## Diagram: Secret Sharing Scheme using DFT and Peeling Decoder
### Overview
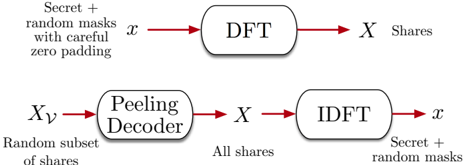
The image illustrates a secret sharing scheme using Discrete Fourier Transform (DFT) and a Peeling Decoder. The scheme involves encoding a secret with random masks using DFT, distributing shares, and then reconstructing the secret using a Peeling Decoder and Inverse Discrete Fourier Transform (IDFT).
### Components/Axes
The diagram consists of the following components:
* **DFT Block:** A rounded rectangle labeled "DFT".
* **IDFT Block:** A rounded rectangle labeled "IDFT".
* **Peeling Decoder Block:** A rounded rectangle labeled "Peeling Decoder".
* **Input/Output Variables:**
* *x*: Represents the secret combined with random masks and careful zero padding.
* *X*: Represents the shares generated by the DFT.
* *X<sub>v</sub>*: Represents a random subset of shares.
* **Arrows:** Red arrows indicating the flow of data.
* **Text Labels:**
* "Secret + random masks with careful zero padding" near the input *x* to the DFT.
* "Shares" near the output *X* of the DFT.
* "Random subset of shares" near the input *X<sub>v</sub>* to the Peeling Decoder.
* "All shares" near the input *X* to the IDFT.
* "Secret + random masks" near the output *x* of the IDFT.
### Detailed Analysis
The diagram can be divided into two main stages: encoding and decoding.
**Encoding (Top Row):**
1. The secret *x*, combined with random masks and careful zero padding, is input to the DFT block.
2. The DFT block transforms the input *x* into *X*, which represents the shares.
3. The shares *X* are distributed.
**Decoding (Bottom Row):**
1. A random subset of shares, *X<sub>v</sub>*, is input to the Peeling Decoder block.
2. The Peeling Decoder processes the subset of shares and outputs *X*, representing all shares.
3. All shares *X* are input to the IDFT block.
4. The IDFT block transforms the shares back into *x*, which represents the reconstructed secret combined with random masks.
### Key Observations
* The DFT is used to encode the secret into shares.
* A subset of shares is sufficient for the Peeling Decoder to reconstruct all shares.
* The IDFT is used to reconstruct the secret from the shares.
* Random masks are used to protect the secret during encoding and decoding.
### Interpretation
The diagram illustrates a secret sharing scheme that leverages the properties of DFT and a Peeling Decoder. The DFT allows for the distribution of the secret into multiple shares, while the Peeling Decoder enables the reconstruction of all shares from a subset. This scheme provides a level of security, as the secret cannot be recovered without a sufficient number of shares. The use of random masks further enhances the security by obscuring the secret during encoding and decoding. The scheme is robust, as it can tolerate the loss of some shares without compromising the ability to reconstruct the secret.