## Diagram: Protocol Negotiation and Private Data Access
### Overview
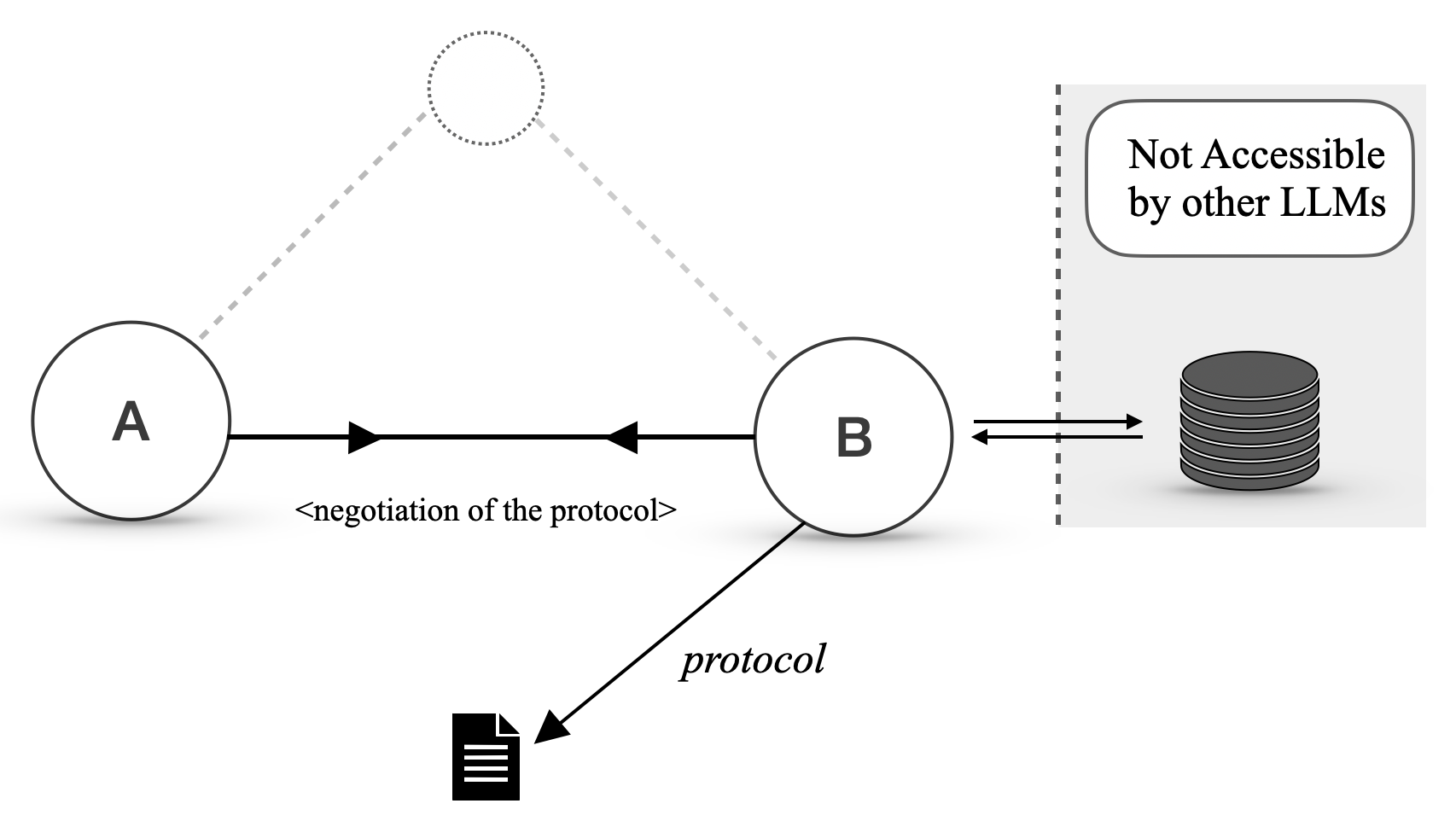
The image is a technical diagram illustrating a communication protocol negotiation between two entities (labeled A and B), where entity B has exclusive access to a private data store. The diagram uses circles, arrows, icons, and text to depict the flow of negotiation, the resulting protocol, and a restricted data resource.
