## Diagram: Software Exception Handler Flow (QEMU vs. Real Device)
### Overview
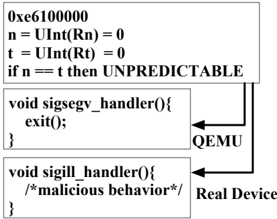
This image is a technical diagram illustrating the flow of control for two software exception handlers (`sigsegv_handler` and `sigill_handler`) in two different execution environments: the QEMU emulator and a "Real Device". It shows a conditional check that leads to an "UNPREDICTABLE" state, which then routes to the respective handlers. The diagram highlights a potential security or behavioral divergence between the emulated and real hardware environments.
### Components/Axes
The diagram is composed of three primary rectangular blocks connected by directional arrows, with two environmental labels.
1. **Top Block (Conditional Check):**
* **Text Content:**
```
0xe6100000
n = UInt(Rn) = 0
t = UInt(Rt) = 0
if n == t then UNPREDICTABLE
```
* **Position:** Top-center of the image.
2. **Middle Block (Handler 1):**
* **Text Content:**
```
void sigsegv_handler(){
exit(0);
}
```
* **Position:** Center-left, below the top block.
3. **Bottom Block (Handler 2):**
* **Text Content:**
```
void sigill_handler(){
/*malicious behavior*/
}
```
* **Position:** Bottom-left, below the middle block.
4. **Environmental Labels & Flow Arrows:**
* **Label "QEMU":** Positioned to the right of the middle block. An arrow points from this label to the `sigsegv_handler` block.
* **Label "Real Device":** Positioned to the right of the bottom block. An arrow points from this label to the `sigill_handler` block.
* **Primary Flow Arrow:** A thick, black arrow originates from the right side of the top block (the "UNPREDICTABLE" condition) and splits, pointing towards both the `sigsegv_handler` and `sigill_handler` blocks. This indicates that the "UNPREDICTABLE" state triggers a call to one of these handlers.
### Detailed Analysis
* **Text Transcription:** All text is in English and has been transcribed verbatim above, including code syntax and the comment `/*malicious behavior*/`.
* **Flow Logic:**
1. The process begins with a memory address or value `0xe6100000`.
2. Two variables, `n` and `t`, are derived from registers `Rn` and `Rt` using `UInt()` (likely "Unsigned Integer"), and both are set to `0`.
3. A conditional check `if n == t` evaluates to true, leading to an `UNPREDICTABLE` architectural state (a term often used in ARM/AArch64 specification).
4. From this `UNPREDICTABLE` state, the diagram shows a flow to exception handlers.
* **Environmental Divergence:** The diagram explicitly separates the handling path based on the execution environment:
* In **QEMU**, the `sigsegv_handler` is invoked, which simply calls `exit(0)`, terminating the program cleanly.
* On the **Real Device**, the `sigill_handler` is invoked, which contains a comment indicating it executes "malicious behavior".
### Key Observations
1. **Identical Trigger, Different Outcomes:** The same architectural condition (`UNPREDICTABLE` due to `n == t == 0`) results in completely different program behavior depending on whether it runs on an emulator (QEMU) or real hardware.
2. **Security Implication:** The comment `/*malicious behavior*/` in the `sigill_handler` is a critical annotation. It suggests this diagram is likely from a security analysis, exploit demonstration, or research paper showing how an emulator can mask malicious code that would execute on real hardware.
3. **Handler Purpose:** The `sigsegv_handler` (Segmentation Violation) is used for a clean exit in the emulator, while the `sigill_handler` (Illegal Instruction) is repurposed for the payload on the real device.
### Interpretation
This diagram demonstrates a **differential behavior analysis** between an emulated environment and real hardware, a common technique in security research and reverse engineering.
* **What it Suggests:** The data (code flow) suggests the existence of an **emulator detection** or **environment fingerprinting** technique. The program checks a condition that leads to an architecturally `UNPREDICTABLE` state. The authors know that QEMU and a real CPU will handle this undefined behavior differently. QEMU likely implements a safe, deterministic response (calling a segfault handler that exits), while the real hardware's response is leveraged to trigger a different code path (an illegal instruction handler) that contains the actual malicious payload.
* **Relationship Between Elements:** The top block is the **trigger**. The split arrow represents the **fork in behavior**. The two handler blocks and their associated labels ("QEMU", "Real Device") represent the **divergent outcomes**. The comment is the **key insight**, revealing the intent behind the divergence.
* **Notable Anomalies:** The primary anomaly is the intentional creation of an `UNPREDICTABLE` state. In normal software, this is avoided. Here, it is weaponized as a covert channel to differentiate environments. The use of `sigill_handler` for "malicious behavior" is also anomalous, as this handler is typically for genuine illegal instruction faults, not intentional payloads.
* **Why it Matters:** This illustrates a sophisticated anti-analysis technique. Security tools and analysts often run samples in sandboxes (like QEMU-based ones) to observe behavior safely. This code would appear benign in such an environment (just exiting), but would deploy its payload only on a victim's real machine, evading detection. It underscores the challenge of malware analysis and the need for hardware-level analysis or more advanced emulation that can mimic such subtle architectural quirks.