## Diagram: Authorization Process Flow for Short vs. Long Access
### Overview
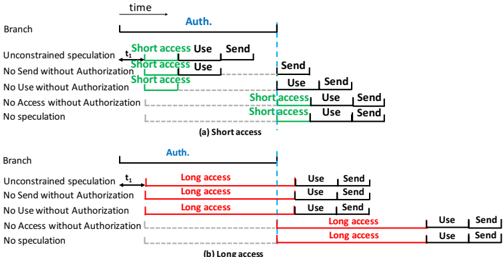
The diagram illustrates two parallel branches of a process flow, comparing "Short access" (green) and "Long access" (red) scenarios under authorization constraints. Time progresses left to right, with a vertical "Auth." marker indicating authorization events. Each branch includes conditional paths based on authorization status and access duration.
### Components/Axes
- **X-axis**: Labeled "time," with a vertical "Auth." marker dividing the timeline.
- **Branches**:
- **(a) Short access**: Green-highlighted steps.
- **(b) Long access**: Red-highlighted steps.
- **Legend**:
- Green = Short access
- Red = Long access
- **Key Labels**:
- "Unconstrained speculation" (initial state)
- "No Send without Authorization"
- "No Use without Authorization"
- "No Access without Authorization"
- "No speculation" (terminal state)
### Detailed Analysis
#### Branch (a): Short access
1. **Timeline**:
- Starts at "Unconstrained speculation" (t₁).
- Proceeds to "Short access Use Send" (green section).
- Post-authorization ("Auth."), transitions to "Send" and "Use" actions.
2. **Conditions**:
- "No Send without Authorization" and "No Use without Authorization" enforce authorization checks.
- "No Access without Authorization" terminates the branch if authorization fails.
#### Branch (b): Long access
1. **Timeline**:
- Starts at "Unconstrained speculation" (t₁).
- Enters "Long access" (red section), spanning a longer duration than Branch (a).
- Post-authorization, transitions to "Use" and "Send" actions.
2. **Conditions**:
- Similar authorization checks as Branch (a), but "Long access" persists longer.
- "No speculation" terminates the branch if authorization fails.
### Key Observations
- **Access Duration**: Branch (b) has a visibly longer "Long access" phase compared to Branch (a).
- **Authorization Dependency**: Both branches require authorization to proceed beyond "Unconstrained speculation."
- **Color Coding**: Green (short) and red (long) visually distinguish access types.
- **Flow Divergence**: Post-authorization, both branches converge on "Use" and "Send" actions but differ in access duration.
### Interpretation
The diagram demonstrates how authorization gates access duration in a process flow. Short access (green) allows brief, controlled use/send actions, while long access (red) extends the authorization period, enabling prolonged operations. The "Auth." marker acts as a critical control point, ensuring no actions proceed without validation. The parallel branches highlight trade-offs between access duration and security constraints, with longer access requiring stricter adherence to authorization protocols.
**Note**: No numerical data or quantitative values are present; the diagram focuses on qualitative process flow and conditional logic.