### Components/Axes
The diagram is composed of the following spatially arranged elements:
1. **Entity A**: A circle on the left side, labeled with the letter "A".
2. **Entity B**: A circle in the center, labeled with the letter "B".
3. **Dotted Circle**: A circle with a dotted outline, positioned above and between A and B. It is connected to both A and B by dashed grey lines.
4. **Negotiation Channel**: A thick, solid black line with arrowheads at both ends connecting A and B directly. Below this line is the text: `<negotiation of the protocol>`.
5. **Protocol Output**: A solid black arrow originates from the bottom of circle B and points diagonally down-left to a document icon. The label `protocol` is written along this arrow.
6. **Document Icon**: A black icon representing a text document, located at the bottom-center of the diagram.
7. **Private Data Store**: A cylinder icon (representing a database) located on the right side of the diagram, within a light grey shaded box.
8. **Access Boundary**: A vertical dashed line separates entity B from the shaded box containing the database.
9. **Access Restriction Label**: Inside the shaded box, above the database icon, is a rounded rectangle containing the text: `Not Accessible by other LLMs`.
10. **Data Channel**: A pair of thin, solid black arrows (one pointing left, one pointing right) connect entity B to the database icon, crossing the dashed boundary line.
### Detailed Analysis
* **Flow and Relationships**:
* The primary interaction is a bidirectional negotiation between A and B, as indicated by the double-headed arrow and its label.
* The dotted circle above may represent an external reference, a third-party service, or a conceptual space for the negotiation context, connected via dashed (likely indirect or potential) links.
* Following the negotiation, entity B produces or outputs a "protocol," represented by the arrow pointing to the document icon.
* Entity B has a bidirectional data connection (read/write) with a database. This connection is explicitly marked as being behind a boundary (the dashed line) and is labeled as inaccessible to other Large Language Models (LLMs).
* **Text Transcription**:
* `A` (Label for left circle)
* `B` (Label for center circle)
* `<negotiation of the protocol>` (Label for the A-B channel)
* `protocol` (Label for the arrow from B to the document)
* `Not Accessible by other LLMs` (Label inside the shaded box)
### Key Observations
1. **Asymmetric Access**: The diagram highlights a key asymmetry. While A and B can negotiate, only B is shown to have a direct, privileged connection to a data resource.
2. **Protocol as an Output**: The negotiation results in a tangible output—a protocol document—suggesting the process is formalized and recorded.
3. **Exclusivity**: The label "Not Accessible by other LLMs" is a critical design constraint, indicating the data store is private to this specific system or agent (B) and is a protected component.
4. **Visual Hierarchy**: The shaded box and dashed line create a strong visual boundary, emphasizing the isolation and security of the data store.
### Interpretation
This diagram models a system where two agents (A and B) establish a communication or interaction protocol through negotiation. The core insight is that agent B serves as a gateway or privileged actor with exclusive access to a private knowledge base or data repository. This setup suggests several possible scenarios:
* **A Specialized Agent**: B could be a specialized AI agent or service that has been trained on or has access to proprietary data. Agent A (which could be a user, another AI, or a client system) must first negotiate the terms of interaction (the protocol) with B before receiving the formal protocol specification. The actual data remains behind B, inaccessible to A or other external LLMs.
* **Security and Privacy Model**: The diagram explicitly enforces a security model. The private data is siloed, and access is mediated solely through the negotiated protocol and entity B. This prevents direct data leakage to other models.
* **Process Abstraction**: The dotted circle may represent the abstract "problem space" or "negotiation context" that both A and B reference, but which does not hold data itself.
In essence, the diagram illustrates a pattern for integrating private, sensitive data with AI systems by creating a controlled negotiation layer (B) that outputs a defined protocol, thereby protecting the underlying data from unauthorized access or exposure to other models.