## Flowchart: Hardware Defenses of Speculative Execution Attacks
### Overview
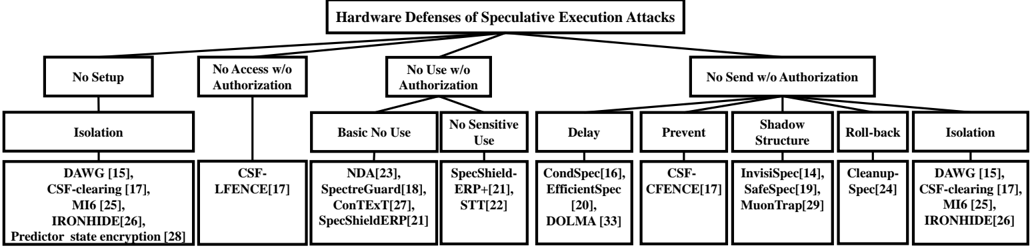
The flowchart categorizes hardware-based defenses against speculative execution attacks, organized into four primary branches: **No Setup**, **No Access w/o Authorization**, **No Use w/o Authorization**, and **No Send w/o Authorization**. Each branch further subdivides into specific defense strategies, with citations provided for each technique.
### Components/Axes
- **Main Title**: "Hardware Defenses of Speculative Execution Attacks"
- **Primary Branches**:
1. **No Setup**
2. **No Access w/o Authorization**
3. **No Use w/o Authorization**
4. **No Send w/o Authorization**
- **Subcategories**:
- **Isolation** (appears under "No Setup" and "No Send w/o Authorization")
- **Basic No Use** (under "No Access w/o Authorization" and "No Use w/o Authorization")
- **No Sensitive Use** (under "No Use w/o Authorization")
- **Delay** (under "No Send w/o Authorization")
- **Prevent** (under "No Send w/o Authorization")
- **Shadow Structure** (under "No Send w/o Authorization")
- **Roll-back** (under "No Send w/o Authorization")
### Detailed Analysis
#### No Setup
- **Isolation**:
- DAWG [15]
- CSF-clearing [17]
- MI6 [25]
- IRONHIDE [26]
- Predictor state encryption [28]
#### No Access w/o Authorization
- **Isolation**:
- CSF-LFENCE [17]
- **Basic No Use**:
- NDA [23]
- SpectreGuard [18]
- ConTeXt [27]
- SpecShieldERP [21]
#### No Use w/o Authorization
- **Basic No Use**:
- NDA [23]
- SpectreGuard [18]
- ConTeXt [27]
- SpecShieldERP [21]
- **No Sensitive Use**:
- SpecShield-ERP+ [21]
- STT [22]
#### No Send w/o Authorization
- **Delay**:
- CondSpec [16]
- EfficientSpec [20]
- DOLMA [33]
- **Prevent**:
- CSF-CFENCE [17]
- **Shadow Structure**:
- InvisiSpec [14]
- SafeSpec [19]
- MuonTrap [29]
- **Roll-back**:
- Cleanup-Spec [24]
- **Isolation**:
- DAWG [15]
- CSF-clearing [17]
- MI6 [25]
- IRONHIDE [26]
### Key Observations
1. **Isolation** is a recurring defense strategy, appearing under both "No Setup" and "No Send w/o Authorization" branches.
2. **CSF-clearing** and **CSF-CFENCE** are variations of the same core concept, differentiated by implementation (e.g., [17] vs. [17]).
3. **SpecShieldERP** and **SpecShield-ERP+** suggest incremental improvements or variants of the same technique.
4. **MI6** and **IRONHIDE** are listed under both "No Setup" and "No Send w/o Authorization," indicating their broad applicability.
### Interpretation
The flowchart emphasizes a layered, multi-faceted approach to mitigating speculative execution attacks. Key trends include:
- **Authorization-Centric Defenses**: The "No Access" and "No Use" branches highlight the importance of access control and usage restrictions.
- **Isolation as a Universal Strategy**: Its repeated use suggests it is a foundational defense mechanism.
- **Specialized Techniques**: Methods like **Shadow Structure** (e.g., InvisiSpec, SafeSpec) and **Roll-back** (Cleanup-Spec) address specific attack vectors, such as data leakage or incorrect state restoration.
The diagram underscores the diversity of hardware-based countermeasures, ranging from basic isolation to advanced techniques like shadow structures and roll-back mechanisms. The citations indicate a reliance on peer-reviewed research, with newer or more specialized methods (e.g., DOLMA [33]) potentially representing cutting-edge solutions.