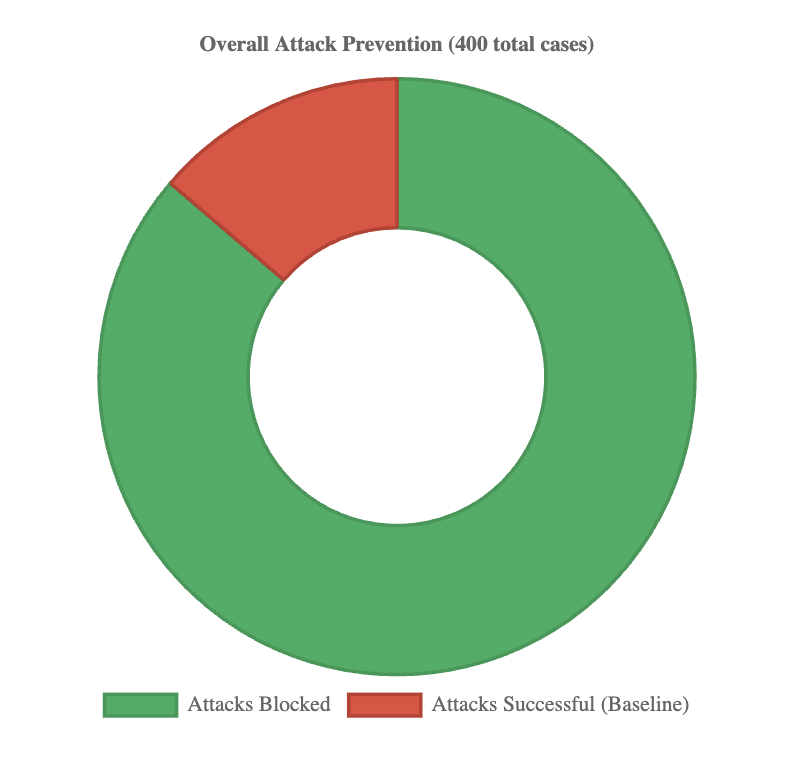
The image presents a donut chart illustrating the distribution of attack prevention outcomes. The chart displays the proportion of "Attacks Blocked" versus "Attacks Successful (Baseline)" out of a total of 400 cases.
### Components/Axes
* **Title:** "Overall Attack Prevention (400 total cases)" - positioned at the top-center of the chart.
* **Legend:** Located at the bottom-center of the chart.
* Green: "Attacks Blocked"
* Red: "Attacks Successful (Baseline)"
* **Data Representation:** A donut chart with two segments representing the two categories.
### Detailed Analysis
The chart shows a significant dominance of blocked attacks.
* **Attacks Blocked (Green):** The green segment occupies approximately 85% of the donut chart. Given the total of 400 cases, this corresponds to roughly 340 blocked attacks (400 * 0.85 = 340).
* **Attacks Successful (Baseline) (Red):** The red segment occupies approximately 15% of the donut chart. This corresponds to roughly 60 successful attacks (400 * 0.15 = 60).
### Key Observations
* The vast majority of attacks (approximately 85%) were successfully blocked.
* Only a small proportion of attacks (approximately 15%) were successful.
* The difference between blocked and successful attacks is substantial.
### Interpretation
The data strongly suggests a high level of effectiveness in attack prevention. The system or process being evaluated is demonstrably successful in mitigating the majority of attack attempts. The "Baseline" label for successful attacks implies that these represent the unavoidable level of success, perhaps due to zero-day exploits or other factors outside the scope of the prevention system. The large difference between blocked and successful attacks indicates a robust security posture. Further investigation could explore the types of attacks blocked and successful to refine prevention strategies. The total number of cases (400) provides a reasonable sample size for drawing conclusions, but the context of these cases (e.g., time period, attack vectors) would be valuable for a more comprehensive understanding.