## Flowchart: Covert Sending Methodologies
### Overview
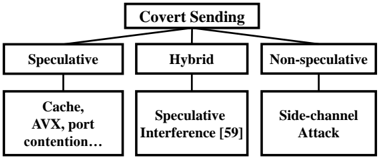
The diagram illustrates a hierarchical classification of covert sending techniques, organized into three primary categories: **Speculative**, **Hybrid**, and **Non-speculative**. Each category branches into specific subcategories, with references to technical methods and potential attack vectors.
### Components/Axes
- **Main Title**: "Covert Sending" (centered at the top).
- **Primary Branches**:
1. **Speculative** (left branch)
2. **Hybrid** (center branch)
3. **Non-speculative** (right branch)
- **Subcategories**:
- **Speculative**:
- Cache
- AVX
- Port contention...
- **Hybrid**:
- Speculative Interference [59]
- **Non-speculative**:
- Side-channel Attack
### Detailed Analysis
- **Speculative Branch**:
- Subcategories include hardware-level techniques like **Cache** (exploiting cache timing), **AVX** (Advanced Vector Extensions for speculative execution), and **port contention** (resource contention attacks). The ellipsis (...) suggests additional unspecified methods.
- **Hybrid Branch**:
- Contains **Speculative Interference [59]**, where "[59]" likely denotes a citation or reference to a specific study or paper.
- **Non-speculative Branch**:
- Lists **Side-channel Attack**, a method that infers data through physical leakage (e.g., power consumption, electromagnetic emissions).
### Key Observations
1. The diagram emphasizes **speculative execution** as a dominant theme, with two branches (Speculative and Hybrid) directly or indirectly referencing it.
2. The **Hybrid** category acts as a bridge between speculative and non-speculative methods, suggesting a combination of techniques.
3. **Side-channel Attack** is isolated under Non-speculative, indicating it operates outside speculative execution frameworks.
### Interpretation
This flowchart categorizes covert sending methods based on their reliance on speculative execution. The **Speculative** and **Hybrid** branches highlight vulnerabilities in modern hardware (e.g., cache timing attacks, AVX-based exploits), while the **Non-speculative** branch focuses on classical side-channel methods. The inclusion of a citation ([59]) for Speculative Interference implies empirical validation of this technique. The separation of Side-channel Attacks suggests they are considered distinct from speculative methods, possibly due to differing attack surfaces or mitigation strategies. The diagram underscores the evolving landscape of covert communication in computing, where speculative execution vulnerabilities (e.g., Spectre/Meltdown) have become critical attack vectors.