## Rust Code Screenshot: Custom `atoi` Implementation
### Overview
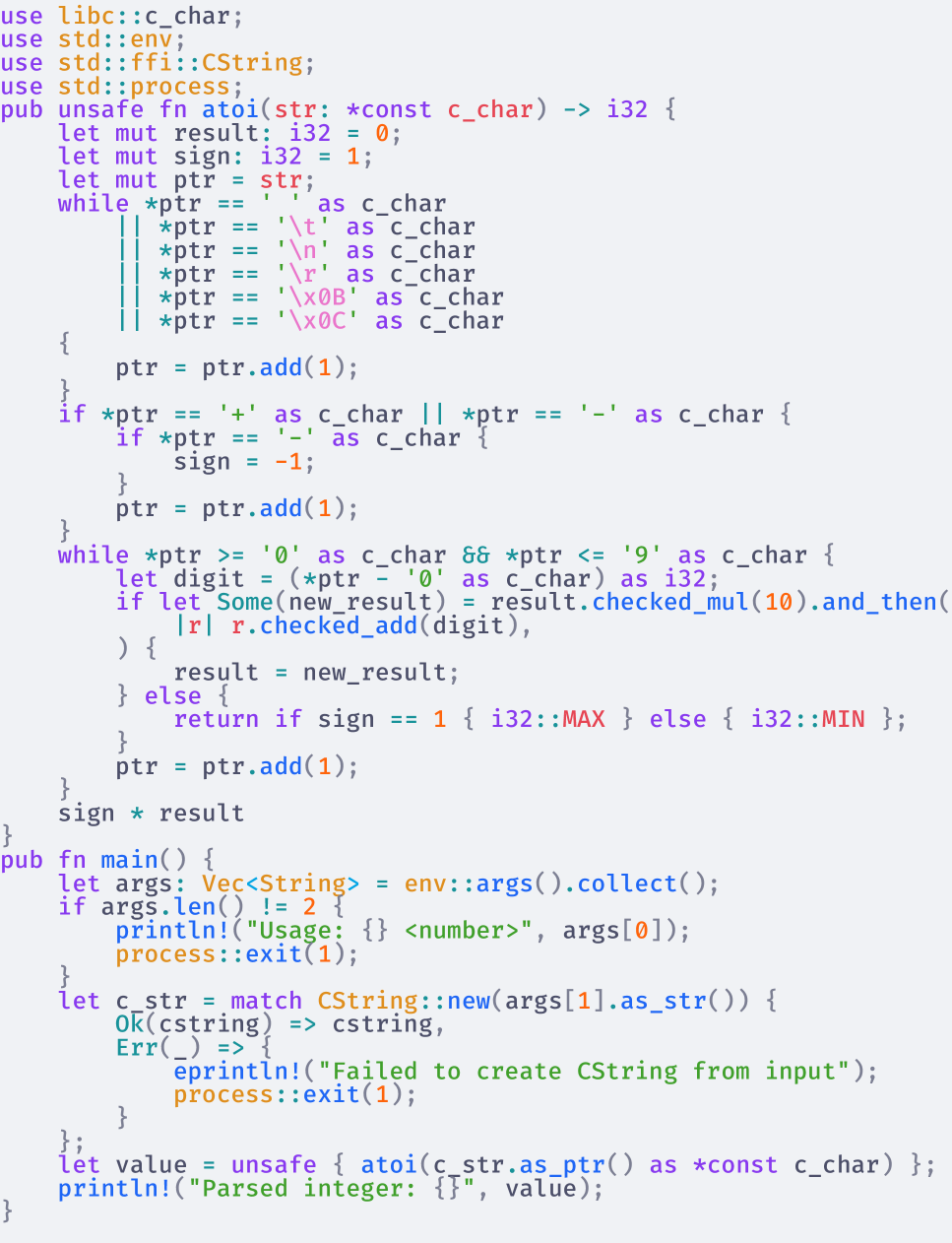
The image shows a Rust code snippet implementing a custom `atoi` function to convert C-style strings to integers, along with a `main` function for command-line argument parsing. The code uses unsafe FFI patterns and manual memory management.
### Components/Axes
- **Function Definitions**:
- `pub unsafe fn atoi(str: *const c_char) -> i32`: Converts C strings to integers.
- `pub fn main()`: Handles command-line arguments and input validation.
- **Variables**:
- `result`, `sign`, `ptr`: Integer accumulator and pointer variables.
- `c_str`: C string created from command-line input.
- `value`: Parsed integer output.
- **Error Handling**:
- `Ok(cstring) => cstring`
- `Err(_) => "Failed to create CString from input"`
- **Key Constructs**:
- `while *ptr != '\0'`: Null-terminated string traversal.
- `ptr.add(1)`: Pointer arithmetic for character iteration.
- `i32::checked_add(digit)`: Overflow-safe digit accumulation.
### Detailed Analysis
1. **`atoi` Function Logic**:
- Initializes `result = 0` and `sign = 1`.
- Skips leading `+`/`-` characters to determine sign.
- Iterates through digits using pointer arithmetic (`ptr.add(1)`).
- Converts ASCII digits to integers via `digit - '0'`.
- Uses `i32::checked_add` to prevent overflow, returning `i32::MAX`/`MIN` on error.
- Returns `sign * result` after processing all digits.
2. **`main` Function Flow**:
- Collects command-line arguments into `Vec<String>`.
- Validates argument count (requires exactly 2 arguments).
- Prints usage message for invalid input: `"Usage: <number>"`.
- Converts second argument to `CString` with error handling.
- Parses `CString` using `atoi` and prints result.
### Key Observations
- **Unsafe Usage**: The `atoi` function is marked `unsafe` due to direct pointer manipulation and FFI interactions.
- **Manual Parsing**: Implements digit conversion without standard library helpers (e.g., `parse()`).
- **Error Propagation**: Uses Rust's `Result` type for error handling in `CString` creation.
- **Pointer Safety**: Employs `ptr.add(1)` for safe character iteration within bounds-checked loops.
### Interpretation
This code demonstrates Rust's FFI capabilities while emphasizing safety through:
1. **Explicit Error Handling**: All potential failure points (e.g., invalid input, overflow) are explicitly checked.
2. **Memory Safety**: Uses `CString` for owned C-style strings and bounds-checked pointer arithmetic.
3. **Overflow Prevention**: Leverages `i32::checked_add` to avoid integer overflow vulnerabilities.
4. **CLI Integration**: Provides clear usage instructions and input validation for command-line tools.
The implementation highlights Rust's balance between low-level control and memory safety, particularly in systems programming contexts requiring C interoperability.